Trojan.Poison
Trojan.Poison is a horrible Trojan that can cause numerous PC problems. Once downloaded, Trojan.Poison seems to act innocently, however, it fools security programs while combining with damaging software immediately after installing onto the affected PC user's computer. Trojan.Poison is so sophisticated in that its malicious activity doesn't become apparent when its code is directly investigated by security researchers or security software. Trojan.Poison usually functions like a common Trojan downloader. Trojan.Poison can change or add system processes and modify registry entries. Trojan.Poison also changes its task actively via taking down and running x86 commands straight into its own analysis that then makes its devastation. Trojan.Poison may decrease PC and browsing performance and display numerous annoying pop-ups. Remove Trojan.Poison by using an effective malware removal tool.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| TrendMicro | BKDR_POISON.DS |
| Symantec | Backdoor.Trojan |
| Sophos | Troj/Poison-AE |
| Prevx1 | High Risk Worm |
| NOD32 | a variant of Win32/Poison |
| Microsoft | Backdoor:Win32/Poisonivy.H |
| McAfee-GW-Edition | Trojan.Backdoor.Poison.CPD |
| McAfee | BackDoor-DKI.gen.d |
| Kaspersky | Trojan.Win32.Inject.si |
| K7AntiVirus | Trojan.Win32.Inject |
| Ikarus | Virus.Win32.Poison |
| F-Secure | Backdoor:W32/PoisonIvy.gen!A |
| eTrust-Vet | Win32/PoisonIvy!generic |
| Comodo | Backdoor.Win32.PoisonIvy.Gen |
| ClamAV | Trojan.Downloader-24465 |
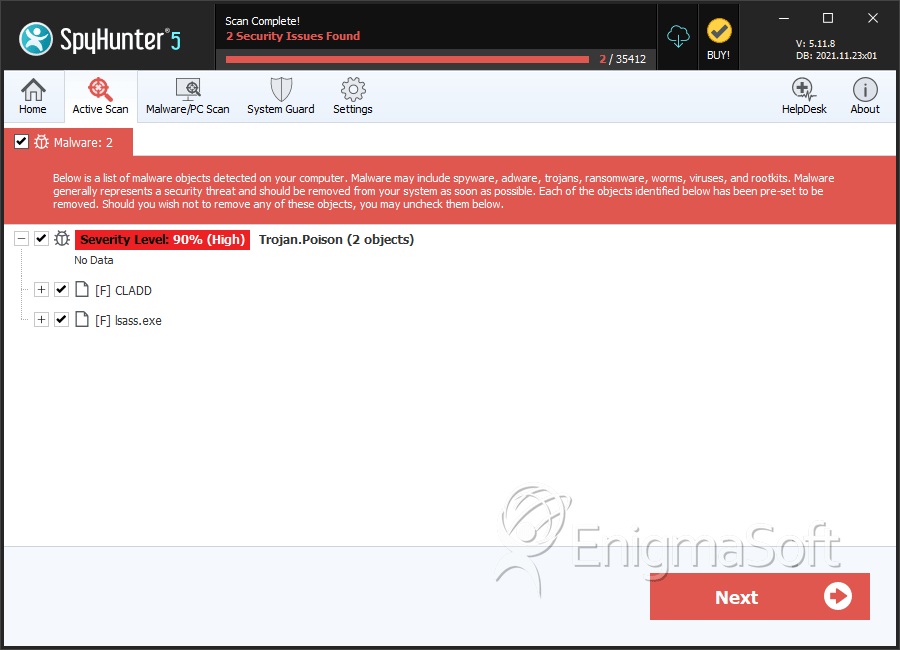
SpyHunter Detects & Remove Trojan.Poison
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | CLADD | bed8b95ace8e29bea18c0178f33211f6 | 0 |
| 2. | lsass.exe | 6ff75b1f5feef8bcb08ff1290220b17b | 0 |
Registry Details
Analysis Report
General information
| Family Name: | Backdoor.Poison |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
5f1efd3aebead612dc47d2475fc247c6
SHA1:
049a56340061a68c2203c6bcdb27eb6111b1fc1e
SHA256:
85E617A9A0749F29FD34A92FED51F960AF95BC40F2B334AABBD3CC18B7455389
File Size:
17.41 KB, 17408 bytes
|
|
MD5:
4cb58f0597ee299c8a4534ec16316f17
SHA1:
0384393ffea7b251c800c211353fae05c1125a49
SHA256:
ADBB078620A3CBD6C22AC266C3B6E4E2ACFB21CA5A8BEF43B383BAC801A10338
File Size:
17.41 KB, 17408 bytes
|
|
MD5:
3c3a2e542435b2e9593bdcc9b40f9253
SHA1:
302ad1d90ee1a8dce5e5e7e0e2add781bff09d83
SHA256:
A8FE37145DFEEF98C83A921A41DCCC908601DCC821B60D9AD8590F52A97DAE63
File Size:
17.41 KB, 17408 bytes
|
|
MD5:
a2f9307f55281dce75c0dd8b5cb1df9a
SHA1:
f2c4a95dde951651601e85d3d4662332e5ef67e4
SHA256:
AD69B4D31A6687FD3DA01D129377FC5559AA7035746F0C4E4E3D9B841E74C270
File Size:
17.41 KB, 17408 bytes
|
|
MD5:
f9ecb4cb4dac6cc85f63099798d7f4ca
SHA1:
4d402e23232f08264eed3b1de48e5a4411210a1b
SHA256:
767F704AB002710DF1D77B3A4819BCB82D16D2D44DB0AF056D94E76B44AFD2B8
File Size:
17.41 KB, 17408 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have resources
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- No Version Info
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 20 |
|---|---|
| Potentially Malicious Blocks: | 1 |
| Whitelisted Blocks: | 19 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Ardamax.K
- MSIL.Krypt.YBAB
