Trojan.Pazzky.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
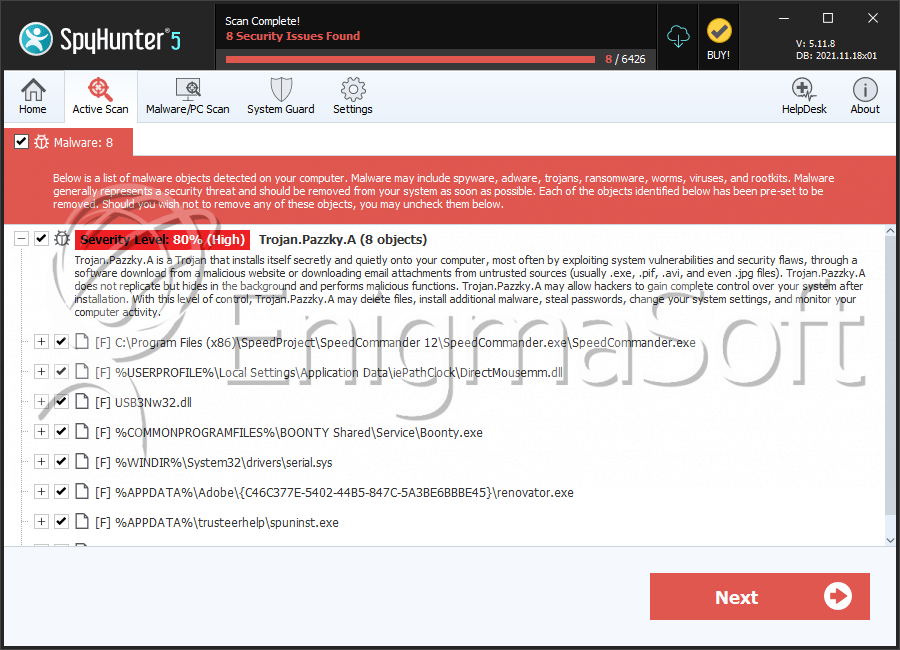
| Threat Level: | 80 % (High) |
| Infected Computers: | 333 |
| First Seen: | January 13, 2012 |
| Last Seen: | February 1, 2026 |
| OS(es) Affected: | Windows |
Trojan.Pazzky.A is a computer Trojan that encompasses numerous bad characteristics. Trojan.Pazzky.A can slow down your PC. The main task of Trojan.Pazzky.A is to distribute an adware application and collect personal details about the affected user's Internet surfing habits. When installed, Trojan.Pazzky.A modifies the Windows Registry so that it can launch automatically whenever you turn your PC on. Trojan.Pazzky.A can install itself into the compromised web browser to take over search results from search systems. Trojan.Pazzky.A can reroute you unwillingly to doubtful web pages. Trojan.Pazzky.A can easily connect to the web and add many infectious files. Delete Trojan.Pazzky.A as early as possible to avoid system harm.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| AVG | Generic25.OKM |
| Fortinet | W32/Malware_fam.NB |
| Ikarus | Trojan.Win32.Pazzky |
| AntiVir | TR/Pazzky.A.1 |
| Avast | Win32:Dropper-gen [Drp] |
| McAfee | Generic.dx!bbdz |
| Sunbelt | VIPRE.Suspicious |
| Prevx1 | Heuristic: Suspicious File With Code Injection Tec |
| F-Prot | W32/Heuristic-162!Eldorado |
| McAfee | Artemis!FF269F2507EA |
| Sophos | Sus/ComPack-C |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Obfuscated.C |
| F-Secure | Suspicious:W32/Malware!Gemini |
| Comodo | Heur.Pck.tElock |
| GData | Win32:Rootkit-gen |
SpyHunter Detects & Remove Trojan.Pazzky.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | SpeedCommander.exe | c8bd3b7f0ad3b7a90bec90001c70932b | 189 |
| 2. | DirectMousemm.dll | 5f65fff31827d9b4f9632abaac917f42 | 39 |
| 3. | USB3Nw32.dll | a6d8fc2c9b1a852941f35c16aadb2d9a | 13 |
| 4. | Boonty.exe | bce06856c6601986bf5d85c5059a89a4 | 11 |
| 5. | ComboFix.exe | fa033f4c11bac43857d729afa1b55a3d | 4 |
| 6. | serial.sys | 6d2767d8137d68b2663aa388d76b36fd | 4 |
| 7. | renovator.exe | 5ca07dbf5c021d3f541e6620e1a42234 | 4 |
| 8. | spuninst.exe | 639ed5465e3df5b0b68d786d4e046fb7 | 3 |
| 9. | afd.sys | 504e5d7269e8c9537a54010a12ab180c | 3 |
| 10. | xrhqef.dll | ae9616117607aed17f84a5e94abc972c | 3 |
| 11. | ZKX2VTNL87999.exe | 57bec70d7f961b32ab750aedcdc1d99b | 2 |
| 12. | smb.sys | d5b6fccf511951335e2217a6f6c24a8f | 2 |
| 13. | windowslogn.exe | 7954124072d0d246469d53ca12912bb9 | 2 |
| 14. | chdc.exe | de615d964a45dca9b887bfc515765bab | 1 |
| 15. | 9a985b2d.dll | c9a55a9620c9544bd34d1bb38bf482c6 | 1 |
