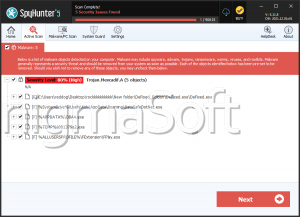
Trojan.MSIL.Webshell.DG
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 9,376 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 21 |
| First Seen: | October 7, 2024 |
| Last Seen: | May 2, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.MSIL.Webshell.DG |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
163c19ce144d18b74dcd1b81c5cd82f9
SHA1:
275de706164c54175bd0f2758c7434d30fe5acf0
SHA256:
0745AFEB2ED410334D0DE49EDEA400437FB49ECD69807395B4C5B46CD23CAAAF
File Size:
307.20 KB, 307200 bytes
|
|
MD5:
8483cf65d6a103e851a6b3c05552a2c0
SHA1:
fbf9f210a49b47003603d5e74fb645966eb1b57d
SHA256:
CDBEF376EA39F07961C03117FB3F32F3F760E0EC59AECC577681049712C48DDF
File Size:
284.16 KB, 284160 bytes
|
|
MD5:
a19ca1ccace7a7fc76e2e435c41d89e1
SHA1:
64b17d2fa779c34bd81d14f8cb6c00f9df60d977
SHA256:
716DB9DD28D5ADBEA025BAB6FBD2D5F0D6B557D2FEF1D42A2321023AF94A570E
File Size:
171.01 KB, 171008 bytes
|
|
MD5:
2607419778b19fe7d162feefa616c42f
SHA1:
a3f9cd24859fae2d156b279d5b03a64e509562d7
SHA256:
7EE604265A79ED3A74CAD8219827BBBBFBB6CA5F520FB93D8B54EFBDBE1213D6
File Size:
247.81 KB, 247808 bytes
|
|
MD5:
3ab111a3aea0cb1b5d8b7e6722883435
SHA1:
a4fa2db42a99bf2210dd20911670f10ef8fa9663
SHA256:
545BDB3068CB87AC9F71C120A47FAFD8B45C2F1E48E7A20CDA2C6D9B9CAD7579
File Size:
302.59 KB, 302592 bytes
|
Show More
|
MD5:
abd68537a67cab965f1447758f39f1f4
SHA1:
18634f3111904a019c8a3179fbd74cd450c9b814
SHA256:
F37FC6D93DEB2809CC35692DBA7158632C390ADD111F3C2C632C409376F4951A
File Size:
208.38 KB, 208384 bytes
|
|
MD5:
634d76b10bbe607f3efe180ab5b658eb
SHA1:
9b904fd819c5c80a7c766c45863bb68a0b230a89
SHA256:
454135E82C8135CBB21547D4404E6A3E3D9E8E8A9D51BC076958982B966CFF50
File Size:
190.98 KB, 190976 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File is .NET application
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- .NET
- dll
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 547 |
|---|---|
| Potentially Malicious Blocks: | 152 |
| Whitelisted Blocks: | 61 |
| Unknown Blocks: | 334 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|