Trojan.MSIL.Mardom.AC
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
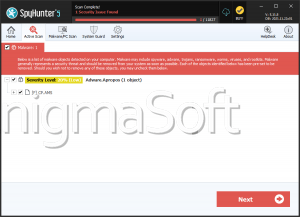
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 14,940 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 53 |
| First Seen: | March 29, 2024 |
| Last Seen: | January 26, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.MSIL.Mardom.AC |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
eb8c12813321d6e535e58b01e362d91d
SHA1:
816d3662f2a2272215d7c809f1b840218c5f001e
SHA256:
A8D7C17BA62EEB4833ACD468C236FD457552D8DCED3AB6527186B4362F603892
File Size:
5.95 MB, 5949952 bytes
|
|
MD5:
61aae84c72353034cf75434ee5cc89a1
SHA1:
2be952be7326b40406a1956b5cdfc55883a03cb7
SHA256:
779A69FC06DFEB02A7D28483F815215EAB22D619B50DC8E8AE06BDEC6054F03D
File Size:
5.00 MB, 4999168 bytes
|
|
MD5:
150764ce79f722be5f33d4d673aad09e
SHA1:
0cca52cafbde869c61047c56413471b5a27e0497
SHA256:
18F1F75BBB2120A2629662E60A4FDAD118F2039216574A5D29D91D25DC2650C0
File Size:
5.34 MB, 5337088 bytes
|
|
MD5:
0b0fba8e7ed863be3882b4ed348c88f1
SHA1:
4db3db8651e977231315d0718e6c30bc9581f0a3
SHA256:
BCE780AB670F1BE5C6A80FCB86324CED49A34D7E6ADECCCE0FB059FDC8398FE4
File Size:
5.17 MB, 5166592 bytes
|
|
MD5:
ae6e47ea84c56690671f0c64cf45f096
SHA1:
3857e6290639887268abc5c5eafdbb3ef85147e8
SHA256:
066A2BEC38E25EB17CBF695DCF7A8D1EC8CEC1708622EB4FC71803EAA8D18BE5
File Size:
5.13 MB, 5126656 bytes
|
Show More
|
MD5:
1c47f019dc4687e5e329d55213b5dbea
SHA1:
9f23db24ccc37359e562434a7d69355c23a6097f
SHA256:
F3A5945FB4F3515CEB5E4995CA819EE78A5A8302B985A62247EB5E94A3860FD3
File Size:
4.44 MB, 4435456 bytes
|
|
MD5:
96613cb84d5f23248d726e5e4cd36eca
SHA1:
00580630544fc031675ea4fa1d79e2ca5b7d0ae9
SHA256:
31429F8AEB42DFC8D16A212BAB73D68ECC3085FE64735043BF1773486928C74A
File Size:
5.95 MB, 5949952 bytes
|
|
MD5:
8d3a732a23c769b87810e75e4b349a7b
SHA1:
159860433fe69c0b2f0d3730cf98cd2c4043e32e
SHA256:
4BFF99435878080A8E435B3135FB284BE29DB2EF12773C071D59B4EFB75E91EB
File Size:
5.05 MB, 5048320 bytes
|
|
MD5:
84261cb063e1dc90bee07b8466dc98ca
SHA1:
752385dfea0166d02311805b89649e2efc3e8fb0
SHA256:
4DCCB91ECEF296F414EEECF33CC882F408318058CBE24A2E2D0B6CCF0E490ECD
File Size:
4.86 MB, 4855296 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is .NET application
- File is 64-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Version |
|
File Traits
- .NET
- Agile.net
- Confuser
- Fody
- HighEntropy
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 665 |
|---|---|
| Potentially Malicious Blocks: | 222 |
| Whitelisted Blocks: | 416 |
| Unknown Blocks: | 27 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- MSIL.Mardom.AC
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| User Data Access |
|
| Anti Debug |
|