Trojan.Injector.XC
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
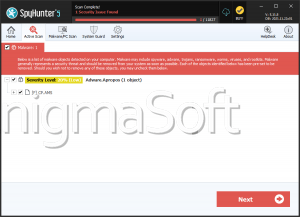
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 4,056 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 124 |
| First Seen: | April 26, 2024 |
| Last Seen: | January 26, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Injector.XC |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
9f194f680b3f39d56a8908424add3d3e
SHA1:
e83112e235326d9757b82f0ea40d2f87bb877fd5
SHA256:
C7D6B87D3B04B6A96D68F574A84E7DD41006FE56057D8B2045A15791947215FC
File Size:
2.53 MB, 2529280 bytes
|
|
MD5:
743d5c03aa3d1ea2320e018cb938a047
SHA1:
9bcede59416e800a20da15b53732c2bca66c5ea2
SHA256:
959A98E0221D3731FB1685192E4559AE42CE59F7D80267C3D94BB752684B4DFE
File Size:
38.91 KB, 38912 bytes
|
|
MD5:
45444160efad31767d709a46740b6620
SHA1:
121e1ba87d3e2083d3a94e270e407370f5629612
SHA256:
722EC6431E14035A14C4A214FB50543A3032F2673FDB0B665057807FC47255E1
File Size:
4.95 MB, 4948480 bytes
|
|
MD5:
eea9212f2da936f215e40278d2751c6e
SHA1:
660a5c501d8644f58c8d5c813d3c02ca15dc0607
SHA256:
972C4F6E2786A42D89CDEB26517BD57DCA2E55694F5CBA6ED2757D5A6449502C
File Size:
2.52 MB, 2521600 bytes
|
|
MD5:
ea3471ef886ea262a668a4e5d5171c8c
SHA1:
4b8f3b861b3cc2376d052920757f4fbaa56597d5
SHA256:
5A78446678280DF7E3B9222863AEDEF96897D423C38D15698C706BB18ACD5520
File Size:
3.92 MB, 3920384 bytes
|
Show More
|
MD5:
462636fab8acd4378fd6b8724a828233
SHA1:
f995a1a8c5c84eba96edcd9a12f92351ba702a13
SHA256:
2DB6B108FA77805B4DB2419ECF2E2633353DE52852A20232498BAA434E580418
File Size:
611.33 KB, 611328 bytes
|
|
MD5:
bc0822b3b1dea07435b913af86faf6d5
SHA1:
3b4af1c7d5f5b0adef00547dbe82c054e2790391
SHA256:
A80B47388BB9FDF937194DF76309A2773076725196BA33AA068CD3D1EC4C65E9
File Size:
2.63 MB, 2627584 bytes
|
|
MD5:
48a6c579ac932ca8c61d27e7132115b6
SHA1:
cc6011d1bf3b227c6e672ca2407767c5d0c886da
SHA256:
82276B0D2727BEFF47911903E1B50844A1E8497FB0EA5AA5EE7761ED1D0C166C
File Size:
1.02 MB, 1015296 bytes
|
|
MD5:
b544743df1b88e320312cdaa401d76f2
SHA1:
d17f83e49e495e306c9c46fa8e0bdb514ef9fac6
SHA256:
C4B1670877C6221B603DCEBC120963684B8BB57F97BB8CEDC27FB7514ACC289E
File Size:
169.98 KB, 169984 bytes
|
|
MD5:
afe7530809661930e805aecad0fb70e0
SHA1:
b925a8ce524b149d241fe66c7497308a232c85fa
SHA256:
AC6D91574C421F42BF053F4EF2F10861BEBC2F1485795533001753E2B9E765A4
File Size:
877.06 KB, 877056 bytes
|
|
MD5:
2158879284ac6e54b0e2cf2b48a10e07
SHA1:
e562ded9b6fbe5119837b1d91c6c1be92a85a848
SHA256:
38FF239C91E49AE4E6020F01E5BACE608E4EE65A72C2FFCA558819CA0AE06EAF
File Size:
877.57 KB, 877568 bytes
|
|
MD5:
e69628e8c87a52ff37811965684e79b5
SHA1:
97f5e78b6a163d05501cb5b2039036639e978311
SHA256:
A99F604A5FF74B708A809C42181778F3B2859FB0431E2D0B8122F1210DC2B80A
File Size:
606.72 KB, 606720 bytes
|
|
MD5:
936b99866ba7267adbe6e5b1bb45122e
SHA1:
4a89d39cc6604de8b6fce4a23ff18c7c157a47cc
SHA256:
B4DD72620721F57BE6924CC69E278BA7A2946DE7346C897918E50B14C4C516A8
File Size:
448.51 KB, 448512 bytes
|
|
MD5:
24f92a8b0930b9405c93650daf369168
SHA1:
ac1530429c91ded59b46833278a2af64ff6a7a16
SHA256:
7ABB92855D845C974820EF4FD49434735AAC65986AF1CF092168A9FE01D90BF3
File Size:
278.53 KB, 278528 bytes
|
|
MD5:
2e01ad17fb35257b3ed966aac3e7fd96
SHA1:
40ac9b9e5d5751b51e9b4a812433576261afc557
SHA256:
41CE538080AA8F0717368B70BD0CAF894CF8FECAC5A27D634CC7AB6BB6D5537A
File Size:
610.82 KB, 610816 bytes
|
|
MD5:
83100b6058dbb46b9e56de65e2003ef1
SHA1:
2d07d55c74bf62581b3fe6edfccbd031fe3f2a3b
SHA256:
15D15886D0C7CDEF0DE30263E94EA8FB33CD353B5783CC4BF75B738EC544A86E
File Size:
325.12 KB, 325120 bytes
|
|
MD5:
260ecfc4d9a901321d7547d1584e6ca9
SHA1:
8ff3b88aeed45d8da8f7199d5b7c3ca762e2b0a2
SHA256:
4B6D4D54834A89A586BB1EA505DD7B7BD0E9D3A86BAD1A070F157B4792F83525
File Size:
166.91 KB, 166912 bytes
|
|
MD5:
fb17f4da1132739ab9cc037ab025c0c0
SHA1:
1626aa1293e7e075573e69dccf84800df9637354
SHA256:
0F2ABC1D03741E72A35A0829261F5E0D6ED36D46A42B4E2E0B09AA20B3ABC08C
File Size:
26.93 KB, 26925 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have resources
- File doesn't have security information
- File has exports table
- File has TLS information
- File is .NET application
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
Show More
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 1.0.0.0 |
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- dll
- HighEntropy
- imgui
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 36 |
|---|---|
| Potentially Malicious Blocks: | 2 |
| Whitelisted Blocks: | 34 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Injector.XC
- Trojan.Injector.Gen.CQK
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\downloads\d17f83e49e495e306c9c46fa8e0bdb514ef9fac6_0000169984.json | Generic Write,Read Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
3 additional items are not displayed above. |
| Process Shell Execute |
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\9bcede59416e800a20da15b53732c2bca66c5ea2_0000038912.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\f995a1a8c5c84eba96edcd9a12f92351ba702a13_0000611328.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\d17f83e49e495e306c9c46fa8e0bdb514ef9fac6_0000169984.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\97f5e78b6a163d05501cb5b2039036639e978311_0000606720.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\4a89d39cc6604de8b6fce4a23ff18c7c157a47cc_0000448512.,LiQMAxHB
|
Show More
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\ac1530429c91ded59b46833278a2af64ff6a7a16_0000278528.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\40ac9b9e5d5751b51e9b4a812433576261afc557_0000610816.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2d07d55c74bf62581b3fe6edfccbd031fe3f2a3b_0000325120.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\8ff3b88aeed45d8da8f7199d5b7c3ca762e2b0a2_0000166912.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\1626aa1293e7e075573e69dccf84800df9637354_0000026925.,LiQMAxHB
|