Trojan.Gen.2
Trojan.Gen.2 is a dangerous computer trojan that may represent security risk for the affected PC system and its network environment. Trojan.Gen.2 may try to establish connection with the remote host once it has infiltrated a computer system. Trojan.Gen.2 can aslo request other files from the Internet to the corrupted computer system. Trojan.Gen.2 often infects computer systems without your authorization at the background. Trojan.Gen.2 enables cyber-criminals to remotely access an influenced computer system. Trojan.Gen.2 can proliferate via network if the infected drive is shared at the network.
Table of Contents
Aliases
7 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Symantec | Trojan Horse |
| Panda | Trj/Refpron.J |
| McAfee-GW-Edition | Trojan.Downloader.Gen2 |
| McAfee+Artemis | Artemis!0A77CA4058B3 |
| Ikarus | Backdoor.Win32.Refpron |
| Avast | BV:Malware-gen |
| AntiVir | TR/Downloader.Gen2 |
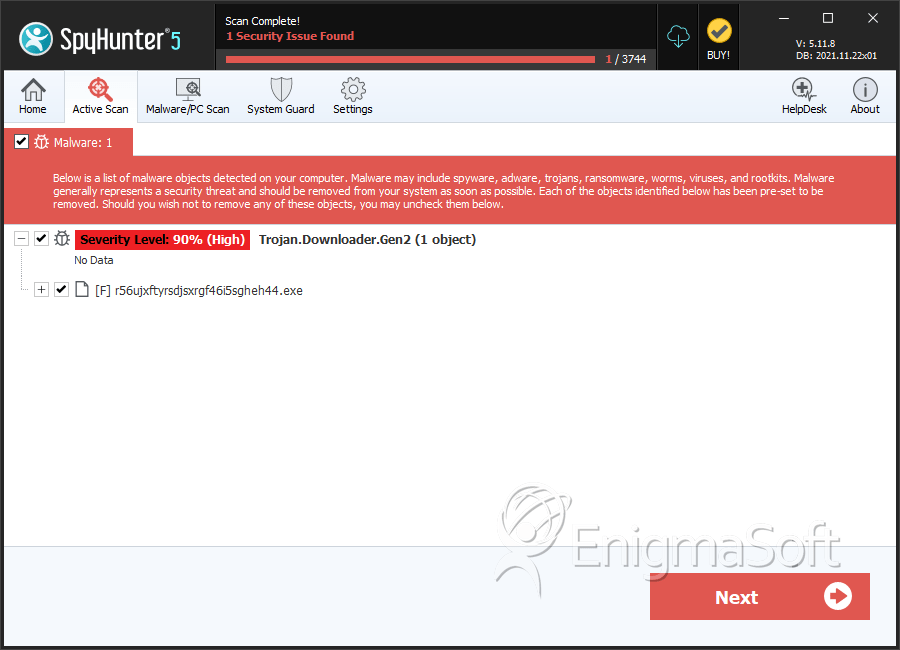
SpyHunter Detects & Remove Trojan.Gen.2
File System Details
Trojan.Gen.2 may create the following file(s):
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %System%\arking2.dll | ||
| 2. | %System%\arking1.dll | ||
| 3. | %System%\arking0.dll | ||
| 4. | %System%\arking.exe | ||
| 5. | r56ujxftyrsdjsxrgf46i5sgheh44.exe | 0ae9a1e5a7ddaf6222954d307edc2ae3 | 0 |
Registry Details
Trojan.Gen.2 may create the following registry entry or registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\MADOWN
HKEY_LOCAL_MACHINE\Software\Trojan.Gen.2


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.