Trojan.Foxhiex
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
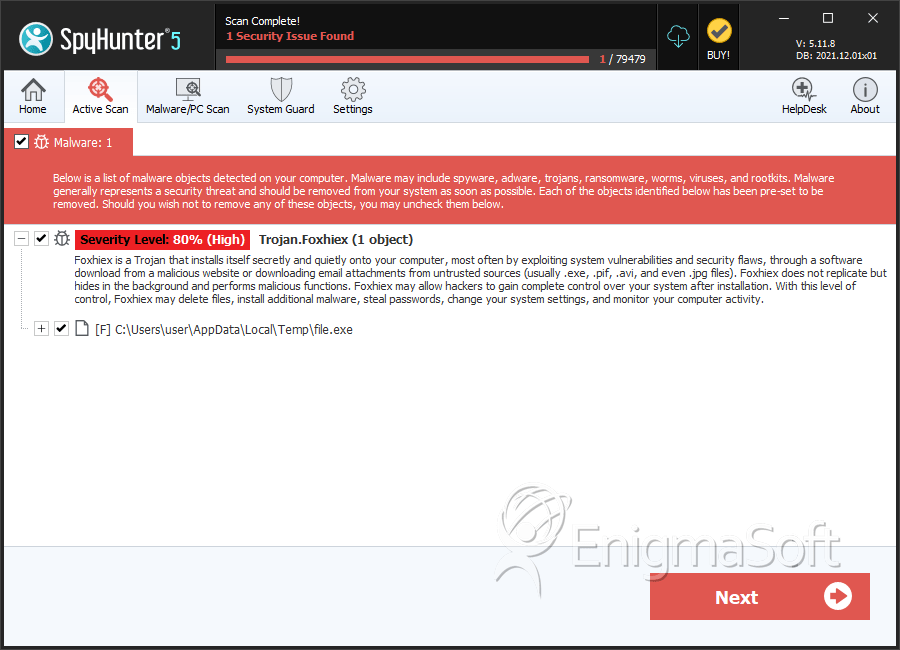
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 79 |
| First Seen: | January 24, 2018 |
| Last Seen: | February 4, 2022 |
| OS(es) Affected: | Windows |
Trojan.Foxhiex is a general detection name used by cybersecurity vendors referring to a Computer Trojan distributed via malvertising (corrupted ads). Attackers associated with the Foxhiex have been observed to use advertisements published on sites with pornographic content and redirect users to unsafe URLs. Loading the bad links triggers the download of an encrypted file along with a JS file, which decrypts the threat payload and loads it into the system memory. Trojan.Foxhiex is used by cybercrooks to send waves of spam emails and facilitate the distribution of other threats.
PC users infected with Trojan.Foxhiex may not notice its presence considering the threat requires minimal system resources to run and does not slow down the machine. The Foxhiex Trojan might be spotted by experienced network experts since the threat performs multiple connections to various email services. The data sent out by the Foxhiex Trojan is relayed via the standard port 8080 using a hidden instance of Internet Explorer. Computer security researchers reported that the Foxhiex Trojan might create the following directories:
C:\Users\username\Application Data\
C:\Users\username\MetaData\
C:\Users\username\Microsoft\Crypto
C:\Users\username\datawork\
The executable that have been used by Trojan.Foxhiex include:
6239.exe
Hype Rat Beta.exe
Whilling.exe
aaaa.exe
ghetto.exe
The Trojan.Foxhiex may inject code into the host process in Windows — svchost.exe to avoid detection. The primary executable for the Foxhiex Trojan might be stored in protected folders and guarded memory blocks on the system drive. It is recommended to remove Trojan.Foxhiex with the help of a trusted anti-malware product. AV companies are using the following detection names to tag variants of the Foxhiex Trojan:
- Backdoor.Breut
- PWSZbot-FABL!91B6826CEFA7
- Troj/MSIL-VZ
- Gen:Variant.Kazy.363616
- Troj_Foxhiex.kh
- Trojan ( 004987c81 )
- Trojan.Win32.Foxhiex.buq
- Trojan/Foxhiex.aq
- W32/Foxhiex.AEQ!tr
- MSIL:Injector-IZ [Cryp]
- Win.Trojan.Agent-737491
- TROJ_GEN.R0CBC0PFJ14
Table of Contents
SpyHunter Detects & Remove Trojan.Foxhiex
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 8dc681c56027f5fb3fc3bd13568ee65c | 1 |

