Trojan.EvilBunny
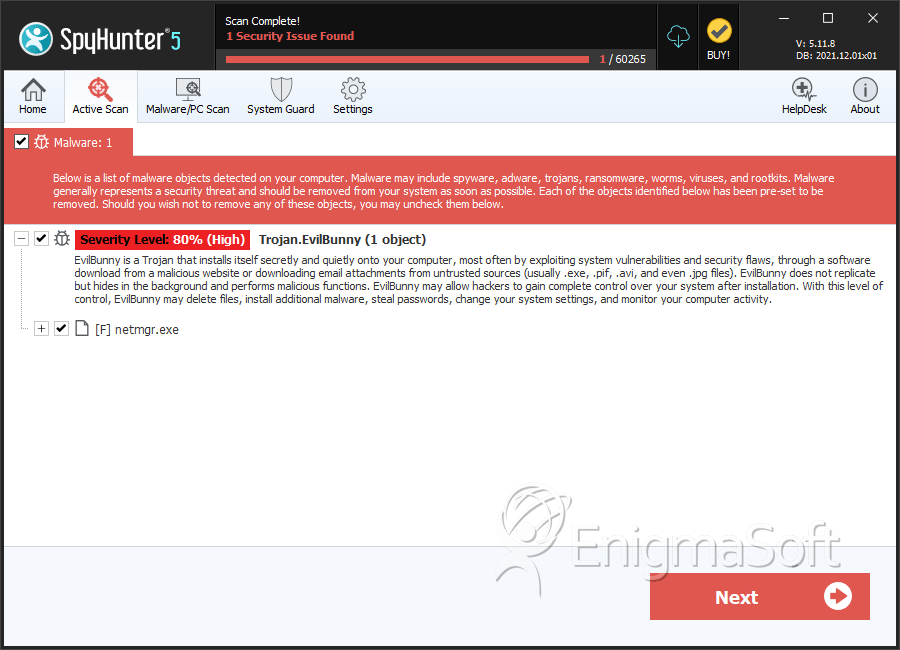
Trojan.EvilBunny is a detection used by security vendors when discussing a backdoor Trojan. The Trojan.EvilBunny threat is placed in the category of backdoor Trojans because of its functionality. Trojan.EvilBunny is introduced to computers by hacking them manually and using phishing emails. Once Trojan.EvilBunny is installed, it would make modifications to the OS that would grant a third-party access to the machine. Trojan.EvilBunny is programmed to create an access point by running a file named 'netmgr.exe' that is placed in the MSapps folder under the Windows directory on the primary system drive. The program is added to the list of programs that Windows OS loads during bootup by adding the following key to the Registry:
'HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\"netmgr" = "%Windir%\msapps\netmgr.exe."
The EvilBunny Trojan can be customized with commands sent remotely. Trojan.EvilBunny uses configuration files to operate and implement updates. PC security researchers note that the EvilBunny Trojan supports a file transfer protocol and can be used to extract data from the compromised machine, as well as retrieve files from a remote server. Network analysis on the connections initiated by Trojan.EvilBunny revealed that the threat might upload and download data from the following domains:
- http[:]//le-progres.net/images/php/test[RANDOM CHARACTERS]
- http[:]//ghatreh.com/skins/php/test[RANDOM CHARACTERS]
- http[:]//www.usthb-dz.org/includes/php/test[RANDOM CHARACTERS]
Moreover, an in-depth analysis of Trojan.EvilBunny shows that the threat can access information stored in your browser. Samples of EvilBunny suggest that the Trojans can read information like saved usernames and passwords in Internet Explorer and Mozilla Firefox. PC users affected by Trojan.EvilBunny may not find evidence of its infiltration immediately and may notice that the files in the folders are missing and accounts on the Web are signed out. If you suspect Trojan.EvilBunny is on your computer it is recommended that you scan your OS with a trustworthy anti-malware scanner that can detect and eliminate Trojan.EvilBunny. AV vendors may use the names TROJ_BUNEVIL.A and Trojan-Dropper.Win32.Daws.chp when talking about Trojan.EvilBunny too.
SpyHunter Detects & Remove Trojan.EvilBunny
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | netmgr.exe | 3bbb59afdf9bda4ffdc644d9d51c53e7 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.