Trojan.Delf.S
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
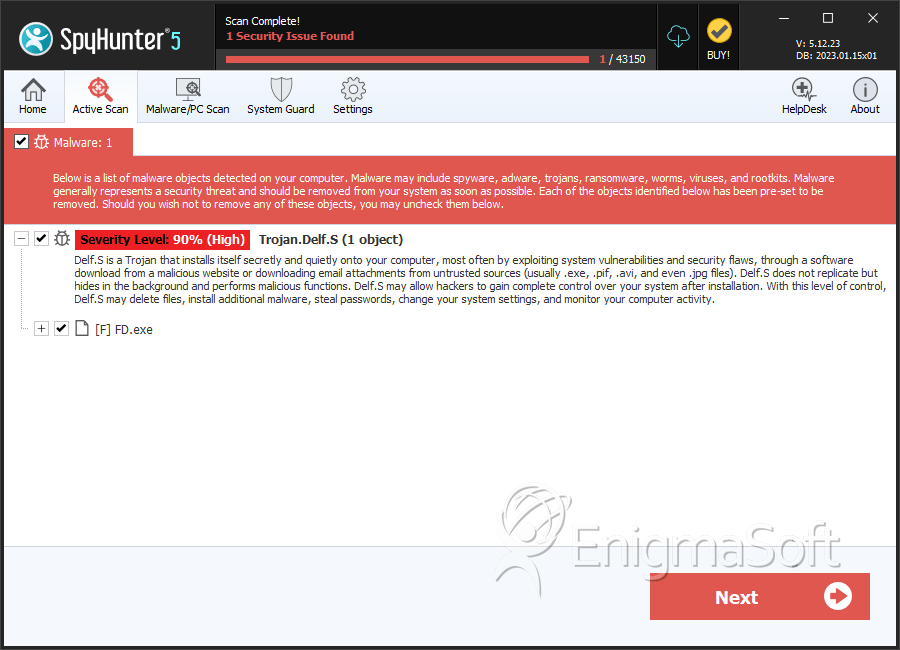
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 7,228 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 73 |
| First Seen: | July 24, 2009 |
| Last Seen: | October 1, 2025 |
| OS(es) Affected: | Windows |
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Panda | Trj/Downloader.MDW |
| NOD32 | probably a variant of Win32/TrojanDownloader.Delf |
| McAfee-GW-Edition | Trojan.Dldr.Delf.njq.1 |
| McAfee | Generic Downloader.x |
| Ikarus | Trojan-Downloader.Win32.Delf |
| F-Secure | Trojan-Downloader.Win32.Delf.njq |
| eSafe | Suspicious File |
| Comodo | TrojWare.Win32.TrojanDownloader.Delf.njq |
| BitDefender | Trojan.Generic.892770 |
| AVG | Downloader.Generic7.ANSL |
| Avast | Win32:Trojan-gen {Other} |
| Authentium | W32/Downldr2.EILE |
| Antiy-AVL | Trojan/Win32.Delf |
| AntiVir | TR/Dldr.Delf.njq.1 |
| AhnLab-V3 | Win-Trojan/Xema.variant |
SpyHunter Detects & Remove Trojan.Delf.S
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | FD.exe | 5fcfa14bdfcd3d202225c826cf905143 | 0 |
Analysis Report
General information
| Family Name: | Trojan.Delf.S |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
ae0dd3bb91186b27fa713ecabe10e4c7
SHA1:
6bf70bd55296ea42234d428e8a169c00847ec8a1
SHA256:
7FC0ABDFFA6B2DD1C68676CDEB711DFD39C902C9DF6ABFDB009FC5F237C863F9
File Size:
53.63 KB, 53632 bytes
|
|
MD5:
59c52b086ed72faffb65bc1d0cce96e6
SHA1:
046a941244f3f25f6c4da477235d60f42c57b11b
SHA256:
9FF10628061DE9F7599779FCEB4857C4EDB067CDFCCA2154592DAE25F3A5EE55
File Size:
62.98 KB, 62976 bytes
|
|
MD5:
2c9d2f9e6a758bfd92b241cc29ba5eed
SHA1:
c40fd1ac44f565453d35ec6ea1cf88f373a2f9df
SHA256:
58DCCD806B88CF3F2759A27FFB7CDC3E66564404F16703E43AB0D735E2414DB4
File Size:
5.60 MB, 5595813 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | Packed with Paquet Builder, see http://www.gdgsoft.com |
| Company Name | DJ, dj@oldgames.sk |
| File Description |
|
| File Version |
|
| Legal Copyright |
|
| Product Name |
|
| Product Version |
|
| Web | http://www.oldgames.sk |
File Traits
- Installer Manifest
- Installer Version
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\pb4ac0.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |

