Trojan.Delf.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
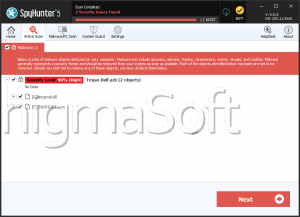
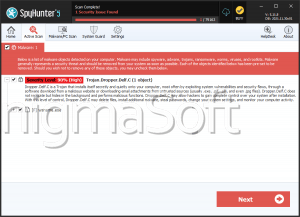
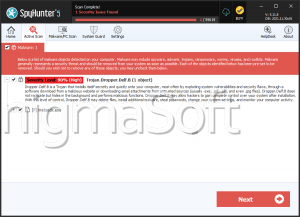
| Popularity Rank: | 9,498 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 3,100 |
| First Seen: | April 27, 2017 |
| Last Seen: | November 6, 2025 |
| OS(es) Affected: | Windows |
A Trojan belongs to the category of high-profile threats because it can pretend to be a necessary application and convince computer users to install it on their machines willingly or it can be bundled with a program the users download from unchecked sources. Trojan.Win32.Delf is one of these misleading programs that once inside a computer, will try to gain administrator access so that it can take control of the machine and start installing its threatening files.
Although sometimes it is not easy to notice the presence of Trojan.Win32.Delf on a computer, if the users notice unwanted Web activities, the machine becoming irresponsive, changes to the Registry or browser setting or any other event out of normal, it is time to use a trusted anti-malware scanner. The malware scanner can detect the presence of Trojan.Win32.Delf as well as its files and remove it from the affected machine securely.
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Delf.A |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
f5e75624592210aa2be9d25a3a4b8b76
SHA1:
6be55ff170ef6797b9dfc0a4c502e57a3ca8299c
SHA256:
C11E90252ED02E5C1F64C2E7195FE4C8023673B8CF722CCB310971EEEA78455A
File Size:
2.99 MB, 2992665 bytes
|
|
MD5:
5249b7f3557cadbf6372525bdd2a92a8
SHA1:
475b08166edaf838c104b26c7f9480225ecc6095
SHA256:
074B94A323EF0A5E7AAB7AFC414669CD6AB1AD60B908C04F64B58037C2251B1E
File Size:
3.30 MB, 3299862 bytes
|
|
MD5:
60f3da3789d6132cf588bf3d5c9055e8
SHA1:
342c50bc3a74c7707cba35f5b13a42d8cce5d98d
SHA256:
FFD0EB3BBC646FDFBB064D82DF8630C976D80649FF0A1FE5F3457DB412E45D36
File Size:
2.99 MB, 2992665 bytes
|
|
MD5:
ceec861babdca3b3a2c1952cf8139733
SHA1:
da8882f914f9af77b50792ffc0f09df59f4a2046
SHA256:
CB90E242533F251EE062C00C086BDF56038BFF444134FEADEBB8C92C151893E3
File Size:
2.99 MB, 2992665 bytes
|
|
MD5:
aba4f592c6999ba2d87c194878f36423
SHA1:
a2ac4a76795d032adf2ecab5ec92a151d08a7930
SHA256:
49B1DE2637A790D4D9CC53968FFC9F5F386A21A95A58017A9F38D4923020461C
File Size:
3.11 MB, 3106474 bytes
|
Show More
|
MD5:
def4af4acf1b642cd01f7a287141b535
SHA1:
9bd46a84b2f14415ebc7e101420b8aac6798ba6b
SHA256:
F81249A92B6AE1769A56E9B621BF13957CC3F91550E59F31D9C338B460EBDB5A
File Size:
3.30 MB, 3299862 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| File Version | 1.0.0.0 |
| Product Version | 1.0.0.0 |
File Traits
- 2+ executable sections
- big overlay
- MZ (In Overlay)
- VirtualQueryEx
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 7,993 |
|---|---|
| Potentially Malicious Blocks: | 126 |
| Whitelisted Blocks: | 7,867 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Bancteian.B
- Banker.FD
- Injector.JDA
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\rcx1187.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\rcx39d0.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\svchost.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\svchost.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
| c:\users\user\appdata\local\svchost.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\svchost.exe | Synchronize,Write Data |
| c:\users\user\appdata\local\temp\icsys.ico | Generic Write,Read Attributes |
| c:\users\user\appdata\roaming\rcx11a8.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\roaming\rcx3a00.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\roaming\spoolsv.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Show More
| c:\users\user\appdata\roaming\spoolsv.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
| c:\users\user\appdata\roaming\spoolsv.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\roaming\spoolsv.exe | Synchronize,Write Data |
| c:\windows\rcx1167.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\windows\rcx39b0.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\windows\wininit.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\windows\wininit.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
| c:\windows\wininit.exe | Synchronize,Write Attributes |
| c:\windows\wininit.exe | Synchronize,Write Data |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\microsoft\windows\currentversion\policies\system::consentpromptbehavioradmin | RegNtPreCreateKey | |
| HKLM\software\microsoft\windows\currentversion\policies\system::enablelua | RegNtPreCreateKey | |
| HKLM\software\microsoft\windows\currentversion\policies\system::promptonsecuredesktop | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| User Data Access |
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
c:\windows\wininit.exe
|
c:\users\jlgdnptl\appdata\local\svchost.exe
|
c:\users\fmxdrkkj\appdata\local\svchost.exe
|