Trojan.Comronki!rts
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 12 |
| First Seen: | November 30, 2010 |
| Last Seen: | April 22, 2021 |
| OS(es) Affected: | Windows |
Trojan.Comronkirts, a malicious program, may not sound generic but actually Trojan.Comronkirts is. ESG's security researchers noted Trojan.Comronkirts was a chameleon of sorts, mutating or changing its names and filenames to switch up its behavior and combat the security programs that are trying to remove it.
Trojan.Comronkirts targets systems running Windows OS and has frail or non-existent protection in place. Trojan.Comronkirts travels by way of exploits in software, hardware or human behavior, which is why it is crucial to exercise good Internet security habits, such as:
- Avoiding piracy.
- Avoiding click on dubious or sensationalized links or attachments in emails, social network environments or on Google search results pages.
- Being cautious when web surfing.
- Paying attention to notifications to upgrade or patch software or hardware vulnerabilities.
- Running occasional 'quick scans' using a trusted anti-malware tool containing anti-rootkit features.
- Being cautious when downloading freeware or P2P transfers, since many are laced in germs.
- Never trusting any program that self loads or runs an unauthorized quick scan.
As mentioned earlier, Trojan.Comronkirts behavior varies per infiltration. However, some common behaviors noted included:
- Disables or disarms security programs or measures.
- Modifies the registry to run automatically its executable at each system startup.
- Adds its malicious program to the 'approved access list' to bypass your firewall.
- Installs an unsigned driver.
- Patches processes in memory.
- Exploits a Remote Assistance Tool or opening a port, so a hacker can secretly control your system.
- Runs other executables or applications without permission.
- Hijacks your browser to keep you from visiting helpful sites or downloading defensive tools.
The thing about malware is that it runs in packs, so once an opening or infiltration occurs, other malicious programs are sure to follow.
Not all malware announces its arrival and other than an alert by a trusted and stealth scanning tool, you may not have a clue your PC is infected by Trojan.Comronkrts. However, there are often subtle hints that many PC users ignore, such as:
- System crashes or freezes up.
- Applications not running correctly.
- Homepage changes or browser redirects to undesirable websites.
- Icons added or missing. Hardware or drivers inoperable.
- System rebooting unexpectedly or not rebooting at all, forcing a manual shutdown.
- Overwhelming pop-ups or a scan indicating intrusion from a foreign rogue security program. Never, ever trust some slick interface that appears out of nowhere and runs an unauthorized quick scan.
At the first hint of an intrusion, whether it is a suspicious activity or a report by a trusted scanning tool, you need to remove it immediately.
ESG's security researchers have seen an alarming use of a rootkit to bury or camouflage malware such as Trojan.Comronkirts. Unless you are highly skilled in editing registry, system, or .dll directory files, you should use a reputable anti-malware tool containing an anti-rookit to find all traces of Trojan.Comronkirts and safely remove Trojan.Comronkirts off your PC.
In the interim, do not use your Internet to transact online banking or purchasing and make sure to use a clean PC to alter your security credentials and logins.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Generic Trojan |
| AVG | PSW.Generic7.CJO |
| Ikarus | Trojan-Banker.Win32.Banker |
| AhnLab-V3 | Win-Trojan/Keylogger.560128 |
| Antiy-AVL | Trojan/Win32.KeyLogger.gen |
| AntiVir | TR/ATRAPS.Gen |
| DrWeb | Trojan.KeyLogger.3900 |
| Comodo | TrojWare.Win32.Spy.KeyLogger.~E |
| BitDefender | Trojan.Generic.1626953 |
| Kaspersky | Trojan-Spy.Win32.KeyLogger.bui |
| eSafe | Win32.TRATRAPS |
| Symantec | Spyware.Keylogger |
| F-Prot | W32/Trojan2.HCBU |
| NOD32 | a variant of Win32/Spy.KeyLogger.NJW |
| K7AntiVirus | Spyware |
SpyHunter Detects & Remove Trojan.Comronki!rts
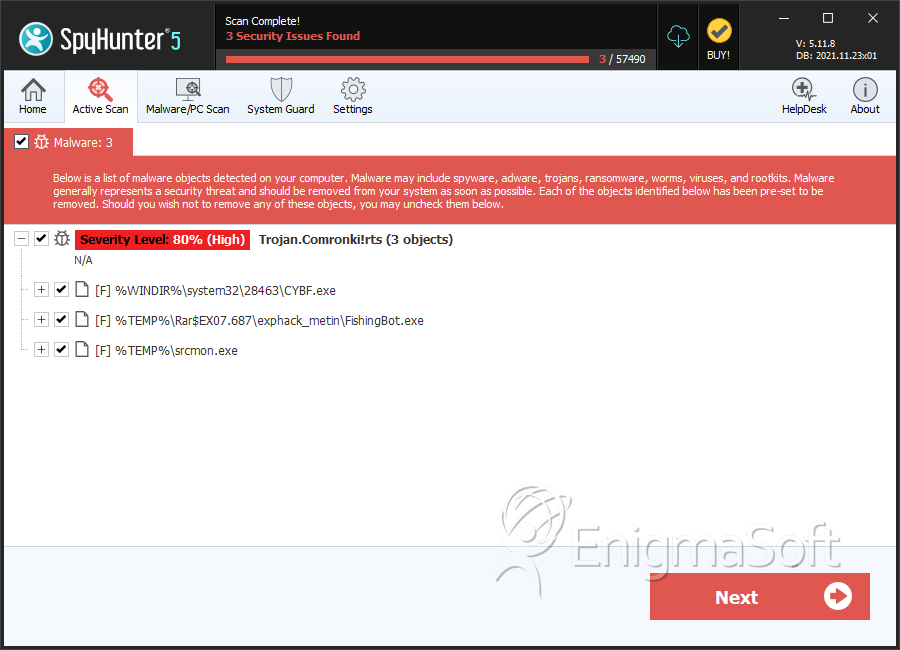
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | CYBF.exe | b314bd03990cf08f3ca04dd98ece3e9c | 6 |
| 2. | FishingBot.exe | d65c0b37df3b46a1e05feb8dccd4a55c | 3 |
| 3. | srcmon.exe | 723de08f6727b196dce1b27f2ec224a8 | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.