Trojan.Betabot
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
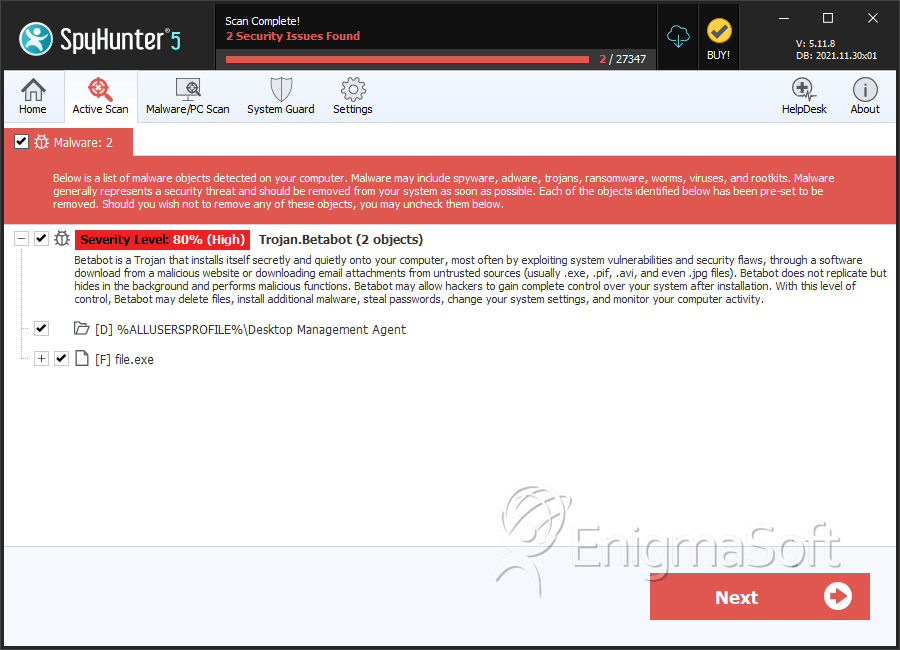
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 49 |
| First Seen: | February 27, 2013 |
| Last Seen: | April 11, 2023 |
| OS(es) Affected: | Windows |
Trojan.Betabot is a Trojan that opens a back door on the corrupted PC. Once run, Trojan.Betabot replicates itself to the particular location on the affected computer system. Trojan.Betabot creates the registry entries that enable it to launch automatically every time you start Windows. Trojan.Betabot may also create and make modifications to other registry entries on the infected computer. Trojan.Betabot then modifies the Windows Registry to reduce Internet security settings. Trojan.Betabot creates a covered instance of the 'iexplore.exe' process and embeds a code into it. Trojan.Betabot then connects to one of the locations and opens a back door, which enables a remote cybercriminal to get full access and control of the attacked PC. Trojan.Betabot then terminates all applications with open windows that incorporate 'explorer.exe'.
Table of Contents
SpyHunter Detects & Remove Trojan.Betabot
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %ProgramFiles%\Common Files\[Windows Licence Check].{2227A280-3AEA-1069-A2DE-08002B30309D}\[NINE RANDOM LOWER CASE CHARACTERS].exe | ||
| 2. | %ProgramFiles%\Common Files\[Flash Update Client].{2227A280-3AEA-1069-A2DE-08002B30309D}\[NINE RANDOM LOWER CASE CHARACTERS].exe | ||
| 3. | %ProgramFiles%\Common Files\[TROJAN FOLDER NAME].{2227A280-3AEA-1069-A2DE-08002B30309D}\[NINE RANDOM LOWER CASE CHARACTERS].exe | ||
| 4. | file.exe | 9d9021fe1aa61e13e8190cccaec8f7fd | 0 |
| 5. | file.exe | 964b98b3e6a2b30b388cc2a2543dee8d | 0 |
| 6. | file.exe | 0f97c0600cb950fe9430023345529356 | 0 |
| 7. | file.exe | 4268720e55ae925de44e06cd3cfcaf65 | 0 |
| 8. | file.exe | f5a1184792b4ae7a32b32df2f78f856f | 0 |
Registry Details
Directories
Trojan.Betabot may create the following directory or directories:
| %ALLUSERSPROFILE%\Desktop Management Agent |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.