Trojan.Agent.iwr
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
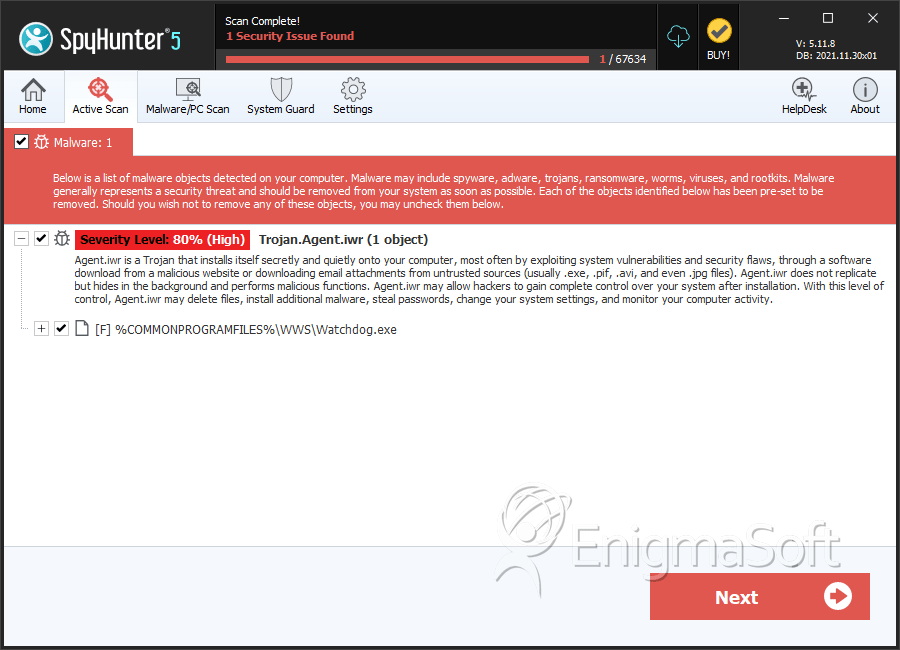
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 12,243 |
| First Seen: | March 13, 2015 |
| Last Seen: | August 23, 2021 |
| OS(es) Affected: | Windows |
Trojan.Agent.iwr is an information-collecting type of threat that may compromise all Windows PCs that lack a reliable protection. After corrupting your system, Trojan.Agent.iwr may start monitoring all of your actions. Trojan.Agent.iwr may provide its operators with access to your hard drive, which would mean they may be able to collect valuable files. However, unless you are famous, the con artists may be more interested in your money than, for example, your pictures. They may be able to take your cash because Trojan.Agent.iwr may track your online actions as well. This cyber threat may serve as a keylogger, which means that Trojan.Agent.iwr may intercept all the data you type during your surfing sessions. Trojan.Agent.iwr also may understand which site you are viewing currently If you enter any data on a financially-oriented or banking platform, the culprits may obtain it soon enough.
The collected login credentials may be transmitted towards remote Command and Control (C&C) servers of the hackers automatically. The function of these machines is not only to receive the information sent from your PC. Instead, the traffic may go both ways, so the con artists may use them to communicate with the threat. According to some reports, computers infected with Trojan.Agent.iwr have been involved in botnets and Distributed Denial-of-Service (DDoS) attacks. Trojan.Agent.iwr may travel inserted in some suspicious email attachments or stand-alone programs hosted on questionable sites. If you make the mistake to open such file, Trojan.Agent.iwr may spread its codes on essential system files like userinit.exe and init32.exe. In addition, the threat may create some registry subkeys to trouble its detection and removal even further. To prevent to be infected with this Trojan, or to delete Trojan.Agent.iwr afterwards, you need to use a dedicated anti-malware program.
Table of Contents
SpyHunter Detects & Remove Trojan.Agent.iwr
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Watchdog.exe | b9ec6ae15bba9cc54f7dcb5e28bb2f7b | 1,249 |
| 2. | tmp3BE8.tmp | 098e8f62d75d3907484a66918bc96ca2 | 1,191 |
| 3. | Watchdog.exe | 43f20ca7ee1b86242e17fae047f5bdf1 | 1,026 |
| 4. | Watchdog.exe | 62e36273a46e1ef6f4212d510d40fc6b | 939 |
| 5. | Watchdog.exe | 421a84d1bc15f3f22920b4f525f75725 | 747 |
| 6. | Watchdog.exe | 2eaf4684197ece5b429a8f9d174b67b8 | 613 |
| 7. | Watchdog.exe | 176ad36c78763a6d4f17d6cda979999f | 350 |
| 8. | Watchdog.exe | f5ab3ad898bb6240ab3d94402dc465a9 | 259 |
| 9. | Watchdog.exe | 0e31e87bb6e8d6464a93095c8f0bac04 | 248 |
| 10. | Watchdog.exe | e1b2e95ab59b6b94be67c5a72710f736 | 246 |
| 11. | Watchdog.exe | 233df91e038d5c0cd42307372ed08e4f | 229 |
| 12. | Watchdog.exe | 4404f30f88430868464175265fd03102 | 172 |
| 13. | Watchdog.exe | 381b1010a03fe2f9b207d758cad05cb9 | 160 |
| 14. | Watchdog.exe | 63572b58488c8c2392c22a17aa1476c3 | 155 |
| 15. | Watchdog.exe | 379b584cf38d8abf3b0a15b1df725bdd | 154 |
| 16. | Watchdog.exe | d1de52cd11eacf3c82bae959e3fb6949 | 146 |
| 17. | Watchdog.exe | 0b21108b3bda1a5376dca6181d8896dd | 131 |
| 18. | Watchdog.exe | 28c919097e3908666b351289b3f214c6 | 127 |
| 19. | Watchdog.exe | ae12792d120085a8857e4414d7740f0e | 118 |
| 20. | Watchdog.exe | e8c5ac73a830c0bfec94ed5dedf3fa65 | 117 |
| 21. | Watchdog.exe | d3f57bd7fa314c9e90fdd47ce490e66d | 105 |
| 22. | Watchdog.exe | 4c7f05c3f93cf8816a476fe129d32f7f | 98 |
| 23. | Watchdog.exe | f39d431a1672e09e9420d4e89714dc0d | 97 |
| 24. | Watchdog.exe | 767be295a423d09814d7c83b3c183866 | 96 |
| 25. | Watchdog.exe | 50b96e558b3dfe7ae5df6dd36e1bc03d | 92 |
| 26. | Watchdog.exe | 65682cbf5330091a3f0bfe230e9eb02e | 91 |
| 27. | Watchdog.exe | 49f531fe985ca5022e9f7c22d76ddc29 | 84 |
| 28. | Watchdog.exe | a4c04155c80a73870e23b3e727899f27 | 83 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.