SweetIM
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 1,674 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 221,121 |
| First Seen: | May 3, 2010 |
| Last Seen: | May 24, 2026 |
| OS(es) Affected: | Windows |
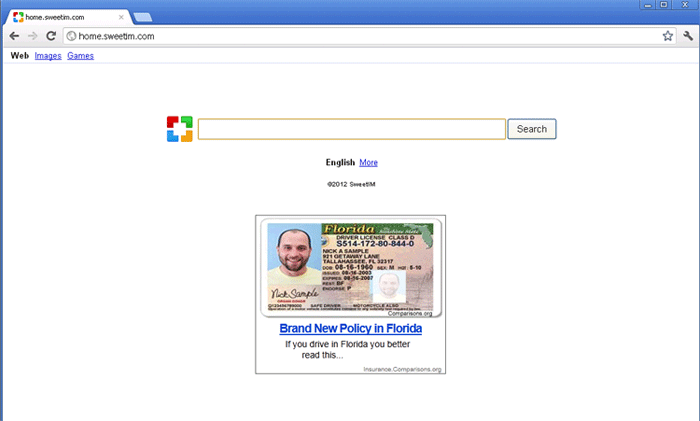
SweetIM Image
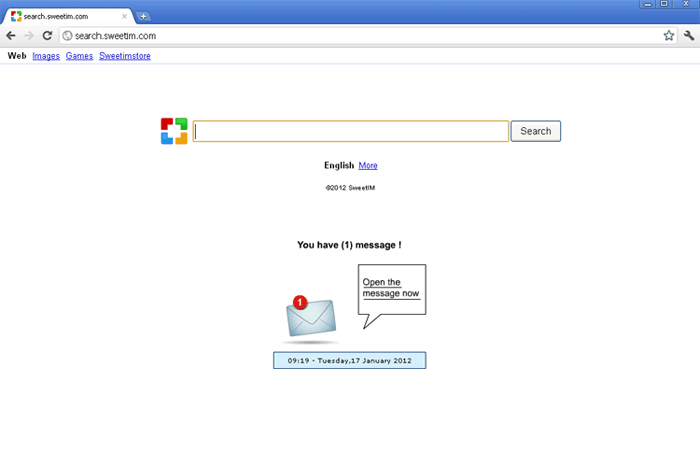
When PC security researchers see the message 'get free smilies', it immediately sets off multiple red flags. This is because the offer of free emoticons is one of the most common ways in which criminals entice inexperienced computer users into downloading and installing malware onto their computer system. SweetIM, associated with the website and toolbar search.sweetim.com, is one of many dodgy companies that lures its victims with the promise of free emoticons but delivers nothing but plenty of hassles and security risks. Because of this, security researchers strongly advise computer users to stay away from SweetIM or from the search.sweetim.com website. Contact with this 'free' service will do nothing but bring infections to your computer system and install a toolbar that cannot be removed through normal means.
Table of Contents
The Main Problems with SweetIM
Computer users visiting websites that do not take care to make sure that advertisements they display are not associated with malware will often have come across obtrusive banner advertisements promising free emoticons for your computer. These obnoxious advertisements will often use pop-up windows or sound in order to obstruct computer users' normal online activity. SweetIM follows all of these tactics. If a computer user downloads SweetIM, SweetIM will immediately block all web browsers except Internet Explorer, since SweetIM is designed to take advantage of Internet Explorer's known vulnerabilities to Browser Helper Objects (that is, malicious toolbars designed to affect your web browser in some way or another). Then, once installed, SweetIM will not allow the victim to remove the SweetIM toolbar from the web browser through normal uninstall procedures. Since the search.sweetim.com toolbar has several obtrusive features (such as being associated with browser redirects and pop-ups, as well as containing elements that may be spying on your online activity), many computer users will quickly want to remove this obnoxious presence from the web browser.
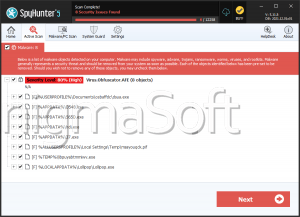
Removing the SweetIM Toolbar
Since SweetIM does not allow removal through Internet Explorer's 'remove add-on' feature and it cannot be removed from the Control Panel, SweetIM may end up leaving a frown on many of its victims' faces. However, removing SweetIM can be done by downloading a particular tool which will erase this obtrusive presence from your computer system. Many anti-virus or anti-malware programs will not detect SweetIM for what SweetIM is, although some of the top anti-malware programs on the market will include tools that allow computer users to deal with infections similar to SweetIM. Downloading and installing the latest definitions for your anti-malware software should help in detecting any malware that may have entered your system as a result of installing SweetIM.
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| AVG | Sweetim.4FB |
| AVG | MalSign.BitCocktail.0E0 |
| Sophos | BitCocktail |
| TrendMicro | TROJ_SPNR.16AM12 |
| Comodo | TrojWare.Win32.PkdKrap.Gx |
| Avast | Win32:Downloader-MOM [Trj] |
| NOD32 | a variant of Win32/Kryptik.ZBL |
| McAfee | Artemis!B35054C47844 |
| BitDefender | Gen:Variant.Graftor.12959 |
| NOD32 | a variant of Win32/Kryptik.ZCE |
| Antiy-AVL | Trojan/win32.agent.gen |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.ModifiedUPX.J!87 |
| McAfee | GenericTRA-AC!1B37D00E7204 |
| AVG | Generic26.ASSM |
| BitDefender | Gen:Variant.Kazy.50515 |
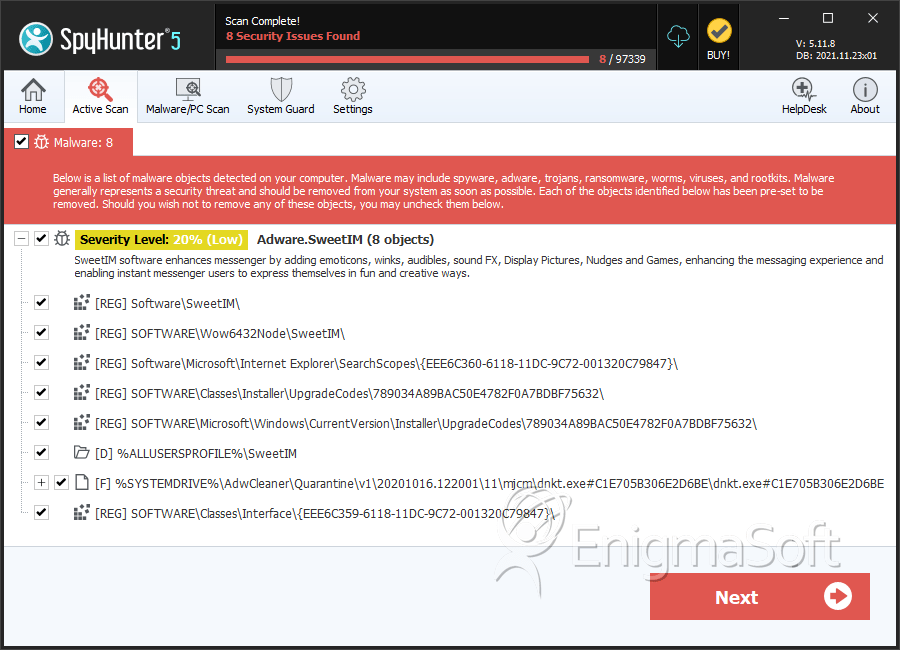
SpyHunter Detects & Remove SweetIM
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | dnkt.exe#C1E705B306E2D6BE | b2cf341204e5ff0353f6421e2d3c8701 | 5,067 |
| 2. | dnkt.exe.vir | 1e1877ff0ece5d97b30c67470cea55ac | 1,679 |
| 3. | lmrn.dll.vir | a1939f2c611e9ddd3d3d9083bbfd0c0b | 729 |
| 4. | Extension32.dll.vir | 4c1d9f10981bc18417e73151a9d37716 | 597 |
| 5. | ExtensionUpdaterService.exe.vir | 388aed0bbe3b0d10297c52c9983df444 | 500 |
| 6. | SweetNT.crx | 189bf5cb9190caef035e00ca521433fb | 376 |
| 7. | QueblesAutoUpdate.exe | d07a6925513f34272f0a8388ff25b7c6 | 357 |
| 8. | USDownloader.exe | 57c3d3cd8d2c2863ce09cd1f41836718 | 222 |
| 9. | SweetPacksUpdateManager.exe | 0c24f7ee670437f023612ff31cad22bb | 149 |
| 10. | Extension32.dll | 0a6f5467b99a4724d1914694aafb9b80 | 144 |
| 11. | SweetIMSetup.exe | 3922583eb499ea4c003802ca9cd77e3d | 72 |
| 12. | unins000.exe | 7efccf3c7cccda95a46d3d6002237307 | 32 |
| 13. | xmxt.exe | 9c23ecf21c7d5ac34bbacbf23f537b3a | 27 |
| 14. | hDNYrohYYsM.exe | cc813c29bf35e72fa8c1724773b7c3e7 | 26 |
| 15. | bclm.exe | 8af4d2267051abe2f29769b0b64f6283 | 25 |
| 16. | dnkt.exe | 89ac1db015062b37f97f175e69ec57ee | 12 |
| 17. | SweetIM.exe | 3c65a1e2a4ce6e4023da1a3de42e003b | 11 |
| 18. | mgHelper.dll | c59d3f7d30d853f2202b3076b3a77958 | 10 |
| 19. | Extension64.dll | 56ca7193a4035792f39df4652be0d8c1 | 6 |
| 20. | 264dsse2.dll | 39fad13f5cd84e1eaae3659a278cf313 | 5 |
| 21. | _ex-68.exe | c6cf379023f8d74dd223477d01d2b5ea | 4 |
| 22. | xqfaji.exe | ca6551e16849718240091a1f4e7ae490 | 4 |
| 23. | ExtensionUpdaterService.exe | e3ac6d88f6af116fbd767d6d9720be03 | 3 |
| 24. | DevWebAgent.dll | e61907120bcb10e1ba91dda5454f4973 | 2 |
| 25. | 25.exe | e92d2186100d900c7c56b4f875abf1de | 2 |
| 26. | crrss.exe | 3bbea3f0047085ffee80bf0326840758 | 2 |
| 27. | aopnaaguwewryg.exe | b35054c47844740352fd12147a1335cb | 2 |
| 28. | ypmvzoag.dll | 41f97c4c5a4c0b3139355fa846926ab9 | 2 |
| 29. | vpsqac.exe | 59585389d756e02184957340fb514efe | 1 |
| 30. | mgToolbarIE.dll | b77b048b498b0bc09621b63f0247c4c0 | 1 |
| 31. | C:\Program Files\Macrogaming\SweetIMBarForIE\toolbar.dll | ||
| 32. | C:\Program Files\Macrogaming\ | ||
| 33. | C:\Program Files\Macrogaming\SweetIMBarForIE\Greetingcards_23x18.bmp | ||
| 34. | C:\Program Files\Macrogaming\SweetIMBarForIE\SmileyWink.bmp | ||
| 35. | C:\Program Files\Macrogaming\SweetIMBarForIE\toolbar.crc | ||
| 36. | C:\Program Files\Macrogaming\SweetIMBarForIE\SmileySmile.bmp | ||
| 37. | C:\Program Files\Macrogaming\SweetIMBarForIE\ | ||
| 38. | C:\Program Files\Macrogaming\SweetIMBarForIE\Mobile_23x18.bmp | ||
| 39. | C:\Program Files\Macrogaming\SweetIMBarForIE\version.txt | ||
| 40. | C:\Program Files\Macrogaming\SweetIMBarForIE\Thumbs.db | ||
| 41. | C:\Program Files\Macrogaming\SweetIMBarForIE\basis.xml | ||
| 42. | C:\Program Files\Macrogaming\SweetIMBarForIE\Cache\ | ||
| 43. | C:\Program Files\Macrogaming\SweetIMBarForIE\Games_23x18.bmp | ||
| 44. | C:\Program Files\Macrogaming\SweetIMBarForIE\affid.dat | ||
| 45. | C:\Program Files\Macrogaming\SweetIMBarForIE\sweetimicons.bmp | ||
| 46. | C:\Program Files\Macrogaming\SweetIMBarForIE\Cache\cd2005c66fba47ff715ecc444d3bc1fb.xml |
Registry Details
Directories
SweetIM may create the following directory or directories:
| %ALLUSERSPROFILE%\Application Data\SweetIM |
| %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\free-for-download bundle |
| %ALLUSERSPROFILE%\SweetIM |
| %LOCALAPPDATA%\Google\Chrome\User Data\Default\External Extensions\{EEE6C373-6118-11DC-9C72-001320C79847} |
| %PROGRAMFILES%\SweetIM |
| %PROGRAMFILES%\sweetpacks bundle uninstaller |
| %PROGRAMFILES(x86)%\SweetIM |
| %PROGRAMFILES(x86)%\sweetpacks bundle uninstaller |
| %ProgramFiles%\Updater By SweetPacks |
| %ProgramFiles(x86)%\Updater By SweetPacks |
| %UserProfile%\AppData\LocalLow\SweetIM |
| %UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\External Extensions\{EEE6C373-6118-11DC-9C72-001320C79847} |
| %WINDIR%\SysWOW64\mjcm |
| %WINDIR%\SysWOW64\tprb |
| %WINDIR%\System32\mjcm |
| %WINDIR%\System32\tprb |
URLs
SweetIM may call the following URLs:
| sweetpacks-search.com |
Analysis Report
General information
| Family Name: | Adware.SweetIM |
|---|---|
| Packers: | UPX |
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
eaa1e5f3deaefa753c9697175435f792
SHA1:
de2b18a0d2e961a1ffb9bfa5c9ca6e4f65e8832c
SHA256:
A01193EAFD0268433404038E6C9238237236095990DD11876DAB4384F12B7298
File Size:
351.02 KB, 351024 bytes
|
|
MD5:
2a5187683cf09e53115c44fb3fec5ec6
SHA1:
ce5274a039a47547c848a7fa7c81f6de740154a4
SHA256:
69781ACB19F504AB7DC22CBBF3367F997954364D909A49BF11688F0F851E12A0
File Size:
1.25 MB, 1253376 bytes
|
|
MD5:
52908ad5a7ad9701b938f4b8be8c295d
SHA1:
53f3ab6daeb13df7338e27be6b27678714981e55
SHA256:
278B7A7386C0F52642882571885AB899A6F8F3C83BD8F8594E3D531974C6DBFC
File Size:
2.18 MB, 2178320 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has been packed
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | local setups |
| Company Name | SweetIM Technologies Ltd. |
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename | mgToolbarIE.dll |
| Private Build | 2 |
| Product Name |
|
| Product Version |
|
| X V I_ Compid |
|
| X V I_ Internal Prod Ver |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| SweetIM Technologies Ltd | Class 3 Public Primary Certification Authority | Root Not Trusted |
File Traits
- big overlay
- dll
- Installer Version
- packed
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 4,314 |
|---|---|
| Potentially Malicious Blocks: | 7 |
| Whitelisted Blocks: | 3,451 |
| Unknown Blocks: | 856 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\microsoft\windows\usrclass.dat{dba6b5ef-640a-11ed-9bcb-f677369d361c}.txr.0.regtrans-ms | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\microsoft\windows\usrclass.dat{dba6b5ef-640a-11ed-9bcb-f677369d361c}.txr.1.regtrans-ms | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\microsoft\windows\usrclass.dat{dba6b5ef-640a-11ed-9bcb-f677369d361c}.txr.2.regtrans-ms | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\1755831383_561078_41.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561140_467.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561156_334.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561156_500.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561171_137.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561171_582.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561187_312.tmp | Generic Write,Read Attributes |
Show More
| c:\users\user\appdata\local\temp\1755831383_561187_450.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561187_896.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561203_122.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561203_622.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\1755831383_561218_873.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\de2b18a0d2e961a1ffb9bfa5c9ca6e4f65e8832c_0000351024 | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|
| Keyboard Access |
|
| Network Wininet |
|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\ce5274a039a47547c848a7fa7c81f6de740154a4_0001253376.,LiQMAxHB
|