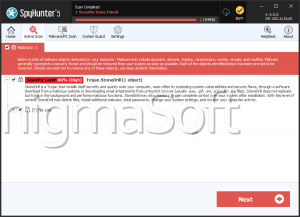
StoneDrill
The StoneDrill malware is a very potent threat that has were first spotted in 2017. Back then, there was a campaign employing the StoneDrill malware that was launched against a European corporation that deals in the sector of petrochemistry. The StoneDrill malware can serve both as a tool for espionage, as well as a wiper. Also, this threat can be used as a backdoor for the attackers to plant additional malware on the infiltrated host. The StoneDrill malware has several variants that have been identified so far, and they all seem to have various features. Researchers found Persian and Arabic (from the Yemeni region) strings and comments in the code - an unlikely finding since the malware developers are obviously experienced, and should not leave traces of this sort. This might mean that the clues were left on purpose to leave researchers with the impression that this is where the StoneDrill malware was developed.
Table of Contents
StoneDrill VS Shamoon
Malware researchers speculate that the StoneDrill malware is an updated version of the older and rather popular Shamoon wiper. Despite all they have in common, the StoneDrill malware and the Shamoon wiper have some significant differences. The StoneDrill threat is capable of detecting if it is being run in a sandbox environment, and if it is, it can terminate all activity. Also, instead of dropping files on the infected machine, the StoneDrill malware plants its code in the memory of a legitimate process, therefore hiding it from the user, as well as evading some low-quality anti-virus products. Furthermore, the StoneDrill malware is able to delete itself from the host by using VBS (Visual Basic Scripts).
The Wiper Module
StoneDrill is able to identify logical and physical drives, and then executes the necessary commands to ensure that all data on them will be wiped - the only exclusion is the 'Windows' directory that the wiper module will spare in order to allow the computer to continue running.
StoneDrill Used for Reconnaissance
A different variant of the StoneDrill was spotted – this version of the threat is not capable of wiping data but can be used as an espionage tool instead. It would scan the infected host to find out whether there is an anti-malware tool present on the system. This version of the StoneDrill malware can gather information about the compromised system and siphon it to the attackers. Malware researchers have concluded that this variant is likely still in progress because it appears unfinished despite having a fair bit of potential.
StoneDrill As A First-Stage Payload
A third version of the StoneDrill malware appears to be built to serve as a first-stage payload that would enable the attackers to infect the compromised PC with additional threats. This variant of the StoneDrill threat is also capable of avoiding sandbox environments.
It is probable that we will see some more high-end hacking campaigns that employ various versions of the StoneDrill malware since this threat is constantly evolving and becoming more weaponized. Download and install a legitimate anti-virus software suite. which will keep your system secure.