SpyNote RAT
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 15,099 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 370 |
| First Seen: | January 4, 2013 |
| Last Seen: | August 5, 2025 |
| OS(es) Affected: | Windows |
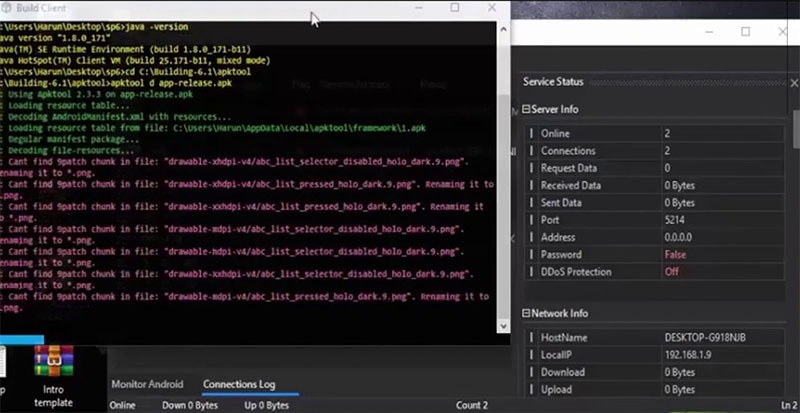
SpyNote RAT Image
Remote Access Trojans (RATs) for Android devices may pack a lot of features that enable their authors with the ability to carry out a broad range of unsafe operations on the infected device. One of the more popular Android RAT projects is SpyNote, and its full source code can be found on many hacking forums. One of the scary things about the SpyNote RAT is that it is absolutely free to use so that anyone can start distributing their unique version of it. Furthermore, criminals who are experienced with programming can write additional modules to extend the SpyNote RAT's features.
SpyNote’s Source Code is Available to all Cybercriminals
Apart from the GitHub page hosting SpyNote RAT's full source code, ads for this hacking tool can be found on many other hacking forums too. Some of the notable features that the SpyNote RAT has allowed it to execute the following tasks:
- Access the device's storage and modify, view or delete files.
- Use the SMS app to read and write messages.
- Use the phone to initiate calls, modify call logs or access and collect contacts.
- Record photo or video footage with available cameras silently.
- Use the microphone to record what is happening around the phone.
- Activate and track the GPS sensor.
- Modify installed applications.
- Acquire software and hardware details.
- Operators get access to a 'FUN PANEL' that can be used to manipulate the phone's behavior in weird and unexpected ways.
SpyNote was Masked as a Fake Netflix Application Previously
One of the largest propagation campaigns involving the SpyNote RAT was carried out with the use of fake copies of popular software. The most notable example was a bogus 'Netflix' application that was hosted on unofficial application stores and 3rd-party application hosting services. The program might have been promoted by promising users that they will be able to use Netflix's services without a subscription, therefore making it more likely that they will opt to download the fake variant.
It is recommended never to download Android applications from unknown sources if they claim to offer features that are too good to be true, especially. Furthermore, it is advisable to use a reputable Android security engine that will scan incoming files for harmful traits, and eliminate them before they get a chance to cause trouble.
