SpeedMaxPC
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 891 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 14,129 |
| First Seen: | September 1, 2011 |
| Last Seen: | October 15, 2025 |
| OS(es) Affected: | Windows |
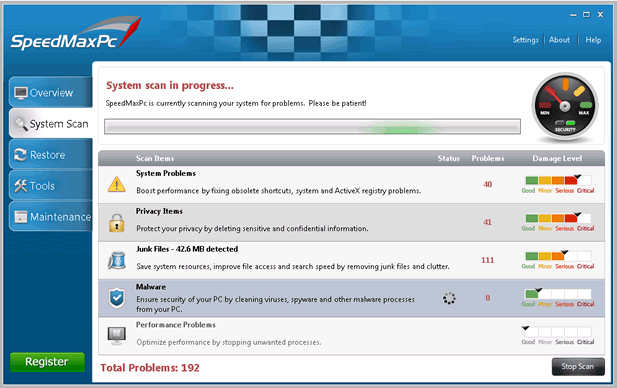
SpeedMaxPC Image
SpeedMaxPC is a rogue computer optimizer and utilized to abduct money from newcomer computer users. Like other rogue security programs, SpeedMaxPC claims to be a legitimate solution to problems on a computer. However, SpeedMaxPC will actually be responsible for problems such as a decreased system performance and an enormous number of bogus error messages. ESG malware researchers strongly advise computer users to avoid installing SpeedMaxPC on their computer. Criminals profit from SpeedMaxPC by convincing inexperienced computer users that they need to purchase an expensive 'full version' of SpeedMaxPC in order to remove nonexistent problems on the infected computer. It is important to ignore all claims made by SpeedMaxPC and not to purchase a 'full version' of this fake system optimizer. Instead, SpeedMaxPC should be removed with the help of a real security application.
SpeedMaxPC has the capacity to display realistic looking error messages and system alerts on the infected computer. These error messages are very similar to the ones that may be displayed by a legitimate security program. However, they may contain grammatical errors or strange elements that betray the fact that they are not real. The similarity between real security programs and SpeedMaxPC ends here; this fake system optimizer displays completely false information in its error messages, detecting corrupted files or malware that is simply not present on the victim's computer. One important thing to remember about SpeedMaxPC is that SpeedMaxPC will often report problems with legitimate Windows files. Computer users who try to fix this 'problem' by removing the supposedly infected files will suddenly find that their Windows operating system cannot continue normally without them.
Although SpeedMaxPC is marketed as a program that can help a computer become faster and more efficient, SpeedMaxPC actually does the opposite. SpeedMaxPC may cause the affected computer to become slower and crash frequently. This is because SpeedMaxPC does not interact well with other, legitimate programs. It is also important to note that SpeedMaxPC may stop your normal activities by displaying fake error messages quite frequently, making it difficult to use the infected computer normally. This, of course, more than negates any supposed speed increases that should come from using SpeedMaxPC.
Table of Contents
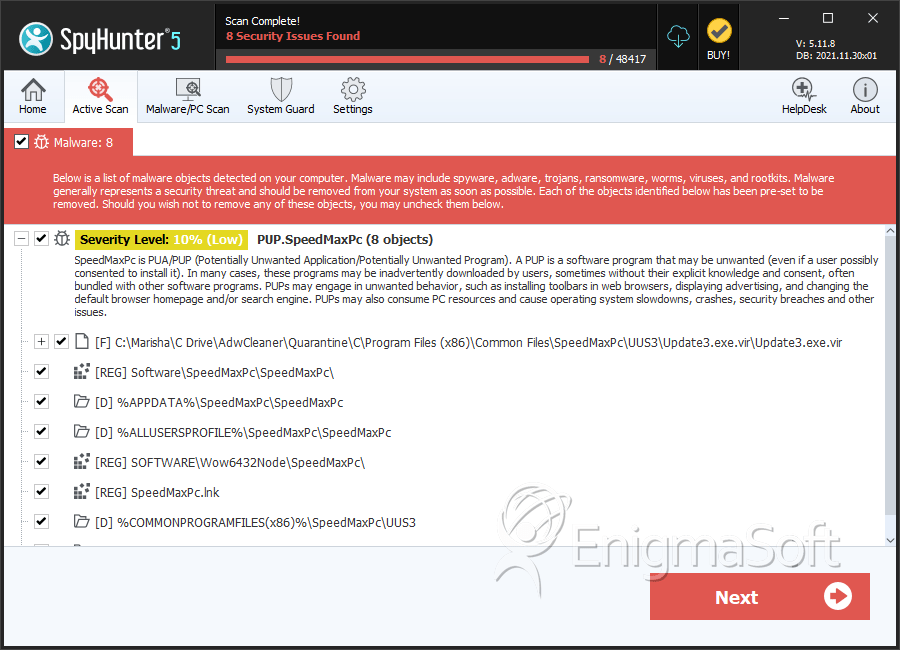
SpyHunter Detects & Remove SpeedMaxPC
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Update3.exe.vir | 3371ec12af3e3098d1336f28f7029781 | 2,525 |
| 2. | Update3.exe | 16fa148b70058415d3bf4888abb5bc3e | 10 |
| 3. | SpeedMaxPc.exe | 61ec304023c79b65fec63cf816254dca | 0 |
Registry Details
Directories
SpeedMaxPC may create the following directory or directories:
| %ALLUSERSPROFILE%\SpeedMaxPc\SpeedMaxPc |
| %APPDATA%\Microsoft\Windows\Start Menu\Programs\SpeedMaxPc\SpeedMaxPc |
| %APPDATA%\SpeedMaxPc\SpeedMaxPc |
| %COMMONPROGRAMFILES%\SpeedMaxPc\UUS3 |
| %COMMONPROGRAMFILES(x86)%\SpeedMaxPc\UUS3 |
| %PROGRAMFILES%\SpeedMaxPc\SpeedMaxPc |
| %PROGRAMFILES(x86)%\SpeedMaxPc\SpeedMaxPc |
Analysis Report
General information
| Family Name: | PUP.SpeedMaxPc |
|---|---|
| Packers: | UPX |
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
d4b65dc35b137b2427319948a8fcaeec
SHA1:
e27b265ffa3bd467c51bb6f53dedd104e73f4172
File Size:
6.30 MB, 6298880 bytes
|
|
MD5:
af6a79ba4733f4d16698397d0a416452
SHA1:
91ccb7a16d8dabb56b67b6c08271cbe9759067e8
SHA256:
266CA948B7B93F472D7D8DE5508459FA9AB548C3F5C3078AF2542BC0503C34E5
File Size:
2.94 MB, 2941493 bytes
|
|
MD5:
8b4aeee9f8f4c1c90d12e4d447a29c59
SHA1:
57af2896f40238ae1f0167f07e3edeb65d51b66f
SHA256:
D80A692D3CD2037904A3D5AAD6ECE646C62A882C6CB932BBD509181376087D2E
File Size:
3.41 MB, 3405885 bytes
|
|
MD5:
a9d34af06225d27d3520c9b56d82fc5e
SHA1:
30db502adc9e32f033c9c2078ff36e907c8a250c
SHA256:
04FFC018C6F22DD8077CDBC2F9DC7F3E67BD3D0DBB1D0C5ADBE7E899F06EE8FB
File Size:
28.67 KB, 28672 bytes
|
|
MD5:
a0743f2550c09fef5b2a50cd90a527c1
SHA1:
6f69009f03106f3ca67cef608673327c42027b1f
SHA256:
A951A165044D56CBBF7EC9459C1E2E8BD38DB330C71A87F6AC96F5CE2441F432
File Size:
53.25 KB, 53248 bytes
|
Show More
|
MD5:
9a62a76e6dcdc54cdfd6ea88e1c12ecb
SHA1:
c3bca3d102886ce93f40238d352df7b63a16176c
SHA256:
E37961277C6E0BECDE8589B399D0548EE2564DEAB37FABBCE89A10A3E9D70172
File Size:
597.50 KB, 597504 bytes
|
|
MD5:
4aca31b558a10153e722a7bcf7f0d390
SHA1:
ccb0f2dc36bc336920e201e64af9754258872b1f
SHA256:
4AB5BC1DA2147B60E6CE46240C6A79D068B55BC64BCAAD1B61D3D08644D20506
File Size:
485.89 KB, 485888 bytes
|
|
MD5:
89f9f7a8c8f83cb07cbf928da778c117
SHA1:
491eb3ab18594fc94539334ca5907f37efe223cd
SHA256:
D2237ECB7D08BD217645AD38B2C413478068C69BB6731EC6FD50D263454582D9
File Size:
449.54 KB, 449536 bytes
|
|
MD5:
03828cc19dbb99b9a06fab96e87e4605
SHA1:
1fc5823a01e9875460283bfa6eca5f64356377b1
SHA256:
FD6E0D270FE8818A6C51D69FCC15137C2C31675DD6C150439872D5605DEA76EE
File Size:
2.94 MB, 2941519 bytes
|
|
MD5:
ada2cb39e40de88051b589010a26acdc
SHA1:
f35eadf8723853464ca0a76782db29f37ac7cb24
SHA256:
B87D7AEF960B95CF3A9EA798C2DFA8674A6DCA8AC4308C41947893C2C6FF0B08
File Size:
548.86 KB, 548864 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has been packed
- File has exports table
- File has TLS information
- File is .NET application
- File is 32-bit executable
Show More
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Show More
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 2013.11.22.0 |
| Comments |
|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
| Version V I | xxxxxxxxxx |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Exeldro | SSL.com Root Certification Authority ECC | Root Not Trusted |
File Traits
- .NET
- 2+ executable sections
- Inno
- InnoSetup Installer
- Installer Manifest
- Installer Version
- packed
- VirtualQueryEx
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 4,469 |
|---|---|
| Potentially Malicious Blocks: | 9 |
| Whitelisted Blocks: | 2,945 |
| Unknown Blocks: | 1,515 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Banker.R
- Emotet.CCA
- Emotet.CDD
- Injector.AK
- Injector.KPP
Show More
- Lumma.GFD
- Rugmi.IA
- Sheloader.A
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\is-9lpfv.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-l29s0.tmp\e27b265ffa3bd467c51bb6f53dedd104e73f4172_0006298880.tmp | Generic Write,Read Attributes |
| c:\users\user\downloads\apexupdate.log | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\downloads\bgb.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\windows\appcompat\programs\amcache.hve | Read Data,Read Control,Write Data |
| c:\windows\appcompat\programs\amcache.hve.log1 | Read Data,Write Data |
| c:\windows\appcompat\programs\amcache.hve.log2 | Read Data,Write Data |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Process Shell Execute |
|
| User Data Access |
|
| Keyboard Access |
|
| Syscall Use |
Show More
|
| Anti Debug |
|
| Encryption Used |
|
| Process Manipulation Evasion |
|
| Network Winsock2 |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"C:\Users\Esupdqol\AppData\Local\Temp\is-L29S0.tmp\e27b265ffa3bd467c51bb6f53dedd104e73f4172_0006298880.tmp" /SL5="$601DE,5335659,891904,c:\users\user\downloads\e27b265ffa3bd467c51bb6f53dedd104e73f4172_0006298880.exe"
|
C:\Windows\Microsoft.NET\Framework64\v2.0.50727\\dw20.exe dw20.exe -x -s 864
|

