Spamhaus Ransomware
Spamhaus Ransomware Image
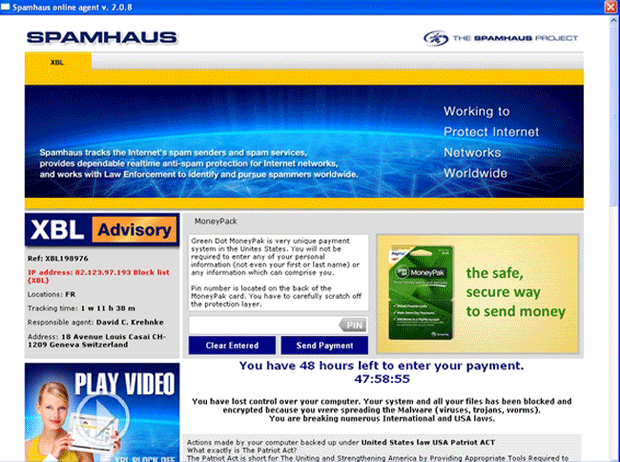
The Spamhaus Ransomware Trojan is a malware infection that has been responsible for various recent attacks. The Spamhaus Ransomware uses a fake warning from Spamhaus, a legitimate organization that tracks spam distributors and works with law enforcement agencies to prosecute spammers around the world. While the legitimate Spamhaus organization is located in Switzerland and provides a valuable service, the Spamhaus Ransomware is actually a malware threat that sullies this organization's good name by using it as part of its scam. Spamhaus is an important organization dedicated to stopping spam and the malware that often comes as a consequence of these kinds of scams.
The Spamhaus Ransomware message is part of one of these kinds of scams which carries out a typical version of the well known Police Ransomware infection. It is important to note that the Spamhaus Ransomware has no actual connection with Spamhaus and that using the brands of popular anti-virus programs or legitimate law enforcement or anti-spam organizations is a common tactic criminals use to carry out their malware attacks. To bypass the Spamhaus Ransomware message, ESG security researchers advise the use of an alternate start-up method, for example, using Safe Mode or a removable memory device to start up the infected computer.
What is the Goal of the Spamhaus Ransomware Error Message?
Claiming to be version 2.0.8 of the Spamhaus online agent, the Spamhaus Ransomware claims that the victim has 48 hours to make the payment of a fine because the infected computer is being used to distribute malware such as worms, Trojans and viruses. The Spamhaus Ransomware also makes the bogus claim that all files on the victim's computer were blocked and encrypted. This is actually a false claim. The Spamhaus Ransomware isn't capable of encrypting or blocking files. Rather, the Spamhaus Ransomware alters the Windows Registry which prevents the computer user from bypassing the Spamhaus Ransomware message and having access to the computer's Desktop. The files are intact and have not been encrypted in any way. Because of this, it isn't necessary to pay the Spamhaus Ransomware fine. It is simply a matter of bypassing the Spamhaus Ransomware message in order to gain access to security software on the infected computer. In fact, paying this 'penalty' will do zero to remove the Spamhaus Ransomware or allow you to recover control over your computer.

