SegmentAssister Ads
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
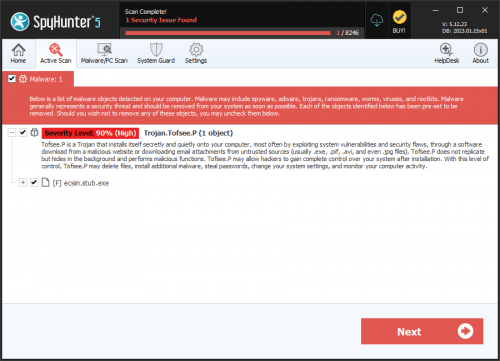
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 8,344 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 4,355 |
| First Seen: | September 15, 2015 |
| Last Seen: | April 18, 2026 |
| OS(es) Affected: | Windows |
The SegmentAssister program is advertised as a search assistant that can hep users browse results on Google faster and find exactly what they are looking for. The SegmentAssister program is developed by MaxAide and can be seen in freeware bundles accompanied by the iLivid Download Manager that is associated with a browser hijacker. Computer users that installed the SegmentAssister program should know that security experts perceive it as adware that is representative of the Multiplug family of adware applications. The SegmentAssister adware may use tracking cookies, detect your approximate geographical location and read your browsing history to determine what type of advertising content would be most appealing to you. The SegmentAssister adware may show pop-up and pop-under windows in Google Chrome, Internet Explorer, and Mozilla Firefox as well as display banners and floating ads on the pages you visit. The SegmentAssister adware is known to start on system boot up as a background service that may be named '4aad814a' and '419ea4b7'. Security analysts remind users that the advertisements by SegmentAssister are not safe, and Web surfers could end up visiting harmful domains like Generalscansite.com and Selectgo.net. Therefore, you might want to use a trusted anti-spyware instrument to scan your PC and eliminate the SegmentAssister adware.
Table of Contents
Analysis Report
General information
| Family Name: | Adware.Dealply.AC |
|---|---|
| Packers: | UPX! |
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
c915913427afdd2cab22b17f544dcc10
SHA1:
0af03fec6af46cb6aef4354512d959561e7b5377
File Size:
569.86 KB, 569856 bytes
|
|
MD5:
fbbb8a7a9c3f6ed1042a1e8ca59d3613
SHA1:
b9fb231a361a3c99c1c40d3b46842ad5e162639b
File Size:
697.34 KB, 697344 bytes
|
|
MD5:
240a59189ae8fe764c66fa6c29b001bf
SHA1:
16bb8212fd1d5c636002200a21cfecb959b89e58
SHA256:
270AF9166702D81724943C322445F69C3C8BCC6BDB908389E2C2D57D5C358603
File Size:
639.49 KB, 639488 bytes
|
|
MD5:
d074d60906216082c0e7a90911fb5205
SHA1:
532bba0ff3d46f6553f4d5a9a764cec916a4c290
SHA256:
931A3A418B3C6335AB8438722A9781750914E59115A3821377861EB1C01BCDDE
File Size:
660.48 KB, 660480 bytes
|
|
MD5:
df003f8f2df83bc841fda399cda22977
SHA1:
ac4383ed2ed366f4d45de8090d7ec57b4c269431
SHA256:
8D6F43164D4EEADE1266AED077B17F186E32C5FFE6241821CE2E31DCBA85E321
File Size:
632.32 KB, 632320 bytes
|
Show More
|
MD5:
e95469840a516805a8e2fc47b5308d7a
SHA1:
474fbcede851f2f351228472c536054a43ad2ccf
SHA256:
E4563101FFD01D80D40D4E48F5DDD02A2BBA347853D6C878E6139A49854A8D26
File Size:
509.44 KB, 509440 bytes
|
|
MD5:
54d9d05d2ed8098f745b3da7e8bd7acb
SHA1:
386322f7474c88c53dfadd7d46c8b9c620914763
SHA256:
99F0A7737CC0DC12E3A4D5C93D88C12B25688678E41BB24DA5DEED43036A5A44
File Size:
613.89 KB, 613888 bytes
|
|
MD5:
2b2c454eb7a6a4c8e1a11ee8b5e7be4d
SHA1:
f5d38fadaa5ac8691fa012024afa87644ddbdefe
SHA256:
F4EE1592AC14E83B67899FA7FAC3506DFBF63E1CC77E684584252B7E9C424B85
File Size:
538.11 KB, 538112 bytes
|
|
MD5:
8d539ff669667f1bcdd8e48df9c37a48
SHA1:
c0c13c6ff8daf3ebcb31d7e252d440a09841b539
SHA256:
18305B91AA54CC7B2964526C848813A789F151770828BD3400B5FB2B43154E00
File Size:
406.02 KB, 406016 bytes
|
|
MD5:
634b9a7151797377108a2b0614e5b0e9
SHA1:
b2592c9fd74ca6babcff4e888b168db153157432
SHA256:
4BF7EAAD94972361B8AA877A3B1C6EED685D04CF0D6974D83CF9427D2354B0CB
File Size:
526.34 KB, 526336 bytes
|
|
MD5:
5ba398e78da9751b7cac963b0b909f8d
SHA1:
ab663e43c1e3b50768a420fded308294fcab69e5
SHA256:
634E32D89F9A924277ABAE67201151DDC4F187F6652F2082F180A9C3F5BE3DB4
File Size:
513.02 KB, 513024 bytes
|
|
MD5:
07e02395d2914117de967c4c2928e15d
SHA1:
92476a4dd82390cd3ca193d6a16dc571d4294318
SHA256:
C7491080BFB22895CDF0ED359AA5A91BC520942FCC6266B2798517D4E1E67666
File Size:
660.99 KB, 660992 bytes
|
|
MD5:
09dab795fb36c1042767cc2a44f732e6
SHA1:
a0ff9fb6f5924b0382939c72ca1755fd0cb1a8cb
SHA256:
E28CE1AC1CCAE7FEC631100FAAFD72212B20D244360381D12FDEEAD74FE58107
File Size:
545.79 KB, 545792 bytes
|
|
MD5:
87fb89eb2477d6c7c40a273e4476101b
SHA1:
f0a76b5ef15cc99276ffdf295a455f6c529dd12f
SHA256:
EC1043A95348FE740987BF7D694C147AA0424B3A6D86C00D809CD09CF0245AE3
File Size:
584.19 KB, 584192 bytes
|
|
MD5:
d693f61e0855f8f268f66c96a1047d9a
SHA1:
6221340d9af83c288f122123dd7555ebb8080d90
SHA256:
6AE9ECE57C890B647E3B6081F0B60A88A42CFB2F90178EF44233DDE9B1A223AA
File Size:
978.94 KB, 978944 bytes
|
|
MD5:
fd4d55624dba4952a37adbb75fffc15a
SHA1:
2584c43e651255d6fc7352478ffcdd55bb5f18da
SHA256:
044774D7581D945538518C0386273261467BCA589BA769F0AC1816D0012EDC38
File Size:
656.90 KB, 656896 bytes
|
|
MD5:
db47e73369f4ebfd9d69d72d37d41e82
SHA1:
4d5dce5f060085d0b1eb02ab2d2d0bbe084cda82
SHA256:
9FB7C786560DE398EB8500F0A706E3372B37D7B7B89E72F43F321101F119DE02
File Size:
646.66 KB, 646656 bytes
|
|
MD5:
b78498a5e8da6966845b165231d20a78
SHA1:
627b1302e59c366e551bbc196291d71c8d8d7df4
SHA256:
AE3182F1B46DAC986EEE515E0054C7643A533A2DB3DE1AEAB413CE47B3C58952
File Size:
523.78 KB, 523776 bytes
|
|
MD5:
f9a52e0da8c14de56a15c6a55982db0f
SHA1:
bfd53d3bd420a2398bf6aa164f5b1595d24a1f35
SHA256:
B84140B77F701DF4D1E1D0DA9A8A7243222BF11F49C1AB90245F6E2714B1F5B9
File Size:
556.54 KB, 556544 bytes
|
|
MD5:
321f51e6e530b499fc115f6f22ccc8d1
SHA1:
afa689ce8864f61c20c6125bb5001eefb13ca50c
SHA256:
A9105E9B924CFB5F72EA6F85873C263467124E44528B1EB7AFD7448657724455
File Size:
627.71 KB, 627712 bytes
|
|
MD5:
4030eecb2018bfbd7002a613aed1b1b3
SHA1:
1a4aac9434288ef48416300771edc4878b07fbfe
SHA256:
F35513B6B24D4417CB73882ED52CF20DF615AE335A303E0E4BC8B11F58ECF89E
File Size:
502.27 KB, 502272 bytes
|
|
MD5:
ce5d28424e5772508daffc99fae92035
SHA1:
e771a64ccd373c7be25b0121cad9e2f77349e61f
SHA256:
0DAF7873FEE9F6AD33A40B88E0BE55B88EA5744C958FED958A37183C7A5FF18B
File Size:
334.85 KB, 334848 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has been packed
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
Show More
|
| File Description |
|
| File Version |
Show More
|
| Internal Name |
Show More
|
| Legal Copyright |
|
| Legal Trademarks |
|
| Original Filename |
Show More
|
| Product Name |
Show More
|
| Product Version |
Show More
|
File Traits
- 2+ executable sections
- No Version Info
- packed
- VirtualQueryEx
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,168 |
|---|---|
| Potentially Malicious Blocks: | 1 |
| Whitelisted Blocks: | 2,136 |
| Unknown Blocks: | 31 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.M
- Babar.W
- Banker.GF
- Gamehack.BSB
- Injector.KPP
Show More
- Keylogger.DF
- Lamer.B
- Lumma.NB
- Malat.A
- Qhost.MA
- Sednit.D
- Swisyn.B
- Talsab.A
- Trojan.Kryptik.Gen.DFA
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| User Data Access |
|
| Anti Debug |
|