RTX RAT
A security incident involving CPUID exposed users to malicious software through its official website, cpuid.com. For a period of less than 24 hours, threat actors successfully manipulated download links to distribute infected versions of widely used hardware monitoring tools.
The compromise occurred between April 9 at 15:00 UTC and April 10 at 10:00 UTC, during which legitimate installer links were intermittently replaced with malicious redirects. Importantly, CPUID confirmed that its original signed binaries remained intact, as the breach stemmed from a secondary feature, essentially a side API, that caused the website to randomly display harmful links rather than altering the core software itself.
Table of Contents
Malicious Infrastructure: Rogue Domains Behind the Attack
Investigations by cybersecurity researchers identified several domains used to host and deliver the trojanized payloads. These rogue websites played a central role in redirecting unsuspecting users to compromised downloads:
- cahayailmukreatif.web[.]id
- pub-45c2577dbd174292a02137c18e7b1b5a.r2[.]dev
- transitopalermo[.]com
- Vatrobran[.]hr
These domains formed part of a broader infrastructure designed to support malware distribution and command-and-control operations.
Stealthy Delivery Mechanism: DLL Side-Loading Abuse
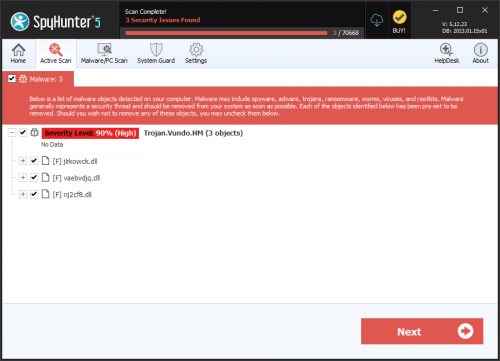
The attackers employed a well-known evasion technique called DLL side-loading. The malicious packages were distributed as both ZIP archives and standalone installers, each containing two components: a legitimate, signed executable and a rogue dynamic link library named 'CRYPTBASE.dll.'
By exploiting the trust placed in signed binaries, the malicious DLL was loaded during execution, enabling covert compromise. Before initiating further actions, the malware conducted anti-sandbox checks to avoid detection in analysis environments. Once these checks were passed, it contacted an external server to retrieve additional payloads.
STX RAT Deployment: A Versatile Post-Exploitation Tool
The ultimate objective of the campaign was to deploy the STX RAT, a powerful remote access trojan equipped with hidden virtual network computing (HVNC) capabilities and extensive data theft functionality.
This malware enables attackers to maintain persistent control over infected systems and execute a wide array of post-exploitation activities, including:
- In-memory execution of EXE, DLL, PowerShell scripts, and shellcode
- Reverse proxying and network tunneling
- Remote desktop interaction and surveillance
Such capabilities make STX RAT particularly dangerous in both individual and enterprise environments.
Campaign Overlap: Links to Earlier FileZilla Attacks
Analysis revealed that the Command-and-Control (C2) infrastructure used in this incident had been previously associated with a separate campaign involving trojanized installers of FileZilla. The reuse of the same server configurations and communication domains strongly indicates operational overlap between the two campaigns.
This repetition of tactics, techniques, and infrastructure provided valuable indicators for detection and attribution.
Long-Term Operation: A 10-Month Campaign Timeline
Further investigation suggests that the CPUID breach is part of a broader campaign that began in July 2025. The earliest known malware sample, identified as 'superbad.exe,' was observed communicating with a command-and-control server at 95.216.51.236.
Security experts assess that the threat actor is likely Russian-speaking and may be financially motivated or functioning as an initial access broker, an entity that specializes in gaining footholds in systems and selling that access to other cybercriminals.
Impact Assessment: Global Reach with Diverse Victims
The attack has affected more than 150 confirmed victims, predominantly individual users. However, organizations across multiple industries have also experienced compromise, including retail, manufacturing, consulting, telecommunications, and agriculture sectors.
Geographically, the majority of infections have been identified in Brazil, Russia, and China, indicating a broad and opportunistic targeting strategy.
Operational Weaknesses: Errors That Led to Detection
Despite the scale of the campaign, several operational security failures significantly undermined the attackers' effectiveness. The reuse of identical infection chains, STX RAT payloads, and command-and-control domains from earlier campaigns made the activity easier to track and correlate.
These shortcomings suggest relatively low sophistication in malware development and deployment practices. As a result, defenders were able to detect the watering hole attack quickly after its initiation, limiting its overall impact and exposure window.