RedStar Ransomware
Malware threats continue to evolve in sophistication, making it increasingly important for users and organizations to safeguard their devices and data. Ransomware attacks in particular can cripple personal systems and corporate networks by encrypting valuable files and demanding payment for their release. One recently observed threat, known as RedStar Ransomware, demonstrates how modern attackers combine simple infection tactics with damaging encryption capabilities to pressure victims into paying a ransom. Understanding how such threats operate and how they spread is essential for strengthening defenses against them.
Table of Contents
The Emergence of RedStar Ransomware
Security researchers identified RedStar Ransomware during an investigation into suspicious malware samples circulating online. Once executed on a compromised device, the ransomware begins encrypting files stored on the system. During this process, each affected file is renamed with the '.RedStar' extension. For instance, a file originally named '1.png' becomes '1.png.RedStar,' while '2.pdf' is converted to '2.pdf.RedStar.' This renaming indicates that the files have been processed by the encryption routine and are no longer accessible in their original form.
Following the encryption stage, the malware drops a ransom note named 'READ_ME.txt' on the infected system. The message informs victims that their files have been locked and cannot be opened without a special decryption tool controlled by the attackers. As is common with ransomware campaigns, the attackers attempt to pressure victims into contacting them to negotiate payment.
The Ransom Demand and Attacker Communication
The ransom note associated with RedStar contains instructions for victims to recover their data. It claims that the only way to regain access to encrypted files is to obtain a decryption key from the attackers. Victims are asked to make a payment in Bitcoin, although the message humorously suggests that 'some good coffee' could also suffice. Despite the joking tone, the threat remains serious because encrypted files typically cannot be restored without the correct decryption key.
The attackers provide a contact email address at 'redstarme@proton.me', and encourage victims to reach out after making the payment. However, cybersecurity professionals strongly discourage paying ransom demands. There is no guarantee that attackers will deliver a working decryption key, and paying only encourages further cybercriminal activity.
In many cases, the safest recovery method is restoring files from unaffected backups, assuming such backups exist and were not compromised during the attack.
How RedStar and Similar Ransomware Spread
Ransomware rarely spreads randomly; instead, attackers rely on multiple infection techniques designed to trick users or exploit weaknesses in systems. RedStar can potentially infiltrate devices through several common channels used by cybercriminals:
- Deceptive emails containing malicious attachments or links
- Exploitation of outdated software vulnerabilities
- Fake software cracks, key generators, or pirated applications
- Malicious advertisements and fraudulent technical support scams
- Infected USB drives or compromised websites
- Peer-to-peer file sharing networks and third-party downloaders
Malware payloads are frequently disguised within files that appear harmless. Executables, compressed archives, scripts, and documents such as Office or PDF files are commonly used as carriers. Once opened or executed, the ransomware silently activates and begins its encryption routine.
Why Immediate Removal Is Critical
When ransomware remains active on a system, the damage may not stop with the first round of file encryption. In some cases, malware can continue encrypting newly created files, attempt to spread across a network, or download additional malicious components.
Because of this risk, infected systems must be isolated from networks as quickly as possible. Removing the ransomware prevents further encryption activity and reduces the likelihood of the infection spreading to other devices within the same environment. Even if files cannot immediately be recovered, stopping the malware limits the scale of the incident.
Essential Security Practices for Stronger Defense
Preventing ransomware infections requires consistent cybersecurity habits and layered defenses. Users and organizations can significantly reduce the risk of infection by implementing the following security practices:
- Maintain regular offline or cloud backups so files can be restored without paying attackers
- Keep operating systems, browsers, and applications fully updated to eliminate known vulnerabilities
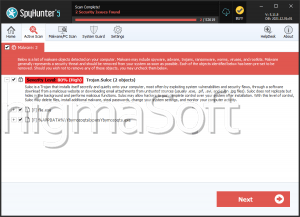
- Use reputable security software with real-time protection and keep its signatures updated
- Avoid downloading cracked software, unofficial installers, or files from untrusted sources
- Carefully inspect emails before opening attachments or clicking links
- Disable macros in Office documents unless absolutely necessary
- Restrict the use of removable media and scan USB devices before accessing their contents
- Educate users about phishing attacks and social engineering tactics
Beyond these technical measures, cybersecurity awareness plays a major role in defense. Many ransomware attacks succeed because users unknowingly execute malicious files or trust fraudulent messages. Building cautious digital habits helps eliminate many of the opportunities attackers rely upon.
Final Thoughts
RedStar Ransomware illustrates how even relatively straightforward malware can cause severe disruption once it infiltrates a system. By encrypting files and demanding payment for their recovery, attackers attempt to exploit urgency and panic. However, understanding how such threats operate and implementing strong security practices can significantly reduce the likelihood of falling victim to them.
Consistent system updates, cautious online behavior, and reliable backups remain among the most effective defenses against ransomware. When these safeguards are in place, even a successful intrusion becomes far less damaging, ensuring that critical data remains recoverable without yielding to cybercriminal demands.