Ransom-AAY.gen.b
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
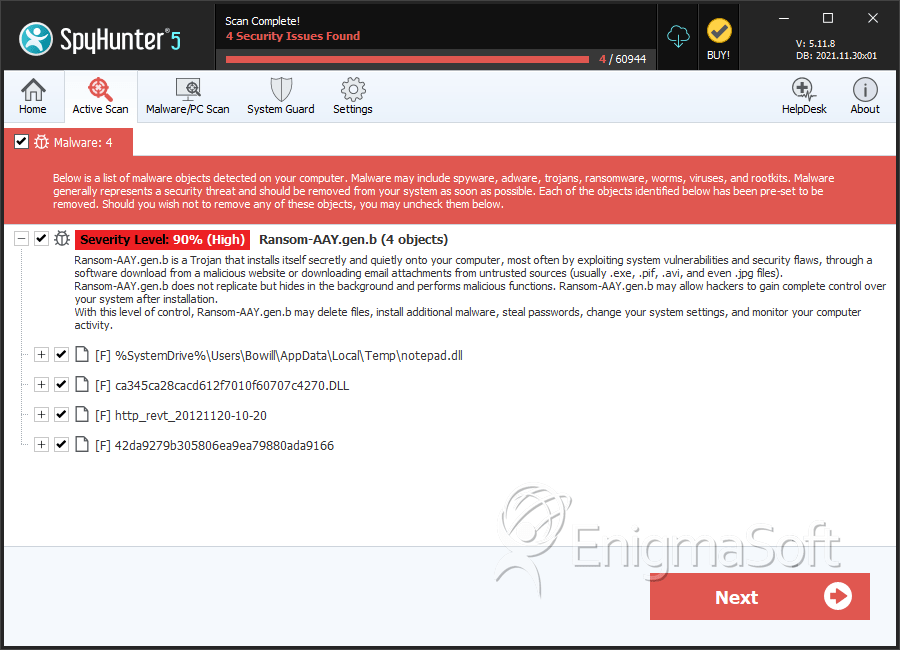
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 4 |
| First Seen: | December 28, 2012 |
| OS(es) Affected: | Windows |
Ransom-AAY.gen.b is a police ransomware Trojan. Ransom-AAY.gen.b has dozens of variants, all of which carry the same basic scam. Ransom-AAY.gen.b is used to blackmail computer users by making them believe that they must pay a fine because of a supposed offense on their part. Basically, Ransom-AAY.gen.b blocks access to the infected computer and covers the desktop with a full screen message claiming that the victim's computer was blocked by the police.
Ransom-AAY.gen.b variants are highly localized and will often impersonate the police force corresponding to the victim's country. Typically, Trojan droppers associated with Ransom-AAY.gen.b variants will detect the victim's IP address and then install a variant of a Ransom-AAY.gen.b Trojan that corresponds to the victim's geographical location. Once installed, the Ransom-AAY.gen.b Trojan makes certain changes to the Windows Registry that allow Ransom-AAY.gen.b to do the following:
- Ransom-AAY.gen.b variants disable the Task Manager in order to prevent computer users from bypassing the full screen ransom message.
- Ransom-AAY.gen.b will also lock its full screen window, preventing computer users from moving it or closing it in order to gain access to their Desktop.
- Ransom-AAY.gen.b will also disable the Task Bar and Start Menu and other essential Windows components.
Since Ransom-AAY.gen.b changes the Windows Registry to ensure that Ransom-AAY.gen.b loads automatically whenever the victim starts up the infected operating system, Ransom-AAY.gen.b effectively prevents the computer user from using their own computer.
The Ransom-AAY.gen.b ransom note requests the payment of a penalty in order to regain control of the infected computer. However, ransomware Trojans in the Ransom-AAY.gen.b family will not be disabled by paying their 'fine.' Because of this, ESG security researchers strongly recommend against following the instructions in the ransom message, even if you are in a hurry to regain control of your computer. One of the aspects that make Ransom-AAY.gen.b unique in relation to other ransomware families is that Ransom-AAY.gen.b uses a web browser Window to display its malicious message. This window is modified to fill up the whole screen and prevent the victim from accessing any content on their computer. Although the default versions of Ransom-AAY.gen.b use Internet Explorer by implementing a malicious DLL file, ESG security researchers have observed variants that use other web browsers already installed on the victim's computer (such as Chrome or Firefox).
Table of Contents
Aliases
14 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Trj/OCJ.A |
| Fortinet | W32/Kryptik.ALTS!tr |
| Ikarus | Trojan-Ransom.Win32.Foreign |
| AhnLab-V3 | Dropper/Win32.Injector |
| Sophos | Troj/Swisyn-AW |
| McAfee-GW-Edition | GenericTRA-BJ!52B9B8BC9042 |
| AntiVir | TR/Graftor.44588 |
| Comodo | UnclassifiedMalware |
| BitDefender | Gen:Variant.Graftor.44588 |
| Kaspersky | Trojan-Dropper.Win32.Injector.fvyp |
| Avast | Win32:Dropper-gen [Drp] |
| Symantec | Trojan.Gen.2 |
| K7AntiVirus | Trojan |
| McAfee | Ransom-AAY.gen.b |
SpyHunter Detects & Remove Ransom-AAY.gen.b
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | notepad.dll | 52b9b8bc9042bee1ff7ddf3b81f59570 | 4 |
| 2. | [startup folder]\[RANDOM FILENAME].dll | ||
| 3. | Lock.dll | ||
| 4. | [STARTUP FOLFER]\runctf.lnk | ||
| 5. | %ALLUSERSPROFILE%\Application Data\[RANDOM FILENAME].[dll] | ||
| 6. | [startup folder]\[RANDOM FILENAME].dll.lnk | ||
| 7. | [RANDOM FILENAME].dll.lnk | ||
| 8. | ca345ca28cacd612f7010f60707c4270.DLL | ca345ca28cacd612f7010f60707c4270 | 0 |
| 9. | http_revt_20121120-10-20 | 96578f08ae75e5d87eac002c116569e2 | 0 |
| 10. | 42da9279b305806ea9ea79880ada9166 | 42da9279b305806ea9ea79880ada9166 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.