PWS-Zbot.gen.cc
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 360 |
| First Seen: | November 30, 2010 |
| OS(es) Affected: | Windows |
Beware of an email scam involving the Trojan PWS-Zbot.gen.cc. This email scam consists of an email claiming to originate from DHL, the popular international courier service. This fraudulent email will try to convince the victim that there is a shipment on the way and that an attached file should be opened in order to track the package and obtain more information on the shipment. However, opening the attached file contained in this bogus email from DHL will cause the victim's computer to become infected with the PWS-Zbot.gen.cc Trojan. It is easy to become fooled by this email scam, because the criminals behind PWS-Zbot.gen.cc have managed to spoof an email address that looks quite authentic, appearing to originate from an official DHL server. It is because of this that ESG malware analysts strongly recommend never opening links or downloading attachments contained in unexpected emails, even if they appear to come from a legitimate source.
The fake email from DHL is a fairly passable imitation of legitimate emails from this courier company. It also contains links to the official, legitimate DHL website. The language within this email is also pretty typical of official emails from this company. This is why caution should be exercised when dealing with unexpected emails. Even then, it is highly unlikely that a legitimate email from DHL would prompt a user to open an attached file in order to receive more information on a particular shipment. These kinds of practices should trigger your alarms, since they are typical of how most phishing scams and email frauds operate on a computer.
The Trojan contained in this fake DHL email, PWS-Zbot.gen.cc, also detected as Win-Trojan/Obfuscated.Gen, is a fairly typical backdoor Trojan. PWS-Zbot.gen.cc is designed to take over your computer system, connect to a remote server and put your computer system in the hands of a criminal. Using the PWS-Zbot.gen.cc infection, a hacker can control your computer system remotely. This level of unauthorized control can be used to perform illegal acts involving the infected computer system. Some examples of activities associated with a PWS-Zbot.gen.cc infection include using the infected computer to send out spam email (including additional copies of the fake DHL email scam), using the infected machine to perform DDoS attacks on specific targets and to cover up other criminal activities such as child pornography rings or money laundering. Computer users should be certain that their anti-malware software is protecting their systems from the PWS-Zbot.gen.cc Trojan.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Generic27.BNIO |
| Fortinet | W32/Injector.PRI |
| Ikarus | Trojan-Ransom.Win32.Mbro |
| AhnLab-V3 | Dropper/Win32.Injector |
| Antiy-AVL | Trojan/Win32.Mbro.gen |
| Sophos | W32/VB-FWA |
| DrWeb | Trojan.Packed.22445 |
| Kaspersky | Trojan-Ransom.Win32.Mbro.dcw |
| ClamAV | Trojan.Mbro-2 |
| eSafe | Win32.Injector.Pri |
| Avast | Win32:Rootkit-gen [Rtk] |
| NOD32 | Win32/MBRlock.D |
| McAfee | W32/Worm-FCF!0E0F3848F352 |
| CAT-QuickHeal | TrojanRansom.MBro.dcw |
| AVG | SHeur3.CGGD |
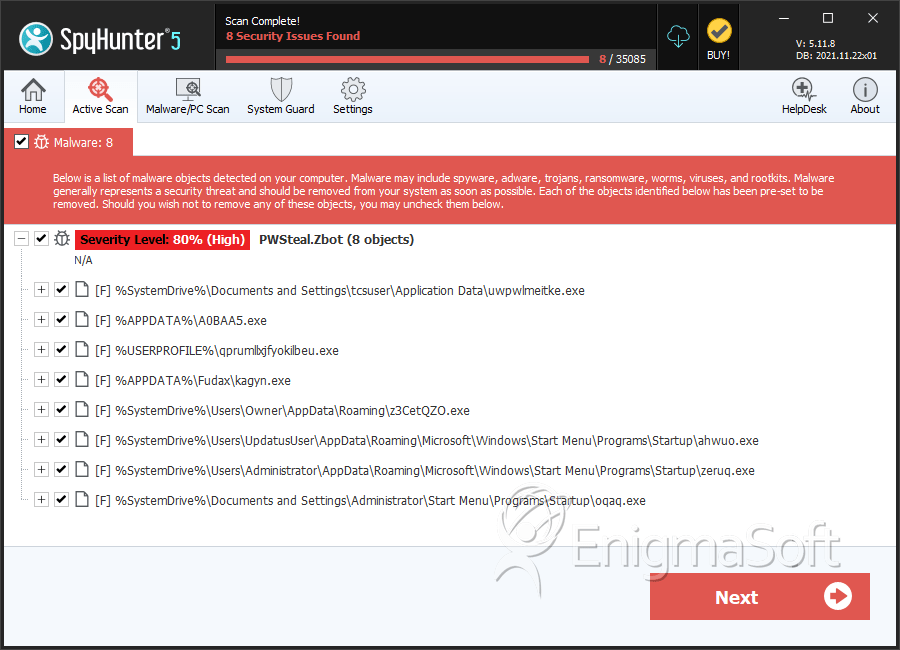
SpyHunter Detects & Remove PWS-Zbot.gen.cc
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | uwpwlmeitke.exe | 87cc0a0b77a8d837a2a70c20f3bbcc7d | 96 |
| 2. | A0BAA5.exe | 8b07fe8f533ab8e02daa3eaae6612e1c | 45 |
| 3. | qprumllxjfyokilbeu.exe | c8471ea9a7c40e586ec0f21e40e21e9e | 27 |
| 4. | kagyn.exe | d7a2a72bbae0760f4772bffc3ed116d4 | 13 |
| 5. | z3CetQZO.exe | 476fda6471c874c584725a4f8cab7555 | 13 |
| 6. | ahwuo.exe | a8b9ddd0d17f35fe5d4c35a89ded2798 | 6 |
| 7. | zeruq.exe | 81227ea07cd172180698580b41c4e109 | 6 |
| 8. | oqaq.exe | 12dfa07d9d0d5de46d4681cb0ccee952 | 5 |
| 9. | mesoa.exe | c631b06107131e1891cf64bcee0f8fc0 | 4 |
| 10. | ikaf.exe | 42fdfd374f3b6ac6c9621325c5d370bd | 3 |
| 11. | apikndss.exe | 0e0f3848f352da113f65e3787df9fc3b | 3 |
| 12. | lozai.exe | f4679f83603bc7ae08ab5517d7065ac6 | 3 |
| 13. | iqzehy.exe | 761eda071af0c7d9841ccc78050ceffb | 2 |
| 14. | ytze.exe | 490763428fd9abf379638aae5bccfc41 | 2 |
| 15. | eHRFhkpXr.exe | 49509701af157a56409774224d99f790 | 2 |
| 16. | 366F95.exe | 1bfef062e53f54d5beb4413ddcc683b0 | 2 |
| 17. | msrerkua.scr | 95b992ee6f22221c0d9fa482d050b916 | 2 |
| 18. | svd.exe | 6f022949743f2ea44116cebfdb9ff232 | 2 |
| 19. | ekeww.exe | 2a2580e77edf6d1a80e49934bb0e1914 | 1 |
| 20. | pevoco.exe | 8df0c89648bd8eb80c82c63bd9bffcb6 | 1 |
| 21. | gyokq.exe | 1ac6598d68f7f7c50f9589132c5bb9f0 | 1 |
| 22. | svcnost.exe | ba9066bb27344c4a74a67f51fc51e258 | 1 |
| 23. | yrahiw.exe | f47751d13cf32bd1f6d8e6834fdc0865 | 1 |
| 24. | xauras.exe | e6bda8657f7e1e16755c8037b8620ee2 | 1 |
| 25. | UpgradeHelper.exe | ad1a6b291341f57a121783a319a3404d | 1 |
| 26. | 83ALuOH.exe | 40f55b80aa1b8900197904e4494fec4e | 1 |
| 27. | skype.dat | 06956b0f41300d476fb83fc63e64bc97 | 1 |
| 28. | file.exe | 1b116181b38b3b414da02f09ea142e9e | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.