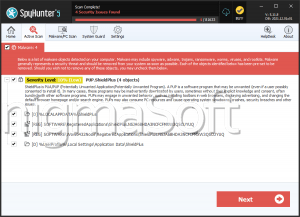
PUP.IBryte
PUP.IBryte is a PUP, or Potentially Unwanted Program. Despite not being considered as risky as other threats like Trojans, security analysts consider that PUP.IBryte and similar PUPs are seriously disruptive because they may interfere with your online activities, compromise your privacy and expose your computer to other PUPs or more harmful forms of threats. It is also important to note that the presence of PUP.IBryte on your computer may indicate that other PUPs or even more threats are present on your machine. In most cases, PUP.IBryte may be installed after carelessly downloading and installing a free program from an unreliable source. Malware analysts recommend the immediate removal of PUP.IBryte and similar PUPs. Although PUP.IBryte may be uninstalled like most other applications, it is important to use a strong, reliable anti-malware application to scan the affected computer in search for any possible threat or unwanted files that may have entered the affected computer as a consequence of a PUP.IBryte infection.
Table of Contents
Usual Symptoms and Issues Related to PUP.IBryte
If PUP.IBryte is installed on your PC, PUP.IBryte may cause a variety of symptoms that are commonly associated with PUPs and similar types of infections. Listed below are known symptoms that have been linked to PUP.IBryte:
- Among the most common problems linked to PUP.IBryte is the occurrence of Web browser redirects. The computer user's Web browser is forced to visit websites associated with PUP.IBryte repeatedly. PUP.IBryte takes over the victim's Web browser, causing computer users to lose control over the websites they visit. PUP.IBryte redirects may lead to low quality search engines or websites containing high quantities of suspicious advertisements.
- Pop-up windows and alerts have also been linked to PUP.IBryte. PUP.IBryte advertisements and pop-ups are usually designed to expose computer users to marketing material and profit at the expense of computer users.
- PUP.IBryte makes unauthorized changes to the victim's Web browser that include changing the victim's home page and default search engine to ensure that the computer user is exposed to websites associated with PUP.IBryte repeatedly.
- PUP.IBryte and associated components may cause performance problems on affected computers. Content associated with PUP.IBryte may cause a computer or Web browser to slow down, crash or freeze frequently, and take an extraordinarily long time to load Web pages or carry out simple tasks.
Aliases
3 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| VIPRE | Gen:Variant.Application.Kazy.427497 |
| SUPERAntiSpyware | Adware AdPlugin.ZK |
| FireEye | Win32:IBryte-EE [PUP] |
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. |
C:\Documents and Settings\ |
||
| 2. |
C:\Documents and Settings\ |
||
| 3. |
C:\Documents and Settings\ |
||
| 4. | player-chrome.exe | f522e71acc6861f25aa7459c22c8d89e |
Analysis Report
General information
| Family Name: | Adware.Ibryte |
|---|---|
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
0ac57e9eb6a0d4cd2d24f0ab4c614def
SHA1:
fefa50a3d1b03ca6e7d166a82dc1a35aaca79c85
File Size:
1.06 MB, 1059480 bytes
|
|
MD5:
72cce165ad699564a574c200078ae16a
SHA1:
37302c65a74b877f67aee8593aaf380f36f0ef53
SHA256:
B914229619EAC8C83E1E6421E0507638996BD4A2247097DF32827AE36E7ED217
File Size:
1.06 MB, 1059480 bytes
|
|
MD5:
354da39163802fa7c67ebf519090b7c3
SHA1:
66f1c484d9b5f2b2df8609c47ec5bbf421dd72b8
SHA256:
3F41CBE88853FD8E773E9FD2CB43BACA7226B842834C7D4D6552F55E621C116E
File Size:
230.78 KB, 230776 bytes
|
|
MD5:
4531bc12f56dfc82613d7a30f1b05e67
SHA1:
5e2a8cd1506107b4439d12a13322cf41894e0422
SHA256:
7508267C4677752376EC5EFE1B93D3F14AC36EA4EDDEE740D3FFE221308B7917
File Size:
1.97 MB, 1969448 bytes
|
|
MD5:
32add31496125bd12755165352ef2ad2
SHA1:
78e016a4c20374734e48434de6ca80c1a74ec40e
SHA256:
27D7E98E766ED16E633E861B04F9F719A3C1506DFAD4C7B3605E292037860371
File Size:
229.75 KB, 229752 bytes
|
Show More
|
MD5:
5928d36aea4bbaaa5c1f030fe59d59c5
SHA1:
2aaceaf4d0bc408a3f4be724726e32ca12dc4413
SHA256:
2C13709A37D321CAAF71067F06F29617327A0986EADA517B71DB12655DAEA259
File Size:
97.14 KB, 97144 bytes
|
|
MD5:
9bea567117b1a3d782f107c13c1ff5e4
SHA1:
c339749d9f912235ce38c62e2293297520cc7c6b
SHA256:
3E98D8585FC9A24616C2E14C3358C77C5AA55A3711A483F4F1C7628A854D059C
File Size:
229.75 KB, 229752 bytes
|
|
MD5:
d08d70f8a8159391f9617a2f7cc85572
SHA1:
1073cfc7f66c2e91f918b8ebde650ece141c3ca8
SHA256:
2A612FB87BCA508BA2BEF1E389D837183C7ADE4A822221D639837C8293564DA9
File Size:
1.07 MB, 1066648 bytes
|
|
MD5:
b43a2ff38e442c2d51d3e8a4518c1863
SHA1:
dc2938e13d5add921b42761a8cfe8ca2ba16018b
SHA256:
BB98544AB9904336F78B5C14D3C24167ABFDB80689A217A813CB03FFB90B1E46
File Size:
273.78 KB, 273784 bytes
|
|
MD5:
eae4814e9e041b53ca685a2f86709be2
SHA1:
94969ec98b07acbb6455f1eeb462a92156c019e3
SHA256:
3C75EE2BA573B9737DA5456DE054D3171E09E5F992CF1C4293264524E8059684
File Size:
226.17 KB, 226168 bytes
|
|
MD5:
31079b5caece0ab2ada85261321cd382
SHA1:
dc11855a7867acea347c833dd06b3cdca4b68c39
SHA256:
089FA110FD46E0306CA44B9AA73B227459B7D74A20B1F6FB7475E9B85F67C4D0
File Size:
57.87 KB, 57870 bytes
|
|
MD5:
80f8f02aa83615d96410af1c6aa4dde7
SHA1:
b2d00f626459e31b6163e7b71c7f0417cd84ce26
SHA256:
B3970CA57A928A5542143568C991A3900599DBCF6530E7CF2C98ECC58045C765
File Size:
92.54 KB, 92536 bytes
|
|
MD5:
547b5ca70ffb68a6d3c713174d86ee48
SHA1:
8d46e07c86bc4e19ed4837f7799c873e75f7d3b0
SHA256:
593F883AC66B1EA5DB7CA373EE2F970A01A45EA73D9EAF4F92103A7D732C3739
File Size:
227.19 KB, 227192 bytes
|
|
MD5:
6c18b37012c1e3975e40c0c0672656f4
SHA1:
5e4f4de46ad78d3fe66c45954e63ec5200898e9f
SHA256:
B2675E77C5F92242C159DA6651517A5841BCE8B67047B45A83F5C2E65F4ACA49
File Size:
78.12 KB, 78120 bytes
|
|
MD5:
c0a34b81da02e8d621d90427daad53f4
SHA1:
18b2c3da4edaef013be6621a99cd5537495bc4c2
SHA256:
A612E36E71578AAEDB5690FDA58ADFDAE83EFE7A2FEAEF8DFC6ABF53F5655B9C
File Size:
232.82 KB, 232824 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Boot Compute | AddTrust External CA Root | Root Not Trusted |
| System Applet | AddTrust External CA Root | Root Not Trusted |
| Premium Installer | VeriSign Class 3 Public Primary Certification Authority - G5 | Root Not Trusted |
| TINY INSTALLER | VeriSign Class 3 Public Primary Certification Authority - G5 | Root Not Trusted |
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 934 |
|---|---|
| Potentially Malicious Blocks: | 14 |
| Whitelisted Blocks: | 905 |
| Unknown Blocks: | 15 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Brute.BH
- Brute.BHA
- Chapak.HBW
- Chapak.HBX
- Rozena.H
Show More
- Trojan.Agent.Gen.VN
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nsqa4e6.tmp\image.png | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsqa4e6.tmp\nsisdl.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\~nsua.tmp\un_a.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | *1\??\C:\Windows\SystemTemp\MicrosoftEdgeUpdate.exe.old122e4��*1\??\C:\Windows\SystemTemp\CopilotUpdate.exe.old12352��*1\??\C:\P | RegNtPreCreateKey |
| HKCU\software\microsoft\internet explorer\main::start page | https://www.google.com/ | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Network Wininet |
|
| Anti Debug |
|
| User Data Access |
|
| Process Shell Execute |
|
| Network Winsock2 |
|
| Network Winsock |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"C:\Users\Rwkcmmsg\AppData\Local\Temp\~nsuA.tmp\Un_A.exe" _?=c:\users\user\downloads\
|