Plasma RAT
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
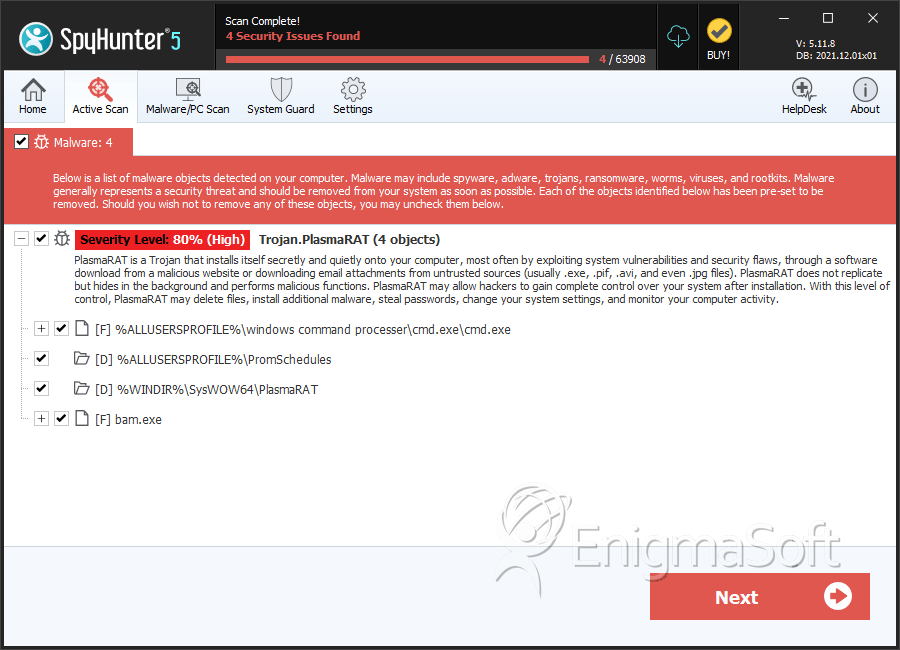
| Threat Level: | 80 % (High) |
| Infected Computers: | 218 |
| First Seen: | January 30, 2017 |
| Last Seen: | May 13, 2023 |
| OS(es) Affected: | Windows |
The Plasma RAT is a malware that is recognized by most AV companies on the cybersecurity scene as of the time of writing this article. The Plasma RAT was introduced to the wide as early as the winter of 2013. The Plasma RAT is a Remote Access Trojan that received many updates up until the winter of 2016 when the project entered a dormant stage of development. The Plasma RAT is classified as a mid-tier Remote Access Trojan thanks to its wide array of features, which are rivaled by a small number of similar tools like OzoneRAT. The Plasma RAT can be downloaded on some Dark Web domains and some Github pages like h[tt]ps://github[.]com/mwsrc/PlasmaRAT for educational purposes as described on the Github post mentioned here. There are threat actors that continue to use the Plasma RAT given its stable performance and support for advanced features, which do not come cheap in tools of the same class. A concise review of Plasma RAT's features is bound to include the following:
- Ability to Edit Hosts File
- Ability to Execute Scripts
- Ability to View Current Network Connections
- Access the Task Manager
- Edit Startup Program Entries
- Install Hooks on Local Processes (Web Browsers, IM Clients, Email Managers)
- Install a Cryptocurrency Miner to Compromised Machines
- Launch DDoS Attacks from Specific Ports at Targeted Servers
- Load a Keylogger
- Local Windows Account and Web Browsers Password Recovery
- Move, Edit, Create and Delete Files on the Local Disks
- Open Chat Windows Between Client/Server
- Remote Desktop and Webcam
- Run Website Stress Testing
The Plasma RAT allows the threat actors to hijack system resources on infected machines and mine digital money/cryptocurrencies like Litecoin (h[tt]ps://litecoin[.]com) and Dogecoin (h[tt]p://dogecoin[.]com). Compromised users may notice increased CPU load and programs that crash often. Also, the Plasma RAT may launch a multitude of network connections at the same time and cause Internet connection errors. The malware payload can be distributed via fake updates to Flash, Java, pirated copies of PC games, and links to insecure pages. It is advised to clean the devices affected by the Plasma RAT using a respected anti-malware solution.
Table of Contents
SpyHunter Detects & Remove Plasma RAT
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | cmd.exe | 39a31c5ebcaf67118a443cf239fbeb2c | 10 |
| 2. | bam.exe | 13604e19ebbd95974841a789d60f9859 | 0 |
Registry Details
Directories
Plasma RAT may create the following directory or directories:
| %ALLUSERSPROFILE%\PromSchedules |
| %WINDIR%\SysWOW64\PlasmaRAT |

