Ook.gg
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 3,320 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 12,857 |
| First Seen: | October 26, 2023 |
| Last Seen: | November 8, 2025 |
| OS(es) Affected: | Windows |
Ook.gg is a search engine that gains visibility through the distribution of unauthorized browser extensions and browser hijacking tactics. These dubious extensions, once installed, manipulate your web browser's settings, effectively reconfiguring it to redirect all search queries automatically through Ook.gg. This means that any search you perform on your browser will be channeled through Ook.gg, even if you didn't intend for it to be your default search engine.
Table of Contents
Browser Hijackers Often Promote Dubious Sites Like Ook.gg via Intrusive Means
After browser hijackers are installed on the users' devices, they usually carry out unauthorized modifications to key settings within the user's Web browser, all without the user's consent. These adjustments encompass crucial aspects of the browser's functionality, which include its default search engine, homepage, and the behavior of the new tab page.
Regarding the default search engine, browser hijackers often execute one of the most prevalent changes by tampering with this setting. They take it upon themselves to replace the user's favored search engine, be it Google, Bing, or another reputable option, with their own preferred and often questionable Web address, such as Ook.gg. This swap ensures that any search queries made through the browser will inevitably be routed through the promoted Web address, granting the browser hijacker substantial visibility and control over the user's search activity.
In addition to meddling with the search engine, browser hijackers can also exert influence over the user's homepage and new tab page. These settings can be forcefully configured to launch a specific website, frequently the one the hijacker aims to promote. This forceful alteration is a deliberate strategy aimed at ensuring that the user is continuously exposed to their chosen web address, ultimately increasing its prominence and maintaining a firm grip on the user's online experience.
Furthermore, when users initiate Web searches or enter website addresses directly into the browser's address bar, the browser hijacker introduces an extra layer of interference. It orchestrates a process wherein the user's request is redirected to the dubious Web address, such as Ook.gg. Users may observe with frustration that their initially preferred search engine and homepage have been stealthily replaced, all occurring without their knowledge or consent.
This kind of behavior further underscores the intrusive nature of browser hijackers, which can disrupt the user's online activities, compromise their online privacy, and potentially expose them to various security risks.
PUPs (Potentially Unwanted Programs) and Browser Hijacker Utilize Various Shady Tactics for Their Distribution
- Bundling with Freeware: This is one of the most prevalent methods used by PUPs and browser hijackers. They are bundled with seemingly legitimate and free software downloads, like PDF readers, video players, or system utilities. Users who rush through installation processes may inadvertently agree to install these additional programs without realizing it. PUPs and browser hijackers often utilize a range of shady tactics for their distribution. These tactics can be deceptive and intrusive, aiming to catch users off guard and encourage them to install these unwanted and often harmful applications. Here's an explanation of some of the common tactics employed by PUPs and browser hijackers:
- Misleading Advertisements: PUPs and browser hijackers may be promoted through misleading or enticing advertisements, often appearing as pop-ups or banners on various websites. These advertisements may claim to offer useful features or software updates, but in reality, they lead to the installation of unwanted programs.
- Phony Software Updates: Users are sometimes tricked into believing they need to update their software or browsers. PUPs and browser hijackers often disguise themselves as legitimate updates, exploiting the user's trust in keeping their software current.
- Rogue Websites: Some websites may host fraud-related scripts or downloads that trigger the installation of PUPs or browser hijackers without the user's consent. Visiting such sites, especially those of dubious origin, can result in these unwanted installations.
- Social Engineering: In some cases, users are manipulated through social engineering tactics. They might receive fake security alerts or warning messages, urging them to install software to resolve an issue or to enhance their system's performance. These messages create a sense of urgency and pressure users into installing unwanted programs.
- Email Attachments and Links: PUPs can be distributed through unsafe email attachments or links in phishing emails. Users may be encouraged to download an attachment or click on a link that triggers the installation of unwanted software.
In summary, PUPs and browser hijackers employ various deceptive and manipulative techniques to infiltrate users' systems. It is crucial for users to exercise caution when downloading software, keep their browsers and security software up to date, and be wary of unsolicited downloads, especially from untrusted sources. Additionally, installing reputable ad-blockers and anti-malware tools can provide an added layer of defense against these invasive tactics.
Ook.gg Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
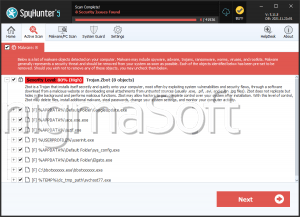
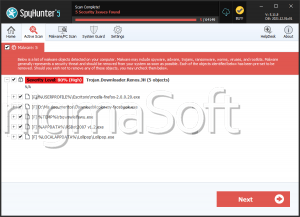
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | vcpkhost.exe | 1ad1df8533b68c889b81c02208de46e0 | 3,072 |
URLs
Ook.gg may call the following URLs:
| ook.gg |