OnionDuke
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 9 |
| First Seen: | November 14, 2014 |
| Last Seen: | October 23, 2020 |
| OS(es) Affected: | Windows |
OnionDuke is a threat infection that may carry its attacks using the Tor network, a network that uses techniques that allow computer users to hide their addresses and locations very effectively. A Tor exit node in Russia was identified as responsible for distributing threatening Windows executable files. PC security researchers, having investigated this Tor network node identified a threat family that was originated in Russia and known as MiniDuke. This threatening family has been involved in attacks targeting NATO and European government targets! In this particular case the threat used is not precisely a MiniDuke variant. Rather, it is a separate family of threatening software that has started to become known as OnionDuke. This name originates from OnionDuke's relationship to the Tor network (which uses .onion addresses) and its relationship to the MiniDuke family of threats.
Table of Contents
Infection Methods Used by OnionDuke
Whenever computer users try to download an executable file using the threatening Tor exit node, instead of receiving their intended file, they may also receive an additional 'gift'. The executable file may be wrapped in a second, threatening executable, which may be embedded into the original executable file. Since this is a wrapper that is added to the original file, this may allow the threatening file to bypass certain security checks. Once the file is executed, the wrapper may execute the second file, working in the background and making it seem as if everything is normal. In fact, PC security analysts have noted that OnionDuke may work in the background to carry out its threat attack. PC security analysts have noted that OnionDuke is a Trojan dropper that is disguised as an embedded GIF image file. In fact, it is an encrypted DLL file that may carry out threatening attacks on infected computers.
How OnionDuke Carries out Its Attack
When the OnionDuke DLL file is executed, OnionDuke may try to contact a remote server to receive its configuration data. This data may include instructions to download and install other threats on the computer. PC security researchers have noted that the domains that OnionDuke contacts are not threatening Web servers but, instead, genuine websites that have been corrupted by third parties so that they may form part of this attack without their owners' knowledge. PC security analysts have been able to identify certain other components of the OnionDuke attack. For example, malware analysts have noted that OnionDuke may collect information such as online passwords or credit card numbers from the infected computer. OnionDuke also may have components that are designed to gather information about the infected computer's security software, firewall or other protections. In some cases, these components may be downloaded and installed by the original OnionDuke infection, although others may have their own command and control server.
Investigating the Sources of OnionDuke Attacks
One component involving OnionDuke has caught the attention of PC security analysts. Among its data, malware researchers have noted that OnionDuke may use Twitter to receive commands from a remote location. One additional feature that also has caught the attention of PC security researchers is that the domains associated with OnionDuke were registered in 2011 by a 'John Kasai', who has also registered numerous domains that have been associated with MiniDuke. This indicates that, although separate, the people responsible for OnionDuke may also be responsible for the devastating MiniDuke attacks and the connection between both threat families goes quite deeper.
Research on dates and code involved with OnionDuke has revealed that OnionDuke has been active since at least October of 2013 and, since February of 2014 infecting executable files contained in .torrent files used to distribute pirated software. Some of the configuration data suggests that OnionDuke has been around quite a bit longer, with several separate versions existing from earlier dates.
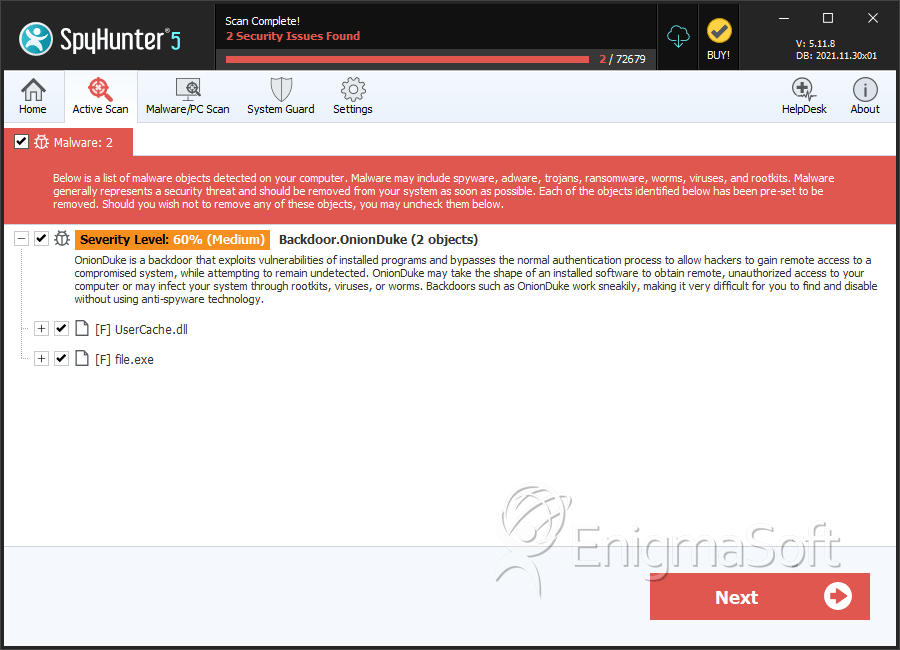
SpyHunter Detects & Remove OnionDuke
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | UserCache.dll | c8eb6040fd02d77660d19057a38ff769 | 0 |
| 2. | file.exe | 5473e29ca75d475f545fa7d9f85e564f | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.