New Zealand Police Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 2,895 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 5,731 |
| First Seen: | February 25, 2013 |
| Last Seen: | September 20, 2023 |
| OS(es) Affected: | Windows |
Initial Police Ransomware attacks we concentrated in the Russian Federation and Eastern European states. These primitive Winlockers were easily bypassed using Safe Mode and demanded payment through SMS messages. Since then, These scams have developed into dangerous malware threats that are able to take pictures using the infected web cam, alter their messages depending to the infected computer's IP address and disable features such as Safe Mode and System Restore. Modern Police Ransomware infections demand payment through Ukash, MoneyPak or a number of other money transfer methods. They are also not concentrated in Europe anymore and, during 2012, spread far and wide. The New Zealand Police Ransomware infection is a good example of this, attacking computers in New Zealand. Variants of these threats have also popped up in South America, Australia and South Africa.
The New Zealand Police Ransomware infection carries out a classic version of the ransomware scam. Essentially, the New Zealand Police Ransomware Trojan takes the victim's computer hostage and then demands payment of one hundred New Zealand dollar fine. Like its many variants, the New Zealand Police Ransomware Trojan displays a message that accuses the victim of viewing pornographic material, downloading copyrighted content and sending out spam email messages. Since, to some degree, many computer users may engage in these activities without knowing it, these kinds of messages are highly effective at scaring inexperienced computer users who may feel guilty about engaging in inappropriate online behavior. After listing the severe penalties that these kinds of activities have under the law, including extensive jail time, the New Zealand Police Ransomware message claims it is possible to avoid these penalties by paying a one time fine.
Table of Contents
Do Not Fall for the New Zealand Police Ransomware Scam!
Since the New Zealand Police Ransomware message has nothing to do with the New Zealand police, ESG security analysts strongly advise computer users to ignore its threatening message. Paying this Trojan's fine will do nothing to unlock your computer. It is possible to remove a New Zealand Police Ransomware infection by gaining access to your security software using alternate boot methods (such as an external start-up disk) and then scanning your computer in order to undo the malicious changes made by the New Zealand Police Trojan to your computer's settings.
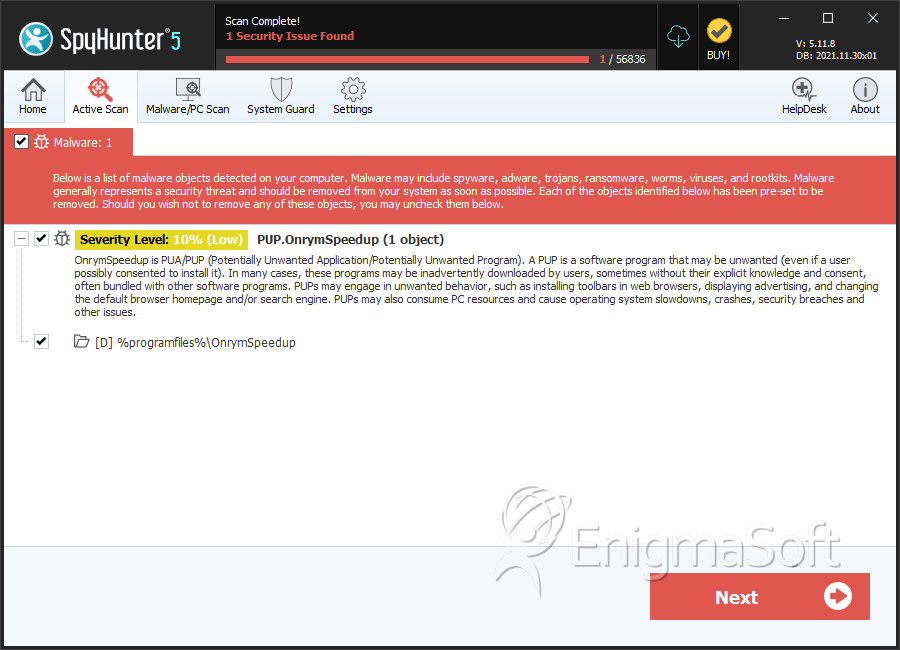
SpyHunter Detects & Remove New Zealand Police Ransomware
Registry Details
Directories
New Zealand Police Ransomware may create the following directory or directories:
| %programfiles%\OnrymSpeedup |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.