MedusaLocker Remains One of the Primary Ransomware Dangers Right Now
MedusaLocker Remains One of the Primary Ransomware Dangers Right Now Image
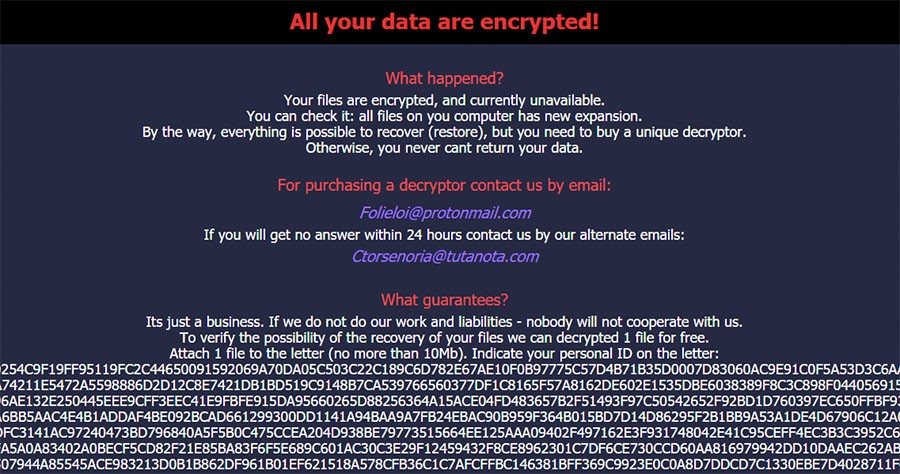
Researchers working at Cisco Talos put their sights on MedusaLocker, ransomware of a particularly prolific nature that sees much activity during the pandemic. The ransomware was first spotted in the wild in 2019, but it has been staying relevant by splitting off into more variants, with advanced persistence upgrades and the ability to infiltrate networks.
MedusaLocker is combining the usual ransomware tactics with the ability to map out network drives, forcing remapping and content encryption. Once MedusaLocker finds itself embedded into a system on a network, it can cause massive damage on all drives within that network.
Table of Contents
What makes MedusaLocker so Dangerous?
MedusaLocker begins its operations by copying itself into the %APPDATA%\Roaming\ directory, then setting up scheduled tasks in Windows on 15-minute intervals. That is done for the reason of finding and encrypting media files connected to the infected system on the network. Users are advised to disconnect infected machines from the network immediately to avoid the spread of the infection. The ransomware uses the '.encrypted' extension for the affected files, with a ransom note generated in all directories. The encryption is the AES 256 variety, with an RSA-2048 key within the executable.
What makes MedusaLocker even more dangerous is the ability to delete 'vssadmin' from Windows, a utility used to restore shadow copies and backups. Assuming users were able to utilize any backups to restore data, they wouldn't have to pay the attackers any ransom. What is more, MedusaLocker tries to reconnect the infected system back to the network, using Windows Registry entries to make it happen. Using a physical disconnection method is necessary to stop that from happening, for example unplugging the cable.
What Measures Can Be Taken by the Average User?
Security researchers advise applying email and spam filters to better protect against MedusaLocker. Other steps that should be taken include updating all components regularly, enabling multi-factor authentication, and using updated security software.
Keeping backups offline is an excellent way to keep your data safe, but that should only be done with systems that are decidedly clean of malware of any kind. Avoiding the use of legacy security products is necessary, as MedusaLocker is blocking the usual reverse engineering and analysis tricks.
The MedusaLocker ransomware was spotted in September 2019 by MalwareHunterTeam for the first time. In as little as 30 days since it was discovered, an average of 10 submissions was made daily, according to the ID Ransomware website. That may not appear like much, but for new ransomware, it was more than enough to make itself known. After that first month, government warnings and news articles started warning users of the new danger.
Since that initial discovery, it has managed to stay relatively unpopular, with the last time it was actively significant being February 2020. Compared to the more popular Ryuk, DoppelPaymer, Maze, and Sodinokibi, MedusaLocker has been less prolific in targeting big corporations.
