Lynx Ransomware
Protecting devices from malware threats is crucial to maintaining the integrity and security of personal and organizational data. Ransomware, a particularly dangerous type of malware, is typically designed specifically to encrypt files and demand a ransom for their decryption, causing significant disruption and potential data loss.
Table of Contents
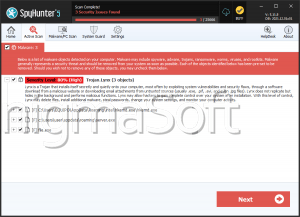
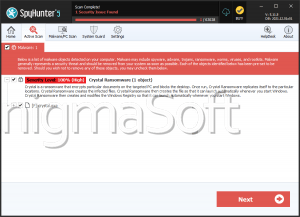
Understanding the Lynx Ransomware
Lynx is a type of threatening software classified as ransomware. When executed on a compromised device, Lynx encrypts files and appends the '.LYNX' extension to their original names. For instance, a file named '1.png' becomes '1.png.LYNX', and '2.pdf' changes to '2.pdf.LYNX'.
Post-Infection Actions
After encryption, the Lynx Ransomware changes the desktop wallpaper and drops a text file named 'README.txt.' Both the new wallpaper and the text file contain identical ransom notes. The ransom note informs victims that their files have been locked and that sensitive data has been stolen. It also urges the victim to contact the attackers, often providing a link to the cybercriminals' Tor network website for leaking data.
Ransom Note Details
The ransom note is brief, emphasizing the encryption of the victim's files and the theft of sensitive data. While the note does not directly threaten to leak the data, it suggests that the stolen data may be published if the ransom is not paid. This tactic is known as double extortion, where victims are pressured to pay not only to decrypt their files but also to prevent the leaking of sensitive information.
Implications of Paying the Ransom
Despite the pressure, paying the ransom does not guarantee file recovery. Cybercriminals often fail to provide the promised decryption keys or programs even after receiving the ransom. Moreover, sending money to these criminals supports their illegal activities, further perpetuating the cycle of cybercrime.
Technical Aspects of the Lynx Ransomware
Ransomware like Lynx can use different cryptographic algorithms to encrypt files, either symmetric or asymmetric. The strength and type of encryption used can significantly impact the ability to decrypt files without the attackers' assistance.
Ransom Amounts
The demanded ransom can vary significantly, ranging from a few hundred to several million USD, depending on the intended victim. Home users might face lower ransom demands, while large entities could be targeted with much higher amounts.
Preventive Measures Against Ransomware
To protect against ransomware infections like Lynx, users should implement the following security measures:
- Regular Backups: Maintain regular backups of all important data. Ensure that backups are stored offline or in a secure, isolated environment to prevent ransomware from accessing them.
- Up-to-date Software: Keep all types of software, including programs and operating systems upgraded with the latest available security patches.
- Anti-malware Solutions: Use reputable anti-malware software to uncover and stop ransomware before it can cause harm.
- Email and Web Filtering: Implement email filtering to block unsafe attachments and links. Use Web filtering to prevent known malicious websites from attempting access.
- User Training and Awareness: Educate users about the hazards of ransomware and how to recognize phishing emails and other common attack vectors.
- Network Segmentation: Segment the network to contain the spread of ransomware if an infection occurs.
- Least Privilege Principle: Apply the rule of least privilege to restrict users' access to only the data and systems necessary for their roles.
Protecting devices from ransomware threats like Lynx is essential to maintaining data security and preventing significant disruptions. By implementing robust security measures, staying informed about the latest threats, and adopting a culture of cybersecurity awareness, PC users can significantly reduce the risk of falling victim to ransomware attacks.
The ransom note dropped by the Lynx Ransomware is:
'Your data is stolen and encrypted.
Your unique identificator is 66a204aee7861ae72f21b4e0
Use this TOR site to contact with us:Use this email to contact with us:
martina.lestariid1898@proton.meOur blog
~ TOR Network: -
~ Mirror #1: -'