LightNeuron
A threatening backdoor dubbed LightNeuron has been reported by security experts as the introductory malware to bring about persistence in the email servers of Microsoft Exchange. By using LightNeuron, the criminals can run commands through corrupted email attachments containing a concealed code. Security experts claim that LightNeuron is not a new threat since it has been attacking Microsoft Exchange servers since 2014 and looks like that the developers of LightNeuron are an espionage-linked criminal group named Turla, which also is called Snake. There have been reports of LightNeuron attacks in the Middle East, Brazil and Eastern Europe. The persistence used by LightNeuron is called Transport Agent and can perform with a high level of reliability on the infected machine. With the attributes of Transport Agent, LightNeuron can prevent its victims from sending emails, read and change any email carried via the email server, compose and send emails and perform other, harmful actions.
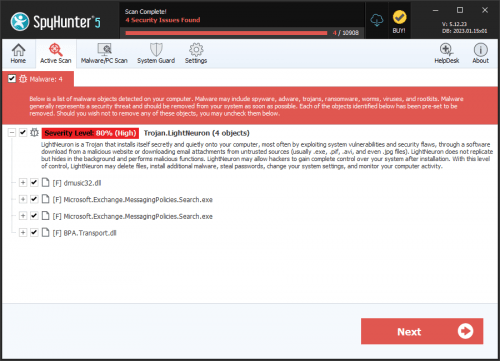
The task of removing a threat like LightNeuron may present various issues since if anything goes wrong, the email server will be rendered useless, which may end up causing even monetary loss. The security experts recommendation is to disable Transport Agent as the first action. Then, the victims should proceed with the removal of LightNeuron by using a devoted anti-malware program.