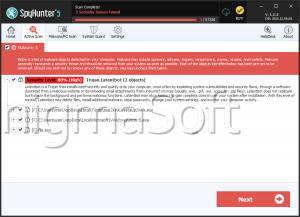
LATENTBOT
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 25 |
| First Seen: | December 16, 2015 |
| Last Seen: | June 14, 2023 |
| OS(es) Affected: | Windows |
LATENTBOT is a new backdoor Trojan that is used to carry out stealth attacks on specific, high- valued targets. LATENTBOT has become known as a particularly stealthy type of backdoor Trojan that has managed to stay hidden for an extraordinarily long time. LATENTBOT is particularly effective at covering its tracks and hiding from security applications on affected computers. LATENTBOT is practically unsurpassed in this regard. LATENTBOT has been detected on computers all around the world, including the United States, South Korea, the United Kingdom, Canada, Peru, Singapore, Poland, the United Arab Emirates and Brazil.
As of now, PC security researchers have not identified a common link between the different computers affected by LATENTBOT. This threat seems to infect computers from various differing industry sectors. However, it is apparent that LATENTBOT is designed to target computers in industry and business rather than focusing on individual computer users. This makes LATENTBOT attacks particularly more harmful than other threats since the potential for data loss, and espionage is much higher than the average infection.
Table of Contents
How LATENTBOT may Infect a Computer
In most cases, LATENTBOT is spread using spam email campaigns. LATENTBOT is included as a corrupted email attachment that may deliver a Trojan downloader to the victim's computer. This Trojan downloader may deliver the LuminosityLink, a threatening RAT (Remote Access Trojan) to the victim's computer. RATs allow third parties to take control over a computer from a remote location. Using this RAT, con artists can install LATENTBOT on the victim's computer. LATENTBOT, unlike many other backdoor Trojans, is designed to run on newer versions of Windows. This means that LATENTBOT is not effective on Windows XP, Windows Vista or Windows Server 2008. Rather, LATENTBOT is designed to infect computers running Windows 7 and newer versions of this operating system.
LATENTBOT is Designed to Remain Undetected on the Victim’s Computer
LATENTBOT uses a complex installation process that is designed to allow LATENTBOT to remain silent. The LATENTBOT installation process involves six stages that are meant to prevent computer security researchers from studying this threat. LATENTBOT is highly obfuscated, and its code is designed specifically to prevent its study by security researchers. LATENTBOT will also delete its data from the affected computer when it's no longer needed and hides its files and associated applications.
How LATENTBOT Carries out Its Attack
LATENTBOT is built using a modular design that allows LATENTBOT to receive specific upgrades and improvements that may add new features. LATENTBOT has the capacity to deliver other threats (LATENTBOT has been linked to the Pony threat), delete the victim's MBR (Master Boot Record) to ruin the affected computer, or collect banking information and online passwords. The first signs of LATENTBOT were first detected in 2013. However, LATENTBOT has been particularly effective at avoiding leaving traces on targeted computers. Fortunately, the fact that LATENTBOT has been around for such a long time has meant that security applications have become capable of detecting LATENTBOT. Security programs will rarely detect LATENTBOT under this name, but will observe its traces in the computer's memory, labeling it LATENTBOT as a 'generic threat.'
What to do When Infected with LATENTBOT
To deal with LATENTBOT, malware researchers recommend the use of a reliable, fully updated anti-malware application. All security software should be kept fully updated. New ways of detecting LATENTBOT, from studying its obfuscated code and updates, are released occasionally, and malware researchers are releasing new updates to combat any new modules released for these types of infections constantly.