Keylogger.Revealer
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 1,845 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 14,050 |
| First Seen: | July 24, 2009 |
| Last Seen: | September 20, 2023 |
| OS(es) Affected: | Windows |
Keylogger.Revealer is a detection name used by cybersecurity vendors in reference to the Revealer program by Logixoft that has an official page on Logixoft.com. The Keylogger.Revealer software is proposed to companies and concerned parents as a monitoring tool, which can help securing important files and help you keep tabs on your children's online activity. Many cybersecurity experts have spoken well of Revealer by Logixoft but you should take into consideration that Black Hat hackers may abuse the application. The Keylogger.Revealer program is available as a free download that supports the following functionality:
- Prevents someone else from opening the program.
- Records text, passwords, and conversations.
The developers of Keylogger.Revealer claim that their program recognizes IM clients, Internet browsers, and other types of apps where the user credentials and simple text is received as input. The complete Revealer suite can be paid for with a one-time payment of 39,99 EUR, which grants the keylogger operator the right to install the app on one machine. Parents and company management may be interested in buying the 'Family' and 'Business' packages, which allow you to install the Keylogger.Revealer on three to five computers. Additionally, Revealer PRO users receive access to the following advanced capabilities of the software:
- Hides in Task Manager, at startup and on the drive.
- Takes screenshots of the desktop or active window.
- Log files via email, Dropbox and FTP or the Local Network.
Experts recommend you read the Privacy Policy published on Logixoft.com/en-eu/privacy-policy before you decide to use the Keylogger.Revealer software. Monitoring tools like Revealer from Logixoft are deemed as legitimate programs, but they are easy to abuse. If you find Keylogger.Revealer on your home PC and you have not installed it yourself, chances are that a third-party might have recorded your activity on the device. Hence, it is a good idea to change your passwords for all your online accounts. PC users who suspect their system is compromised by a corrupted copy of Keylogger.Revealer should use a trusted anti-malware solution to clean their systems.
Table of Contents
Aliases
11 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Sunbelt | Revealer Free Edition |
| Panda | Trj/Keylog.LH |
| Ikarus | not-a-virus:Monitor.Win32.RevealerKeylogger.b |
| Fortinet | Keylog/RevealerKeylogger |
| F-Secure | Monitor.Win32.RevealerKeylogger.b |
| eWido | Not-A-Virus.Monitor.Win32.RevealerKeylogger.b |
| ClamAV | Trojan.Keylogger-209 |
| BitDefender | Application.Keylogger.Revealer.1.2 |
| AVG | Logger.CYJ |
| Avast | Win32:Adware-gen |
| AntiVir | SPR/RevealerKeylogger.B.1 |
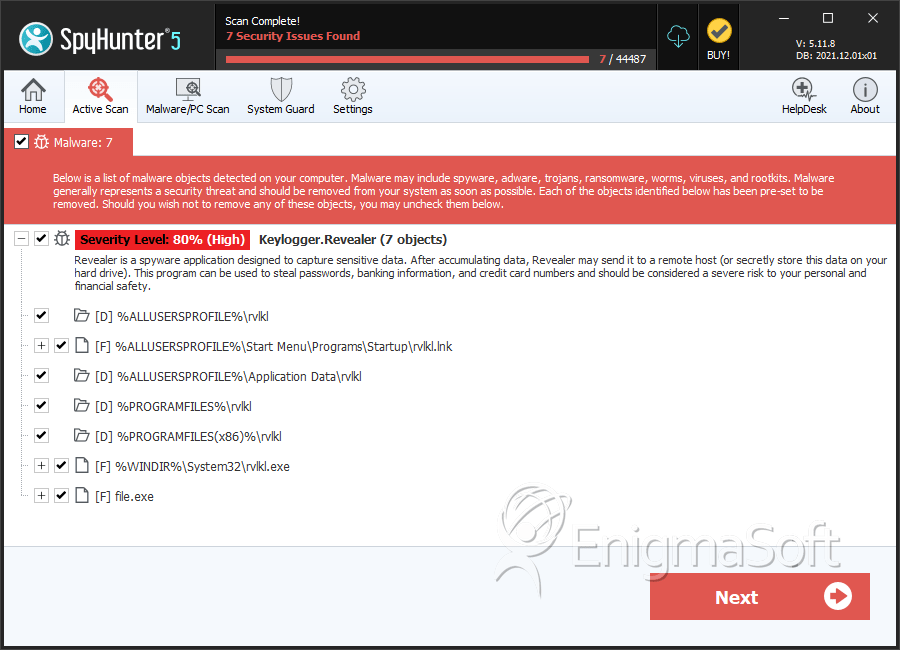
SpyHunter Detects & Remove Keylogger.Revealer
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | rvlkl.lnk | 5656e45ecab328ddde79e815b0a6d2d4 | 242 |
| 2. | rvlkl.lnk | d95c7bd2b19201d654a2e0d46dd91044 | 226 |
| 3. | rvlkl.lnk | 4d5ab107ffc743a01b631af3054010bd | 167 |
| 4. | rvlkl.exe | adbeeb56fdf4afab537af84dcf22ef0b | 139 |
| 5. | rvlkl.lnk | 706827141a26d7006c9cefbdcb3c3259 | 102 |
| 6. | rvlkl.exe | 47ea6a6ecff01d6dd3d37896b85b47c4 | 86 |
| 7. | rvlkl.lnk | 21edee5f0806469524f98667af280e56 | 83 |
| 8. | rvlkl.lnk | 5cad2c402c420039579949acd2ef66f6 | 83 |
| 9. | rvlkl.lnk | 1227cdc53f991ca8f712ed2a0c13c58b | 76 |
| 10. | rvlkl.lnk | db75b3607bfa0e8eff8a2e637d72a283 | 67 |
| 11. | rvlkl.exe | b088b294ea68045da5ef3c28e7667535 | 60 |
| 12. | rvlkl.exe | 638ec77b4fef6e71f53de03e20889461 | 52 |
| 13. | rvlkl.exe | 3ed9e62ff0f8ee8854bcb7943cd961de | 46 |
| 14. | rvlkl.lnk | a8241f5447e90cfbd2f59d9e3ce84d8f | 45 |
| 15. | rvlkl.lnk | b1618a3f8b15974af5a4d1a48d98f591 | 42 |
| 16. | rvlkl.exe | 1179da3d9aa1d716862e23723104af0d | 32 |
| 17. | rvlkl.exe | de3ebeb04dc0a95c274270ac47ec0899 | 23 |
| 18. | rvlkl.exe | 5e276375fc67913d53814f47431cda3a | 20 |
| 19. | rvlkl.exe | 5e09352059a7fc6357e9ebdf9561f849 | 14 |
| 20. | rvlkl.exe | f11f567f2578f06b1b32040283fd9401 | 10 |
| 21. | rvlkl.exe | dae32e26f42f996354f4461e61274074 | 8 |
| 22. | rvlkl.exe | c90846e860f7766d84814d7707b06149 | 3 |
| 23. | rvlkl.exe | 6139dedba18185cb55b5bf68d7ead1e7 | 3 |
| 24. | rvlkl.exe | 73a0bff9cc4db8a8efa832650c35d196 | 2 |
| 25. | file.exe | 6e6c73f87952f9fa6ae12ebfd5c74071 | 1 |
Registry Details
Directories
Keylogger.Revealer may create the following directory or directories:
| %ALLUSERSPROFILE%\Application Data\rvlkl |
| %ALLUSERSPROFILE%\rvlkl |
| %PROGRAMFILES%\rvlkl |
| %PROGRAMFILES(x86)%\rvlkl |

