Jpadsnetwork.com
The internet is filled with malicious and deceptive websites designed to exploit unsuspecting users. Cybercriminals continuously adapt their tactics, relying on fake prompts, misleading ads, and fraudulent notifications to trick visitors into lowering their guard. One such rogue platform tracked as Jpadsnetwork.com demonstrates why vigilance is essential when browsing.
Table of Contents
Deceptive tactics of Jpadsnetwork.com
Jpadsnetwork.com is engineered to exploit users' trust in common web elements. Researchers have found that the site relies heavily on a fake CAPTCHA check to convince visitors to click the 'Allow' button. By disguising its trick as a standard verification prompt, it manipulates users into enabling browser push notifications. Once these permissions are granted, the site gains the ability to flood the victim's device with intrusive ads.
Notably, Jpadsnetwork.com and similar websites are often reached indirectly through redirect chains initiated by shady advertising networks. Depending on the visitor's IP address and geolocation, the site's content and redirections may vary, making detection and blocking more difficult. In some cases, pressing 'Allow' on the page has led to forced redirection toward other malicious domains, such as Cramlexad.com.
The hidden danger behind spam notifications
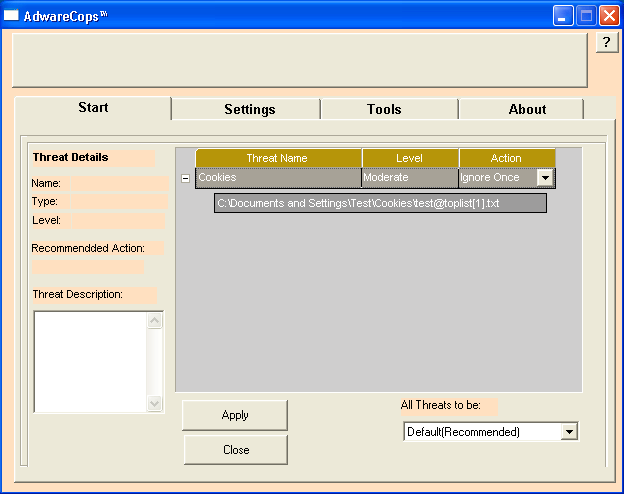
Once users permit notifications, Jpadsnetwork.com exploits this channel to deliver aggressive advertising campaigns. These notifications can promote:
- Malicious websites pushing phishing scams or fake technical support alerts.
- Untrustworthy and potentially unwanted programs (adware, browser hijackers, and fake optimization tools).
- Direct links to malware, including trojans, spyware, and ransomware.
Even when notifications advertise legitimate-looking products or services, it is often a scammer abusing affiliate programs for profit. This means clicking such ads risks exposure to both fraudulent content and malicious downloads.
Warning signs of fake CAPTCHA checks
One of the most common methods rogue sites use to gain user interaction is the phony CAPTCHA test. These typically feature:
- Messages like 'Click Allow to verify you are not a robot' or 'Press Allow to continue.'
- Oversimplified CAPTCHA-style graphics with no actual validation mechanism.
- A lack of alternative verification methods, pressing 'Allow' is presented as the only option.
- Suspicious redirects after interaction, leading to unrelated or unsafe pages.
Genuine CAPTCHA systems never require enabling browser notifications. Their sole purpose is to verify human activity through visual or logic-based tests, not push permissions. Recognizing this difference is key to avoiding manipulation.
The risks of interaction
By falling for these tricks, users open the door to significant risks, including malware infections, privacy breaches, financial theft, and even identity compromise. Every notification click further deepens exposure, while system performance and security degrade as malicious content piles up.
Final thoughts: Staying protected
Jpadsnetwork.com illustrates how social engineering and technical abuse combine to deliver harmful results. Users should never trust CAPTCHA prompts that request notification permissions and should immediately close such pages. Configuring browser settings to block suspicious notifications, keeping security tools updated, and browsing only through trusted sources are all critical defenses. Awareness and caution remain the strongest shields against threats posed by rogue websites.