Infostealer.Napolar
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 2,010 |
| First Seen: | September 25, 2013 |
| Last Seen: | July 11, 2021 |
| OS(es) Affected: | Windows |
Napolar is a Trojan used to steal information from infected computers. Napolar made its first appearances in early 2013 and quickly gained popularity among criminals. Currently, PC security researchers have noticed hundreds of cases of attempted Napolar attacks every day. Napolar goes by various aliases. Napolar is also widely known as Solarbot. Napolar first started to be noticed in May after advertisements for this Trojan started to appear in underground forums and websites. Napolar infections increased significantly in the weeks after these advertisements started to appear.
Table of Contents
A Cheap Tool that Can Generate High Profit
The majority of Napolar attacks started to appear in mid-August. Currently, malware researchers estimate that thousands of Napolar infections are active, especially in South America. One aspect of Napolar that has caught the attention of malware researchers is that this threat is promoted with a professionally designed website that is accessible to the public and that contains information on developing Napolar plug-ins. The website even contains a user manual for this Trojan. However, the most alarming aspect of Napolar is its low price. Anyone can buy the Napolar Trojan's binary file (necessary to infect computers) for the impressively low cost of two hundred dollars. Similar Trojans can cost thousands of dollars, making this low-cost threat particularly ominous.
Napolar not So Impossible Mission is to Seize Personal Information
Napolar may be used to carry out Distributed Denial of Service Attacks (DdoS), establish an unauthorized proxy, steal sensitive data such as passwords and login information and spy on the computer users' online activity. The Napolar uses a modular design that allows its functionality to be extended through the use of plug-ins. Plug-ins for this threat may be developed to add new features. For example, a plug-in may be added to Napolar that allows criminals to steal Bitcoin wallets or target a specific bank's login credentials. Although the Napolar Trojan has worldwide reach, most Napolar attacks have occurred in Latin American countries. It is important to note that there are numerous other Trojans today that offer similar features to the Napolar Trojan and that are widely used. For example, the many variants of the ZeuS Trojan come to mind. However, Napolar's low price makes Napolar stand out from these alternatives.
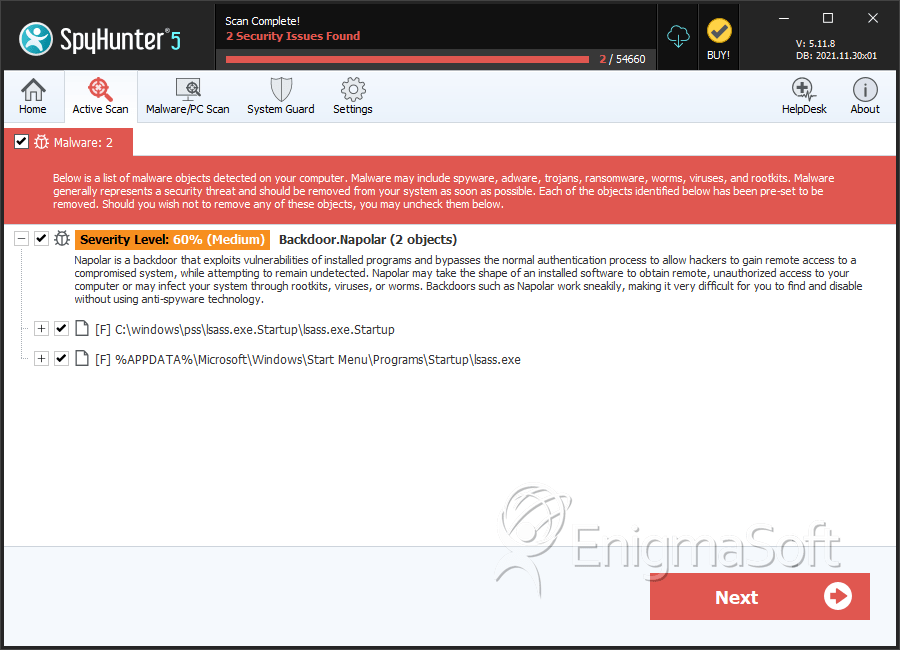
SpyHunter Detects & Remove Infostealer.Napolar
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | lsass.exe | 3ecf858ffd7838e119df1f0fd820e434 | 228 |
| 2. | lsass.exe.Startup | 67b9431ad975013a7b947dce3d03183b | 227 |
| 3. | lsass.exe | 0526c700b23f41fdb3ccff153b043577 | 215 |
| 4. | lsass.exe | a7f98058b69527f7ac081f8966082ce7 | 134 |
| 5. | lsass.exe | e918ae5279ccbb47d9d2fa0f92fbf2ee | 105 |
| 6. | lsass.exe | 618cb4a2a1b3007f24b8b5bbcc578f35 | 100 |
| 7. | lsass.exe | b1b76f46ba82d1ff343010740eadb66c | 68 |
| 8. | lsass.exe | 38b3234fca4c48a2c35c55699a33ea93 | 67 |
| 9. | lsass.exe | 6c8c66923f24cb197f1e8fb97e7e49c2 | 67 |
| 10. | lsass.exe | 2d3c64b8b2604c9d4327b9926b84080a | 53 |
| 11. | lsass.exe | 9871a4184603d7815317c8c03c56f368 | 51 |
| 12. | lsass.exe | 13f24d9b6eeb1a6a7329aaf1fbb39781 | 47 |
| 13. | lsass.exe | 399efabada0ef92b47400e94763729b2 | 45 |
| 14. | lsass.exe | c13b4da055e54465dc73ff4e0fb95032 | 43 |
| 15. | lsass.exe | ac047ca35b0fb6a5c16efecce59eda96 | 41 |
| 16. | lsass.exe | 5336f8fbdcd83fa9b7034dcef5659d12 | 39 |
| 17. | lsass.exe | 62bd1d3ff352de28b88245a98d4660ba | 38 |
| 18. | lsass.exe | e9807b55084a3fbfef875b6c73ee52fa | 32 |
| 19. | lsass.exe | 274da20e073b912e7bd97ddbd29bfbdd | 31 |
| 20. |
C:\Documents and Settings\ |
||
| 21. |
C:\Documents and Settings\ |
||
| 22. |
C:\Documents and Settings\ |
Registry Details
URLs
Infostealer.Napolar may call the following URLs:
| canc3r1nf0rmat10n.pw |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.