Infostealer.Gampass
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 190 |
| First Seen: | July 24, 2009 |
| Last Seen: | February 18, 2023 |
| OS(es) Affected: | Windows |
The Infostealer.Gampass Trojan was first discovered in the Fall of 2006 and was last updated in March of 2007. However, Infostealer.Gampass and several variants of this threat remain active today. Infostealer.Gampass, also known as LIneage YI and Bloodhound.KillAV, is a threat that is used to collect login information for various online video games. Infostealer.Gampass is used to infect computers running the Windows operating system. Infostealer.Gampass does this by trying to log information such as video game registration numbers and keys and login information for online accounts. Infostealer.Gampass' main targets are MMORPGs (Massively Multiplayer Online Role Playing Games) such as Warcraft or World. In order to carry out its attacks, Infostealer.Gampass needs to run on an infected PC with the targeted video game and the affected computer needs to have a network connection.
Table of Contents
How Infostealer.Gampass is Disgtributres
Infostealer.Gampass follows typical threat delivery methods in its distribution. However, Infostealer.Gampassi s distributed in two specific ways designed to target online games:
- Infostealer.Gampass may be distributed through file sharing networks. The Infostealer.Gampasse xecutable file or a dropper Trojan may be disguised as an enhancement, module or another component for the targeted game.
- Infostealer.Gampass may also be distributed through online forum posts posted on forums that are related to the targeted game.
The Infostealer.Gampass attack is straightforward: Infostealer.Gampass will try to gain access to the victim's information and then send it to a third party. Infostealer.Gampass has become a standard detection for threats that specifically try to target video game credentials. Initial Infostealer.Gampass infections were used to gather the registration keys for popular games. Having access to the registration key allowed the attacker to play the game without having to purchase a copy. However, things have evolved since the beginning of Infostealer.Gampass. Online video games have become ever more popular, with underground economies forming around particularly popular games. This has allowed third parties to make significant profits by selling game accounts, in-game items, currency and through other game-related illicit activities. This resulted in the evolution of Infostealer.Gampass, with a greater focus on collecting account data rather than registration keys for new games. Attackers gaining login information for a particular account with valuable in-game items may log into the targeted account, strip it of all of its owners achievements and sell these to a third party.
Unlike other Trojans, the most popular way in which Infostealer.Gampass is distributed through gaming-related avenues, especially forum posts and file sharing networks. File sharing websites are already rife with threats and suspicious files. In many cases, cracks, mods and other components distributed on file sharing networks are Trojans such as Infostealer.Gampass designed to take over the victim's account and collect their login information. These types of files may also be downloaded through game forums. Spammers may spam the comments on these forums, claiming that they can solve various problems or help computer users to have greater success in the targeted game through a download offered in the spam comments. This has meant that Infostealer.Gampass distribution tactics are rather advanced, designed to target the users of one particular game specifically.
Protecting Yourself from Infostealer.Gampass
Although Infostealer.Gampass variants target specific games, reputable security software may detect the different Infostealer.Gampass variants since they use typical methods such as logging computer user's keystrokes or taking screenshots on the affected computer. The main goal of Infostealer.Gampass attacks is to collect gaming accounts and to obtain in-game items and currency. In many cases, computer users will not realize they have been attacked until they cannot log into their gaming account or realize that their account has been stripped of achievements, items and currency. Fortunately, computer users can protect themselves by using a strong security application to protect their computer at all times.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Ikarus | Packer.PESpin |
| Sophos | Mal/Packer |
| AntiVir | TR/Agent.3710976 |
| BitDefender | Gen:Packer.PESpin.A.I7W@aynDsUrO |
| ClamAV | Trojan.Backdoor-11 |
| eSafe | Win32.TRAgent |
| NOD32 | probably a variant of Win32/Spy.Agent.IJPQFES |
| K7AntiVirus | Riskware |
| McAfee | Generic.dx!f |
| Panda | Trj/Lineage.BZE |
| Fortinet | W32/Agent.LTXBUDK!tr |
| Ikarus | Win32.SuspectCrc |
| Sophos | Mal/KeyGen-M |
| DrWeb | Trojan.Packed.593 |
| Comodo | UnclassifiedMalware |
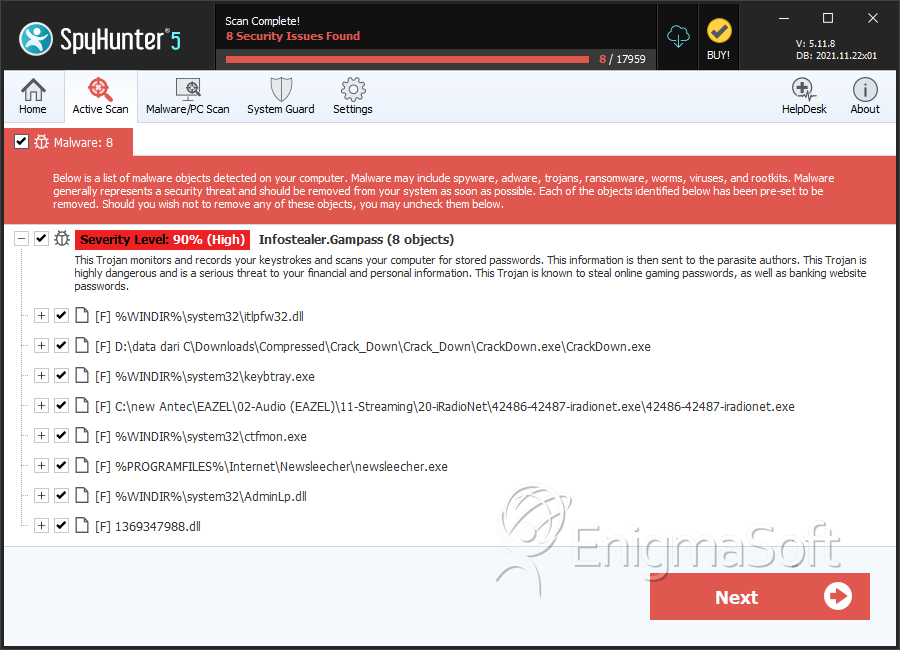
SpyHunter Detects & Remove Infostealer.Gampass
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | itlpfw32.dll | 4ed60abfeed35a673b90d651818250f0 | 85 |
| 2. | CrackDown.exe | cb70c4fa80243195ba59e25db068e1c8 | 25 |
| 3. | keybtray.exe | b030222345d91c7aa73867bcb5b7a380 | 14 |
| 4. | 42486-42487-iradionet.exe | 37e6e1a278659302f311dd9015cce387 | 6 |
| 5. | ctfmon.exe | 7fe831e595f75caade9bc91fbabf10a1 | 4 |
| 6. | newsleecher.exe | fc6ca6278e89916b7aa8edefbfe0864c | 3 |
| 7. | AdminLp.dll | 249e70aab278802186302b31f28d0e05 | 1 |
| 8. | 1369347988.dll | f9053595b96cb98255730e5854d9e4fe | 0 |
| 9. | rru.exe | 3b2786554980c167f614ce4b84dc3bfc | 0 |
| 10. | cj.v4.dll | be229d6cb0613be8a337b7e48273f9c0 | 0 |
| 11. | video.dll | e2dfd03fb9b2a99689dde74d6beffc25 | 0 |

