HYFBTCLOCKER Ransomware
Protecting personal data from modern malware is essential, as today's threats are designed to spread quickly, cause extensive damage, and leave victims with limited recovery options. HYFBTCLOCKER Ransomware is a prime example of how disruptive these attacks can be, targeting files across a system and holding them hostage for profit.
Table of Contents
A Dangerous File-Locking Operation
HYFBTCLOCKER was identified during an analysis of newly emerging malicious threats. Once it infiltrates a device, it launches a systematic encryption routine that targets a wide range of file types. Each locked file receives the '.hyfencb' extension, turning ordinary documents like '1.png' into '1.png.hyfencb,' and so on. After completing this process, the ransomware plants a ransom note named 'WHAT_HAPPEN_OF_MYFILE.html', which outlines the attackers' demands.
The note claims that all data has been encrypted using AES-256, a robust cryptographic standard. Victims are told that the only way to recover their information is to follow the attackers' instructions. The message also threatens that tampering with encrypted files, moving, renaming, or deleting them, will make recovery impossible.
The Reality Behind the Ransom
In most ransomware cases, files cannot be decrypted without the cybercriminals' private keys. Only in rare cases involving poorly made ransomware can victims restore their data without paying. Even then, success is uncommon. Worse yet, many victims who meet the demands never receive a working decryption tool.
For these reasons, paying the ransom is strongly discouraged. It fuels criminal activity and offers no guarantee of data restoration.
Eliminating HYFBTCLOCKER from an infected system is still important, as it prevents additional files from being encrypted. However, removal does not undo the damage. The only dependable recovery path is restoring data from a safe, unaffected backup.
Why Backups Matter
Regular backups remain the strongest defense against ransomware-induced data loss. Storing copies in more than one location ensures that a single failure point, whether a cyberattack or hardware issue, doesn't result in permanent loss. Remote servers, external drives kept offline, and other isolated storage solutions all play a vital role in a healthy backup strategy.
How HYFBTCLOCKER Spreads
Like many modern threats, HYFBTCLOCKER relies heavily on deception. Attackers frequently disguise malicious files as ordinary documents, software installers, compressed archives, or scripts. Simply opening one can be enough to activate the malware.
Its distribution methods often involve:
- Phishing and social engineering that push victims to open attachments or click harmful links.
- Compromised or unreliable download sources, pirated content, malicious ads, fake updates, and trojans that load ransomware in the background.
- Some malicious programs can even propagate independently via local networks or removable media, enabling rapid spread within organizations.
Strengthening Your Defense Against Malware
A multi-layered security approach significantly reduces the risk of ransomware infections. Adopting safe digital habits and using reliable protective tools creates strong resistance against even advanced threats.
Key practices include:
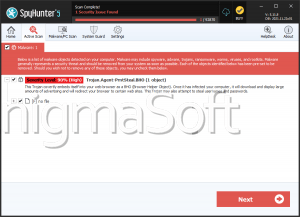
- Use reputable security software and ensure real-time protection is enabled.
- Update the operating system and all applications regularly, as attackers frequently exploit outdated software.
- Avoid opening unexpected attachments or clicking suspicious links, even if they appear legitimate.
- Download software only from official sources, never from freeware hubs, torrent sites, or unofficial distributors.
- Disable automatic execution on external drives to prevent self-spreading malware.
- Maintain routine backups, keeping at least one copy offline or offsite.
- Be cautious with macros and scripting features in documents, as these are common infection vectors.
Implementing these measures creates a meaningful barrier against ransomware and reduces the likelihood of severe data loss.
Final Thoughts
HYFBTCLOCKER illustrates how quickly modern ransomware can compromise critical information. While the damage it causes can be substantial, informed behavior and solid security practices dramatically decrease the risk. Staying alert, maintaining secure backups, and using trusted cybersecurity tools are essential steps in ensuring long-term digital safety.