How to Get Rid of Malware on Your Android Phone
 Google's mobile operating system Android is notoriously known for being prone to malware infections of all kinds. Although the company has recently made significant steps into improving the security of Android devices, chances of downloading an infected app are still high, even if you have installed some anti-virus programs on your device. Malware threats spread through various channels, yet they are typically hidden within third-party applications that promise free tools, games, adult or gambling content. So, if you have recently installed any such apps, you should check your Android device for symptoms of an infection. Signs that you are already infected include your device running suddenly really slow, displaying weird data, or making certain data inaccessible to you. A ransomware threat, or some data-stealing malware, could have sneaked into your Android phone, so you should immediately take steps to remove the dangerous scripts.
Google's mobile operating system Android is notoriously known for being prone to malware infections of all kinds. Although the company has recently made significant steps into improving the security of Android devices, chances of downloading an infected app are still high, even if you have installed some anti-virus programs on your device. Malware threats spread through various channels, yet they are typically hidden within third-party applications that promise free tools, games, adult or gambling content. So, if you have recently installed any such apps, you should check your Android device for symptoms of an infection. Signs that you are already infected include your device running suddenly really slow, displaying weird data, or making certain data inaccessible to you. A ransomware threat, or some data-stealing malware, could have sneaked into your Android phone, so you should immediately take steps to remove the dangerous scripts.
Your first step should be to try to identify and remove the infected app before it can spread to your other linked devices and unfold its full damage potential. The following simple steps describe how to remove Android malware, including certain security software recommendations to help you protect your device in the future.
- Shut down your device
If you are certain that your Android device has fallen victim to a malware attack, you should try to switch it off immediately by holding the power button down for a few seconds until the phone is fully off. This step should prevent the malware from accessing other nearby networks or devices connected to your own network. Next, you should do your research and try to find out which specific app that you recently downloaded could have infected your Android phone. If you cannot think of anything suspicious, then use another computer to check your symptoms on the Internet. Make also a list of all new apps that you have recently installed and look them all up one by one for security issues, maybe this way you can narrow down your search and find out which app caused the issue. Remember, if you cannot find out which app brought the malware to your system, you cannot remove it.
If, however, your research is in vain, you can turn your device back on and skip to step 4. Installing an anti-malware program could help you identify the problem, and possibly even clean up your phone from the malicious application. That will require connecting your phone to the Internet again, which involves additional risks.
- Switch your phone to emergency/safe mode while you are using it
In order to limit the damage that the infected app can cause to your device, you should switch over to safe mode before you turn your phone back on and start searching for the infected app. To access the safe mode of your Android device, press and hold the power button for a few seconds, then tap and hold the "power off" option. This should bring up to your screen the option to "reboot to safe mode," along with a list of several other options. Choose the safe mode option and then let your phone reboot. In case you cannot find the safe mode option, just activate the airplane mode - that will do the job as well as it will cut your device off from any networks.
Note, that if a ransomware threat has hijacked your Android device, most likely all of these actions will be blocked and you will not have access to them. In that case, you should not waste your time but contact a professional as soon as possible.
- Find and delete the suspicious app on your device
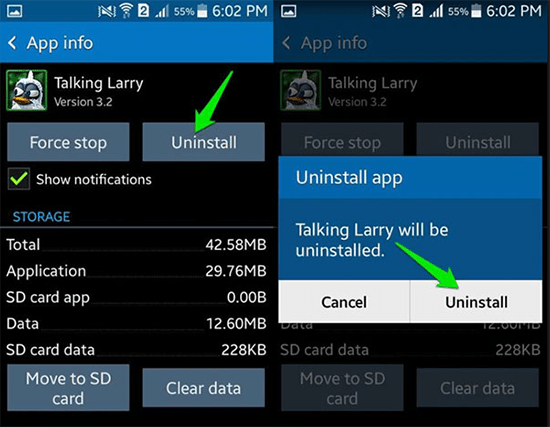
The next step includes finding the problematic application. To do this, you need to open the "Settings" menu on your Android device. It is typically represented through a gear-shaped icon, but it could also have a different appearance depending on any personalization themes. After opening the "Settings" menu, scroll down all the options until you find the section called "Apps." When clicking on it, you should get a list of all applications currently installed on your phone. Otherwise, you may need to open "App Manager" in order to see the full list. From the apps list, locate and select the infected app, then choose the "Uninstall" or the "Force close" option. When completed, this action should remove the application that is causing the problems on your device.
Removing and Uninstalling an Android App
Also, go carefully through the entire list to look for other suspicious downloads - you may notice weird apps that you did not even know you have on your phone, or you cannot remember having installed. These could also be a source of trouble, potentially hiding some malware threats, so check out on the Internet anything that does not look familiar to you.
In some cases, however, you may not be able to uninstall the desired app because the "Uninstall" will not be available. Instead, a "Disable" option will be displayed. This happens, because some of the most sophisticated malware, like ransomware, for example, have the capability to access your administrator settings and acquire special protection so that users cannot delete them in the normal way. No worries, though, that can be fixed as well. In the original "Settings" menu, scroll down to "Lock Screen and Security" and find there a section named "Phone/Device Administrators" ( in some Android devices, you may need to open the "Other security settings" option first), where you can allow the option to remove the malicious apps.
- Install reliable malware protection on your Android device
After you have manually removed the malware, or any other potentially harmful applications, from your Android device, you can take the final steps towards future infections. Various security programs are available on the market that can help you protect your phone, scan for viruses, and clean your device from any malicious apps. Search on the Internet and in Google Play Store for anti-malware software with high ratings, or ask an expert for recommendations.
Lastly, another important thing is always to keep your Android device up-to-date, because an outdated operating system is a major factor that can leave your phone vulnerable to cyber attacks.