HOOK Android Malware Variant
Cybersecurity researchers have identified a new variant of the Android banking trojan known as HOOK, now featuring ransomware-style overlays designed to extort victims. This marks a significant evolution in its capabilities, pushing it beyond traditional banking malware.
Table of Contents
Ransomware-Style Overlay Extortion
One of the most striking additions in the latest variant is its ability to deploy a full-screen ransomware overlay. This overlay displays a threatening 'WARNING' message, accompanied by a dynamically retrieved wallet address and ransom amount from the command-and-control (C2) server.
The extortion screen is remotely triggered when the C2 server sends the 'ransome' command and can be dismissed when the attacker issues the 'delete_ransome' instruction.
Roots in ERMAC Banking Trojan
HOOK is considered a direct offshoot of the ERMAC banking trojan, whose source code was previously leaked online. Much like ERMAC, HOOK relies heavily on Android's accessibility services and fraudulent overlay screens to steal credentials, automate financial fraud, and seize control of infected devices.
Advanced Espionage and Exploitation Features
Beyond credential theft, HOOK boasts a variety of intrusive features. It can:
- Send SMS messages to attacker-controlled numbers.
- Stream a live feed of the victim's screen.
- Capture images using the front-facing camera.
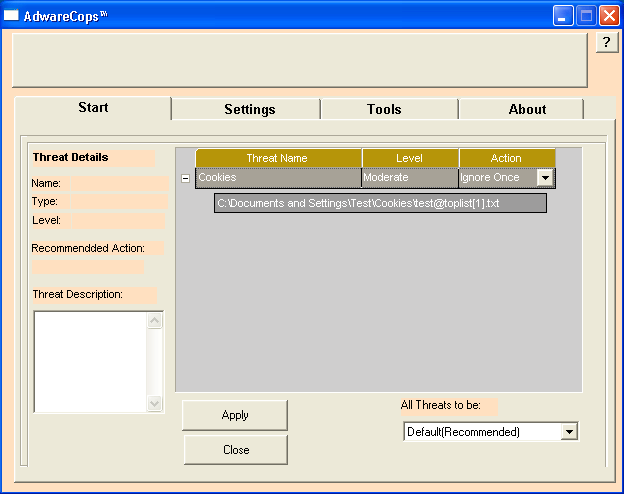
- Steal cookies and recovery phrases linked to cryptocurrency wallets.
These functions highlight HOOK's convergence with spyware capabilities, giving attackers broad surveillance and theft options.
Expansion of Remote Commands
The latest version of HOOK supports 107 remote commands, with 38 newly added capabilities. These enhance its ability to deceive users and harvest sensitive data.
Some of the most notable new commands include:
- ransome – Displays a ransomware-style overlay on the device
- delete_ransome – Removes the ransomware overlay
- takenfc – Shows a fake NFC scanning screen to capture card data
- unlock_pin – Presents a fake unlock screen to steal device PINs or patterns
- takencard – Mimics Google Pay to phish for credit card details
- start_record_gesture – Uses a transparent overlay to record user gestures
Large-Scale Distribution Channels
Researchers have traced HOOK's distribution to phishing websites and fraudulent GitHub repositories hosting malicious APK files. The use of GitHub for malware distribution is not new, families such as ERMAC and Brokewell have also been spread via the platform, demonstrating its growing popularity among threat actors.
Blurring the Line Between Malware Categories
The rapid evolution of HOOK reflects a troubling trend in mobile threats: the convergence of banking trojans, spyware, and ransomware techniques. By constantly expanding its features and spreading through large-scale campaigns, HOOK poses an escalating risk to financial institutions, enterprises, and everyday Android users.