Hijacker.StartPage.KS
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 18,375 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 775 |
| First Seen: | August 3, 2012 |
| Last Seen: | November 24, 2025 |
| OS(es) Affected: | Windows |
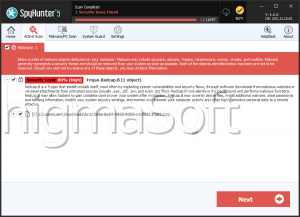
Hijacker.StartPage.KS is a malicious browser hijacker that PC security analysts have ranked as the third most common home network infection of 2012. Hijacker.StartPage.KS is associated with malicious browser toolbars and is designed to change a web browser's homepage and default search engine. If you find that your web browser's starting page has been changed without your authorization, it is very likely that your machine has become infected with threats similar to Hijacker.StartPage.KS. One symptom of Hijacker.StartPage.KS is that even if you try to change your hijacked homepage, Hijacker.StartPage.KS will change it again every time the affected web browser is launched.
Table of Contents
How the Hijacker.StartPage.KS Malware Infection Works
ESG malware analysts have observed that Hijacker.StartPage.KS-related browser redirects take computer users to websites that are set up explicitly to gather sensitive data and generate advertising revenue. Hijacker.StartPage.KS makes changes to the infected computer's Windows Registry, ensuring that Hijacker.StartPage.KS starts up automatically and that Hijacker.StartPage.KS cannot be removed easily. Malicious toolbars associated with Hijacker.StartPage.KS usually cannot be removed through ordinary means and depend upon the use of boosted anti-malware application.
Taking a Look at Hijacker.StartPage.KS and Other 2012 Home Malware Threats
In the year 2012, nearly fifteen percent of all household networks are infected with malware similar to Hijacker.StartPage.KS. Most of the time, these kinds of malware infections will infiltrate the victim's computer through malicious spam email messages. These malicious email messages often contain dangerous embedded links or attached malware files. These malicious links or files take the victim to phishing websites or to legitimate websites that have been hacked in order to make it attack computer users. Although Hijacker.StartPage.KS is not considered a high-level malware threat, Hijacker.StartPage.KS will seldom attack alone. In fact, most Hijacker.StartPage.KS infection will involve very high-level malware components such as the Alueron or ZeroAccess rootkits. Becase of this, malware like Hijacker.StartPage.KS should not be allowed to remain on the infected computer.
Although it is possible to remove Hijacker.StartPage.KS manually, ESG security researchers do not advise doing this. Hijacker.StartPage.KS makes changes to the Windows Registry that must be inverted in order to remove this threat effectively. Since Hijacker.StartPage.KS will seldom infect a computer by itself, manual removal may also be problematic because of other malware threats and rootkits present on the compromised computer. On account of the fact that the bulk of Hijacker.StartPage.KS infections has appeared in 2012, it is important to keep your security software fully up to date.
Analysis Report
General information
| Family Name: | Adware.Elex.K |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
318bfae202954fc4eaf362e550f5db21
SHA1:
0b038cc6ff7b5302ad2ee57815d530c592b766b5
SHA256:
4D6C51808A75DA217201566905918C36923299AF2C075B16559599416067C0C2
File Size:
146.43 KB, 146432 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have security information
- File has exports table
- File is 64-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- dll
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 433 |
|---|---|
| Potentially Malicious Blocks: | 20 |
| Whitelisted Blocks: | 390 |
| Unknown Blocks: | 23 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|