Hidden-Tear.Gen Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 14,318 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 454 |
| First Seen: | May 22, 2017 |
| Last Seen: | February 24, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
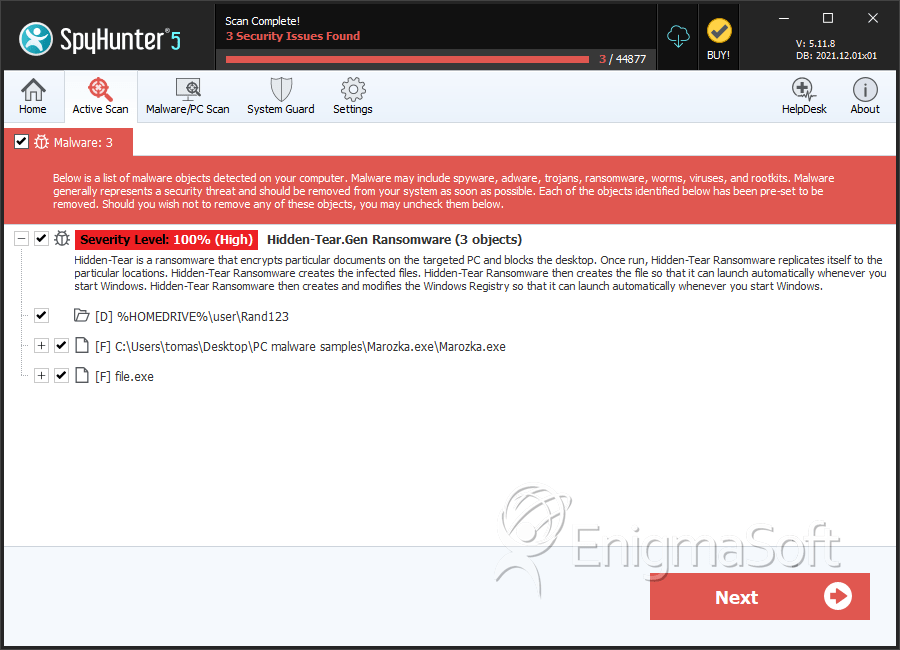
SpyHunter Detects & Remove Hidden-Tear.Gen Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Marozka.exe | 7b34f5ecb7c14244aaa6e330c620584a | 1 |
| 2. | file.exe | e1a88ddb222b48f55f5be7eb9ea9164e | 0 |
Registry Details
Directories
Hidden-Tear.Gen Ransomware may create the following directory or directories:
| %HOMEDRIVE%\user\Rand123 |
Analysis Report
General information
| Family Name: | Hidden-Tear.Gen Ransomware |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
76f7d852e1fab2295e4922a974d47caa
SHA1:
8691b22978a9b9110a332fa348b5f7aa64ecd489
SHA256:
9A1592CE558C00A19F816BAC310D99FB432EA0CBB3FAB540B02582CB12C46621
File Size:
595.24 KB, 595238 bytes
|
|
MD5:
f78eff4667708137132051ee4a976200
SHA1:
9e5f0bc15a8e630947cc5437e0b912b6c04f48e9
SHA256:
D2CC3CA1137F80635AFF3676F09B913D0FBD9A65FCF09B519C990C4CAE342E28
File Size:
1.05 MB, 1051136 bytes
|
|
MD5:
b19b4cb9e8443a5ca13b7dae8d2fb8b3
SHA1:
260714dcf6fbcedcdedf5918ce2583acf077606d
SHA256:
915078A6E0FE0A5C75A3AA5FCE2238F84CB9F3098D747C39F6556436279EAB7A
File Size:
818.69 KB, 818688 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is .NET application
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 0.0.0.0 |
| File Version |
|
| Internal Name |
|
| Original Filename |
|
| Product Name | Project1 |
| Product Version |
|
File Traits
- .NET
- dll
- RijndaelManaged
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,699 |
|---|---|
| Potentially Malicious Blocks: | 6 |
| Whitelisted Blocks: | 1,725 |
| Unknown Blocks: | 968 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|
| Syscall Use |
Show More
|
