GhostAdmin
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
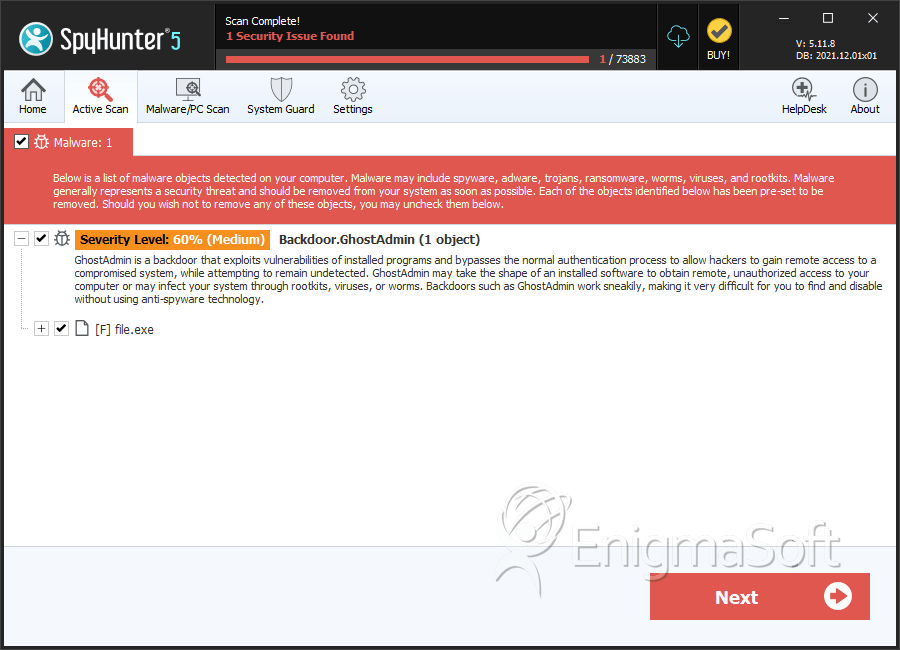
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 2 |
| First Seen: | January 18, 2017 |
| Last Seen: | May 13, 2020 |
| OS(es) Affected: | Windows |
GhostAdmin is a threat infection that is used to collect data and infiltrate the victims' computers. Third parties can take control of a computer infected with GhostAdmin. Commands can be sent to the infected computers by using IRC. GhostAdmin integrates the infected computers into a botnet, a vast network of infected computers that can then be used to carry out coordinated attacks, such as a sending out spam emails or carrying out DDoS (Distributed Denial of Service) attacks. GhostAdmin is already in active distribution and has been used in at least two attacks. GhostAdmin has already been used to collect large quantities of data from two businesses.
Table of Contents
The GhostAdmin Infection
Malware researchers have studied the GhostAdmin's code and have determined that is an updated version of CrimeScene, a botnet family that was active in 2012 and 2013. GhostAdmin is improved from this predecessor substantially, however. Currently, GhostAdmin is in version 2.0. GhostAdmin is written in C#. During its attack, GhostAdmin gains boot persistence, meaning that it remains active even if the infected computer restarts. It establishes communications with its command and control server through a particular IRC channel. The people controlling GhostAdmin can use this IRC channel to send commands that will be sent to all of the connected bots, a term used to refer to computers infected with the botnet threat.
What GhostAdmin can Do on an Infected computer
GhostAdmin can be used to interact with the infected computer's file system, copying, moving and deleting data. GhostAdmin also can browse the Web from the infected computer, download files and run them on the infected computer, and access the infected computer's history and settings. GhostAdmin also may be used to monitor the infected computer and is capable of taking screenshots, recording audio, and a wide variety of other functions. The main purpose for which GhostAdmin is being used currently is to collect data from the infected computers. These people gather data from the infected computer using GhostAdmin and then send this data to a Command and Control server using FTP to upload the data to a remote server. The FTP credentials are stored in GhostAdmin's configuration file, as well as an email address that is sent to contact the GhostAdmin's author.
Tracking GhostAdmin’s Origins
PC security analysts suspect that GhostAdmin was created by a user going by the name 'Jarad.' PC security researchers have managed to infiltrate the GhostAdmin's FTP server using the FTP credentials found in the GhostAdmin's configuration files, tracking information about Jarad's computer, as well as finding files taken from the GhostAdmin's victims. PC security researchers uncovered data collected in a lottery company and an Internet provider, from whom more than 360 GB of data had been gathered. GhostAdmin was used to collect a database containing information from the lottery company. At the time of this writing, GhostAdmin's IRC channel seems to have ten active bots only, which correspond to the current victims of this attack.
Most botnet families require thousands or even millions of bots to carry out effective attacks. This makes it obvious that GhostAdmin is just in its first steps. However, the fact that GhostAdmin's FTP credentials and other crucial data were able to be recovered from GhostAdmin's code makes it appear that Jarad is not a particularly sophisticated malware developer and, in fact, GhostAdmin does seem to be a step behind other, more advanced botnet threats in sophistication and potential of the attack. Regardless, PC security analysts strongly advise computer users to take precautions against GhostAdmin. It is important to install a reliable security program that is fully up-to-date and capable of detecting these threats.
SpyHunter Detects & Remove GhostAdmin
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 219ba2ee0bcdb23bf89079ac97730d57 | 1 |
| 2. | file.exe | b7cd29cfc8c2a3c26493c80ea0a6ffb6 | 0 |
| 3. | file.exe | 7a2a5b88b8331732e5bf0e0e1c6d54e8 | 0 |
| 4. | file.exe | 62c47ae826413abcf87df611d699ad6e | 0 |
| 5. | file.exe | 80efaf603cbc72e855457fc727b281af | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.