FormBook
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 28 |
| First Seen: | October 4, 2017 |
| Last Seen: | February 17, 2022 |
| OS(es) Affected: | Windows |
The FormBook malware is developed by a programmer who uses the handle 'ng-Coder' and offers access to a "FormBook Builder" software on various Dark Web forums and code sharing platforms. The FormBook malware became the talk of the cybersecurity community in October 2017 and was covered as part of the QuantLoader and the Panda Banker campaigns extensively. The cybercrooks are offered by 'ng-Coder' to buy their way into the "FormBook Builder," which is not distributed to machines locally. Customers are given access to a PHP control panel, which they use to create and download a customized version. Interested parties are welcomed to purchase a subscription for $29/week, $59/month, and $99/three months if they are interested in incorporating the FormBook into their operations. The FormBook payload can be packed as PDFs with download links, DOC, and XLS files with macros and archives with executable inside. Once the FormBook malware is introduced to a targeted device, it offers the following capabilities to its operators:
- Clear the browser's cookies.
- Clipboard grabbing.
- Collect passwords and emails from Outlook, Mozilla Thunderbird, Mozilla Firefox, Google Chrome and Internet Explorer.
- Download and execute files.
- Download and extract files from archives.
- Install updates to the bot.
- Keyboard input logging.
- Reboot & shut down the system.
- Record HTTP;HTTPS;SPDY;HTTP2 forms.
- Remove the bot from the infected device.
- Screenshot.
The FormBook Trojan includes abilities to make it harder for AV solutions to find the threat on the compromised system. Malware analysts alert that FormBook loads on startup via a hidden entry, uses standard Windows APIs, employs encrypted channels for C&C communications and includes a function that changes the file paths, file names, and extensions used during active periods. All these features make the FormBook Trojan hard to identify and an intriguing product on the Dark Web. The FormBook Trojan was launched within the South Korean cyberspace initially. However, we expect the FormBook Trojan to receive a lot of attention and spread throughout Asia, Europe and South America. You should make sure to run a trustworthy anti-malware suite that can identify and eliminate the FormBook threat. AV engines flag FormBook-related files as:
- DR/AutoIt.Gen
- Gen:Heur.Liusky.1
- RAR/Agent.CC
- Script.Trojan.Agent.DLEUTD
- TROJ_OTOFORM.A
- Trojan ( 005126601 )
- Trojan/Win32.AutoIt.C2181283
- W32/Injector.CZM!tr
Table of Contents
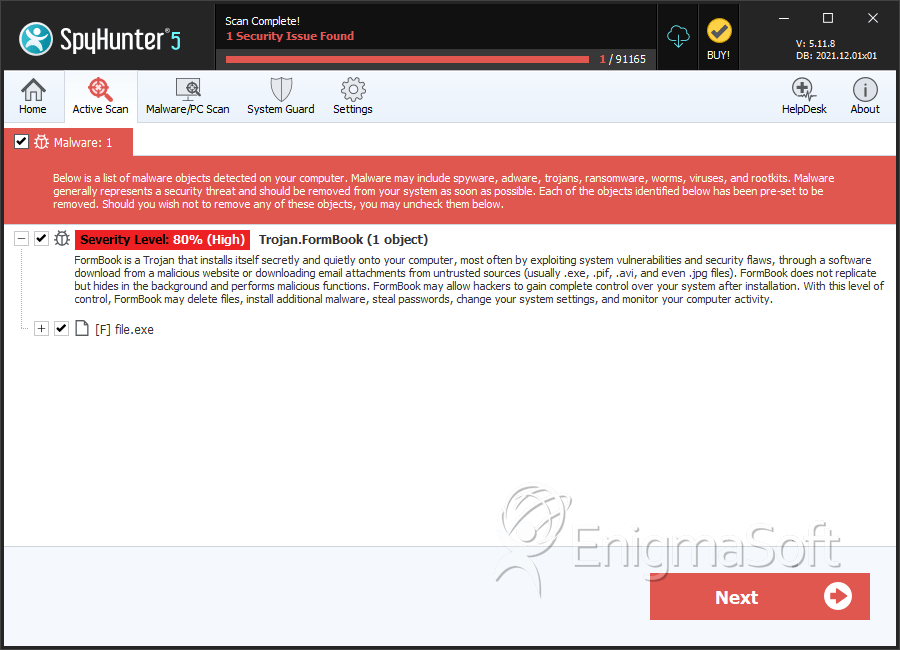
SpyHunter Detects & Remove FormBook
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 211b801cc175d75c6570ef784fa03025 | 2 |
| 2. | file.exe | ec7b972d6233995bf76d91030e71c111 | 2 |
| 3. | file.exe | 08d6ddcbcb89d0bc3545467ed8ac71f0 | 1 |
| 4. | file.exe | 027749b3b4fbd2fc44dbe50e65cf3765 | 1 |
| 5. | file.exe | 653922d5e914eb7e6d906a083d930e29 | 0 |
| 6. | file.exe | d6c41a1f2e15889849747f0aa1772a20 | 0 |
| 7. | file.exe | 0fac516e1a47d43be56599c17ac1aa0a | 0 |
| 8. | file.exe | 869356c3b8fa73dd2dc5ee5ee584d7e3 | 0 |
| 9. | file.exe | 49a8d93dd6280f7197b094c359d785cb | 0 |
| 10. | file.exe | 423e35ab50cd115760cae05cfdedbe60 | 0 |
| 11. | file.exe | e2e47c3ab5643fe179baf5241e09dc40 | 0 |
| 12. | file.exe | 27097f447e01e3d7be9c16d87fd5559d | 0 |
| 13. | file.exe | 0692d69cd44ac2badbbfd0e98176f23a | 0 |
| 14. | file.exe | 01a43ab570cfe7f8a271ea3e76cf8ef1 | 0 |
| 15. | file.exe | 2055df8d5e156dd222ea5307baaa3329 | 0 |
| 16. | file.exe | 56edae07a8c9f4fc73346af43170e6dd | 0 |

