Fobber
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 81 |
| First Seen: | June 25, 2015 |
| Last Seen: | May 2, 2022 |
| OS(es) Affected: | Windows |
Malware researchers classify the Fobber cyber threat as a trojan that is used by cybercriminals to obtain log-in details for social media and online banking portals. You may be interested to know that the Fobber trojan is an updated and modified version of the Tinba malware that fills the same niche of harmful programs. The Fobber trojan is distributed via exploit kits such as the HanJuan Exploit Kit and could be introduced to your computer by a trojan downloader like Ajuxery and Drepitt. The Fobber trojan is written with the purpose of monitoring your web traffic and recording your user credentials when you type them onto the log-in page. The Fobber trojan executes man-in-the-middle (MITM for short) attacks that can allow cybercriminals to hijack your social media account and purchase goods on online stores by using your credit card number. Also, the Fobber trojan may start a background service in the Windows Task Manager to hide its operations. Malware researchers note that the Fobber trojan could be found in the Application Data folder, and users should not try to remove it manually because it may contain links to an auto-restore module in the Temp folder. Users who detect the Fobber trojan on their computer should seek the help of a trusted anti-malware solution that can delete the Fobber binary. Additionally, you should change your passwords for all of your accounts to avoid security issues.
Fobber
Table of Contents
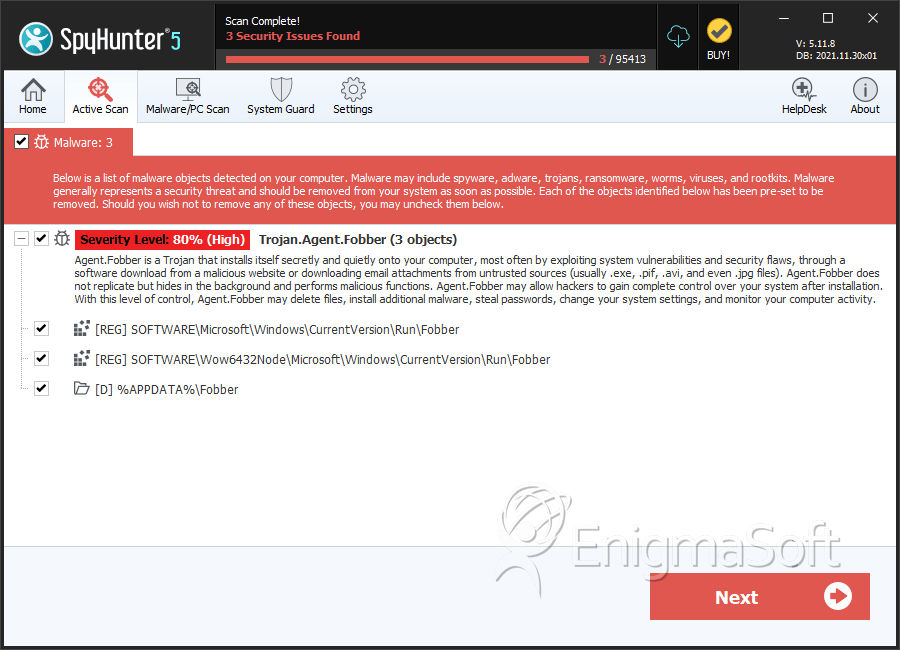
SpyHunter Detects & Remove Fobber
Registry Details
Directories
Fobber may create the following directory or directories:
| %APPDATA%\Fobber |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.