FindSearchEngineResults.com
FindSearchEngineResults.com Image
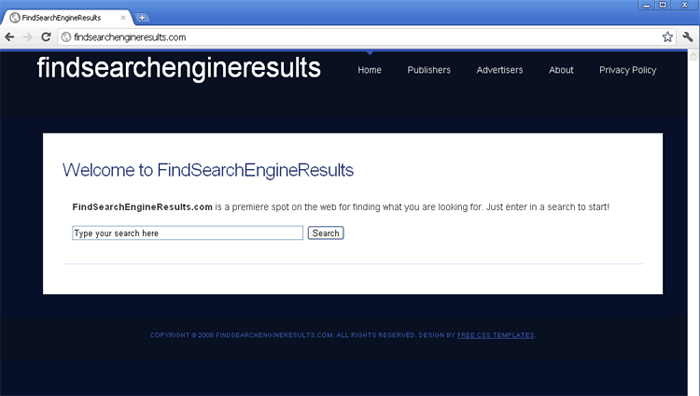
FindSearchEngineResults.com is a fairly simply website that gives off the appearance of being a search engine. However, FindSearchEngineResults.com has absolutely no real search capabilities. In fact, trying out a search on the FindSearchEngineResults.com search bar will simply result in a long list of advertisements, websites that are nothing but links and advertisements and results that are in no way relevant to the search carried out by the computer user. So, why would anyone want to use FindSearchEngineResults.com when there are reliable alternatives online such as Google, Yahoo or Bing? This is where the main danger of FindSearchEngineResults.com manifests itself. The fact is that most people visiting FindSearchEngineResults.com have absolutely no choice in the matter. This is because FindSearchEngineResults.com will usually be introduced aggressively by a browser hijacker on the victim's computer system. A browser hijacker will hijack the victim's web browser and force it to visit FindSearchEngineResults.com repeatedly, as well as carrying out other malicious tasks in order to ensure that the victim ends up at the FindSearchEngineResults.com website as often as possible. If you find that your web browser is compelling you to go to FindSearchEngineResults.com contrary to your will, this is a sure sign of a dangerous malware infection on your computer system. Use a reliable anti-malware application to hunt down browser hijackers on your hard drive and to stop all redirects to FindSearchEngineResults.com.
Criminals do not use browser hijackers to force you to visit FindSearchEngineResults.com repeatedly for fun or simply to mess with your head. Rather, they do it so that they can profit from the vast amounts of traffic that can be artificially generated with the help of these malware infections. While most users would normally have absolutely no interest in using FindSearchEngineResults.com for their online searches, infecting as many computer users with a browser hijacker ensures a constant, artificially-generated stream of visitors arriving at the FindSearchEngineResults.com web page every day. This web traffic translates into advertising revenue and revenue generated from pay-per-click schemes. If you do not want criminals to profit from infecting your computer system with browser-hijackers, make sure that you protect your machine with a reliable security tool, a firewall and other security software. Also, make sure to follow basic online safety guidelines while browsing the Internet.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%[trojan name]toolbarcouponsmerchants2.xml | |
| 2. | %AppData%[trojan name]toolbarcouponsmerchants.xml | |
| 3. | %AppData%[trojan name]toolbarguid.dat | |
| 4. | %AppData%[trojan name]toolbaruninstallStatIE.dat | |
| 5. | %AppData%[trojan name]toolbarversion.xml | |
| 6. | %AppData%[trojan name]toolbarcouponscategories.xml | |
| 7. | %AppData%[trojan name]toolbarstat.log | |
| 8. | %AppData%[trojan name]toolbaruninstallIE.dat | |
| 9. | %Temp%[trojan name]toolbar-manifest.xml | |
| 10. | %AppData%[trojan name]toolbardtx.ini | |
| 11. | %AppData%[trojan name]toolbarpreferences.dat | |
| 12. | %AppData%[trojan name]toolbarstats.dat | |
| 13. | %AppData%[trojan name]toolbarlog.txt |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.