Dominus Ransomware
Protecting computers and mobile devices from malware has become essential in an era where cybercriminal groups increasingly target personal files, business records, and sensitive data. A single infection can interrupt daily operations, cause financial losses, and expose private information. One threat that highlights these risks is Dominus Ransomware, a file-encrypting malware strain designed to extort victims through fear, urgency, and data exposure.
Table of Contents
A Closer Look at Dominus Ransomware
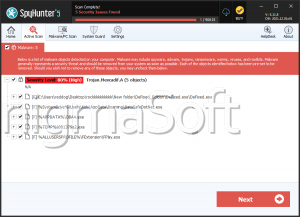
Dominus is a ransomware family identified by security researchers as a serious extortion threat. Its primary objective is to encrypt files on an infected machine and pressure the victim into paying for a decryption tool. In addition to locking files, Dominus claims to steal confidential information before encryption begins. This tactic is intended to increase pressure by threatening public leaks or third-party sales of the stolen data.
After execution, Dominus targets multiple file types and appends a modified extension, such as '.dominus27' to affected files. Variants may use different digits, but the naming pattern remains similar. For example, a file originally named '1.png' may become '1.png.dominus27,' while '2.pdf' may be renamed '2.pdf.dominus27.' Once encryption is complete, the malware drops an HTML ransom note named 'RANSOM_NOTE.html.'
The Extortion Strategy Behind the Attack
The ransom note opens in a web browser and informs victims that their files have been encrypted. It also states that highly sensitive personal data has allegedly been collected and stored on a private server. According to the attackers, payment will result in file recovery and destruction of the stolen data. If the victim refuses, the criminals threaten to publish or sell the information.
Victims are instructed to contact the attackers through the email addresses 'stevensfalls@outlook.com' or 'richardfeuell@outlook.com'. The note even recommends creating a ProtonMail account before initiating contact. To appear credible, the operators offer to decrypt two or three unimportant files for free. A countdown warning claims that the ransom price will rise if contact is not made within 72 hours.
This model is known as double extortion. The victim faces two simultaneous threats: loss of access to files and exposure of private data. Even when backups exist, the fear of reputational damage or leaked records can be used to coerce payment.
Why Paying the Ransom Is Risky
Paying cybercriminals does not guarantee recovery. Attackers frequently disappear after receiving funds, demand additional payments, or provide tools that fail to decrypt the files properly. There is no trustworthy enforcement mechanism, contract, or customer support system in ransomware operations.
Payment also helps finance future attacks, allowing threat actors to improve infrastructure, recruit partners, and target more victims. For these reasons, security professionals generally advise focusing on containment, forensic investigation, restoration from clean backups, and legal or incident response procedures instead of rewarding the attackers.
How Dominus Commonly Reaches Victims
Like many ransomware strains, Dominus often relies on social engineering and unsafe software sources to gain access. Common infection routes include:
- Malicious email attachments or links disguised as invoices, shipping notices, account alerts, or routine correspondence.
- Trojans, cracked software, fake updates, malicious ads, peer-to-peer downloads, and files from unofficial hosting websites.
Some campaigns may also exploit users through deceptive advertisements that trigger downloads with minimal or no interaction.
Best Security Practices to Strengthen Malware Defense
Strong cybersecurity hygiene remains the most effective defense against ransomware. Devices should always run reputable security software with real-time protection enabled, and operating systems must be updated promptly to close known vulnerabilities. Outdated software is one of the easiest entry points for attackers.
Regular backups are equally important. Copies of critical files should be stored offline or in secure cloud environments that cannot be directly altered by malware running on the primary device. Testing backups periodically ensures that restoration will work during an emergency.
Email caution is another major safeguard. Unexpected attachments, urgent payment requests, password reset messages, and suspicious links should be treated carefully, especially when they create pressure or demand immediate action. Verifying the sender through a separate communication channel can prevent compromise.
Strong passwords and multi-factor authentication help reduce unauthorized access. Administrative privileges should be limited so that daily-use accounts cannot make unrestricted system changes. Network segmentation in business environments can also stop ransomware from spreading across multiple machines.
Finally, software should only be downloaded from official vendors and trusted marketplaces. Pirated programs, activation cracks, and fake installers are common malware delivery tools. Avoiding these sources significantly lowers exposure to ransomware threats like Dominus.
Final Assessment
Dominus Ransomware demonstrates how modern cybercrime has evolved beyond simple file locking into psychological and data-driven extortion. By encrypting files, renaming them with extensions such as '.dominus27,' and threatening to leak stolen information, the attackers attempt to maximize pressure on victims. The strongest response remains prevention: layered security controls, cautious online behavior, dependable backups, and fast incident response planning.