Default-Search.net
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 1,307 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 266,425 |
| First Seen: | May 2, 2014 |
| Last Seen: | April 12, 2026 |
| OS(es) Affected: | Windows |
Default-Search.net is a low-grade search engine that has been correlated with Potentially Unwanted Program infections. Default-Search.net is linked to Web browser redirects, changes to affected Web browser settings and a large number of other threat-like behaviors on affected computers. If your computer is presenting symptoms associated with Default-Search.net, security researchers strongly advise the removal of any PUPs installed on your computer. PUPs associated with Default-Search.net are usually bundled with low quality freeware. Because of this, you can prevent the installation of PUPs associated with Default-Search.net by guarding the installation process of any new software carefully. In most cases, choosing custom installation and only selecting necessary components to be installed can prevent the installation of these types of unwanted components.
Table of Contents
Common Issues Associated with Default-Search.net
There have been observed a wide number of issues related to Default-Search.net and its associated PUPs. If your Web browser is presenting any of the following symptoms, this may indicate that a PUP associated with Default-Search.net has been installed on your computer:
- PUPs associated with Default-Search.net may change the affected Web browser's homepage, default search engine and default new tab or window website to Default-Search.net.
- PUPs linked to Default-Search.net may display pop-up windows and other types of pop-up advertisements associated with Default-Search.net. These pop-ups may appear quite frequently, seriously interfering with computer users' activities on affected Web browsers. Default-Search.net has also been linked to banner advertisements, in-text marketing advertisements and other forms of intrusive advertising.
- PUPs associated with Default-Search.net may take over the affected Web browser, forcing it to visit Default-Search.net repeatedly. Default-Search.net redirects may be quite disruptive, interrupting affected computer users' activities frequently.
Aliases
4 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| McAfee | Artemis!A392180ACD34 |
| McAfee | Artemis!6C0E99A88F43 |
| AVG | Toolbar.SearchSuite |
| Fortinet | Riskware/Toolbar_SearchSuite |
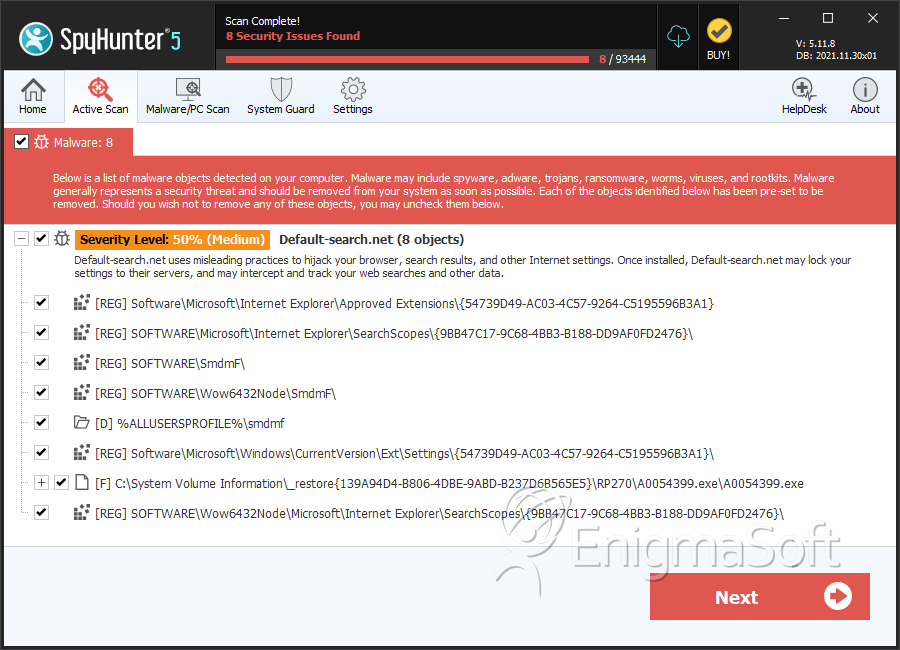
SpyHunter Detects & Remove Default-Search.net
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | $R7LROA4.cfg | 7e1c1b7e7c427d8ba44b133761cb2192 | 4,971 |
| 2. | A0054399.exe | 4c6a302490db9b796c9db8c1e90421f3 | 3,713 |
| 3. | smdmfmgrc3.cfg.vir | 5f4e2340edce27b6eaca191509f20f67 | 3,105 |
| 4. | smdmfmgrc2.cfg.vir | 981c2858ebf6192c785d303dc509335f | 1,444 |
| 5. | smdmfmgrc3.cfg | a9f348403170fece9f72def38d3522f4 | 1,030 |
| 6. | smdmfmgrc2.cfg | 3f0312e1d2fdfd5859b3aa2d7464a7f6 | 862 |
| 7. | smdmfmgrc2.cfg.173809.gzquar | 53d67b57b046b2cccb12a4a436e4ef89 | 472 |
| 8. | SystemkService.exe | a392180acd34edc3680a4fa13991870b | 342 |
| 9. | systemkmgrc1.cfg.vir | eefda207e341fb04ba6b31780db51782 | 306 |
| 10. | OldCoordinator_nsr3EF.exe | 2c8d11ecf064685ebc4d351fa4349c91 | 125 |
| 11. | SystemkService.exe.vir | 94b263fde2babc554166b948185f33ab | 124 |
| 12. | systemku.exe | debaba91bd2dbf83a671a2d89dfe0bf1 | 82 |
| 13. | OldCoordinator_nsv7C27.exe | 05fa869b004082417be1441fec20daf5 | 30 |
| 14. | Systemkey.exe | 49fb644bb0ee23cda11c0d96d32c45b5 | 20 |
| 15. | tbicon.exe | 3261c97eeac15368c9a5d5ab193593f2 | 20 |
| 16. | syskldr.dll | 37bde04482447b938e70c36f9aaf79fe | 10 |
| 17. | Internet Explorer Settings.exe | c4eed641e19e676d3050a8052558d142 | 8 |
| 18. | A0054395.dll | 7b3585c97afabd24fb0a5bfb865f388b | 7 |
| 19. | syskldr.dll | 90aeb99323361cf86e1647691f231fec | 2 |
| 20. | Uninstall.exe | c44da1bdd949d8941674ce66d72c102c | 2 |
Registry Details
Directories
Default-Search.net may create the following directory or directories:
| %ALLUSERSPROFILE%\Application Data\smdmf |
| %ALLUSERSPROFILE%\Application Data\systemk |
| %ALLUSERSPROFILE%\smdmf |
| %ALLUSERSPROFILE%\systemk |
| %AppData%\FirefoxToolbar\Settings Manager\smdmf |
| %PROGRAMFILES%\Assets Manager\smdmf |
| %PROGRAMFILES%\Settings Manager\smdmf |
| %PROGRAMFILES%\Settings Manager\systemk |
| %PROGRAMFILES(x86)%\Settings Manager\systemk |
URLs
Default-Search.net may call the following URLs:
| default-search.net |
Analysis Report
General information
| Family Name: | Default-search.net |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
2a9818a11001fa9101c5d2c178e5e3a9
SHA1:
f711aedf127201e611ce3fd57d63c4a73feada12
SHA256:
4F7D45FBACED429C292A062369DE812655651EFA45659C42D624905F56223CFB
File Size:
8.72 MB, 8718440 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Aztec Media Inc |
| File Description | Settings Manager Install |
| File Version | 5.0.0.14682 |
| Legal Copyright | Copyright (c) 2005 - 2014 |
| Product Name | SettingsManager |
| Product Version | 5.0.0.14682 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| AZTEC MEDIA INC. | Thawte Code Signing CA - G2 | Self Signed |
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nsma786.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
