Datper
Datper is a backdoor Trojan. These threats allow criminals to gain access to the victims' computers. Datper was reported in November 2018 in association with attacks linked to a criminal group that has been known as 'Tick' mainly. Tick has been active since 2016 and has gained notoriety for developing several threats and hacking tools. Datper is being used in attacks by this criminal group on targets located in South Korea and Japan. Various websites in these two countries have been found to be compromised by Datper already. The Datper attacks seemed to be based out of China.
Table of Contents
How Datper Works
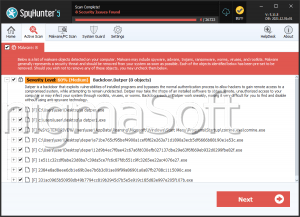
Once Datper is installed on the victim's computer, Datper allows criminals to run commands on the infected device. Datper also allows the attacker to gain information about the affected computer. Using Datper, criminals can install other malware or collect data stored on the targeted device directly. Essentially, threats like Datper allow criminals to gain control of the targeted device, which can then be translated into other ways of making money or carrying out other attacks. It is possible that Datper attacks are part of a service being provided by these criminals to other criminal groups, where they will lease out malware services to allow third parties to carry out attacks. Threats like Datper should be prevented by including a strong security program and security measures, as well as backup copies of all data stored on a separate location.
Detailing the Work of Threats Like Datper and the Tick Group
Tick has been known by other names, including 'Redbaldknight' and 'Bronze Butler.' This group, based in China, has been carrying out attacks on South Korean and Japanese targets for several years, at least since 2016. Many of the attacks that Tick has carried out are espionage attacks, used to collect sensitive data and gain important intelligence about the victims. Datper is just one of the many backdoor Trojan families that the criminals associated with this attack have used to carry out attacks on their targets. Although Datper can be distributed in several ways, it is still unknown how the criminals are carrying out the attacks exactly. The most common methods for distributing threats like Datper are through corrupted email attachments and exploit kits located on compromised websites. Tick has compromised various servers located in South Korea and Japan and has used them as Command and Control servers. Examples of websites hijacked by Tick include a legitimate laundry service website located in South Korea, where vulnerabilities in the servers' security allowed the criminals to take it over to host their attacks.
Other Campaigns Associated with Tick and the Makers of Datper
The most high-profile attacks associated with this criminal group have targeted defense companies in South Korea, making it possible that Tick is a state-sponsored group, with considerable resources. In this previous attack, there was an attempt to gain access to classified information that would have made it possible to carry out attacks on targets in the defense industry and military. Tick has been responsible for other malware families emerging beside Datper. One of the most high-profile threats developed by Tick is known as SymonLoader, a threat designed to target outdated versions of Windows that is capable of spreading via USB drives.
Protecting Yourself from Tick and Datper
Tick and Dapter attack quarry high-end targets and are involved in industrial and commercial espionage. Because of this, typical computer users do not have much to fear. However, the tools they develop will invariably, be used by run-of-the-mill criminals eventually, making it important to ensure that you are protected.