Danti
Danti is the name of a hacking group that is likely to originate from China, but this is yet to be confirmed. The activity of the Danti group was first spotted in 2016. Ever since then, the Danti hacking group has not been very active. The Danti group shares some infrastructure and hacking tools with several infamous APTs (Advanced Persistent Threats) from China, which is why it is being speculated that the individuals behind this operation may be of Chinese origin.
The activity of this hacking group appears to be concentrated in Kazakhstan, Uzbekistan, the Philippines, Myanmar and Nepal mainly. Most of the Danti group’s campaigns appear to be motivated politically. The majority of the targets of the Danti hacking group are either political movements or high-ranking government officials. The Danti group uses both publicly available hacking tools and custom-built threats in their reconnaissance campaigns. Malware analysts believe that most of the Danti group’s operations aimed at stealing sensitive or classified data.
Spear phishing emails appear to be the preferred propagation method by the Danti hacking group. The bogus emails would contain a corrupted attached file that would contain the payload of the threat. According to reports, the early campaigns of the Danti group would utilize the CVE-2015-2545 vulnerability. This vulnerability allows EPS files to execute code on the targeted system. However, malware researchers believe that the Danti group has likely expanded their hacking arsenal, as well as located other vulnerabilities since.
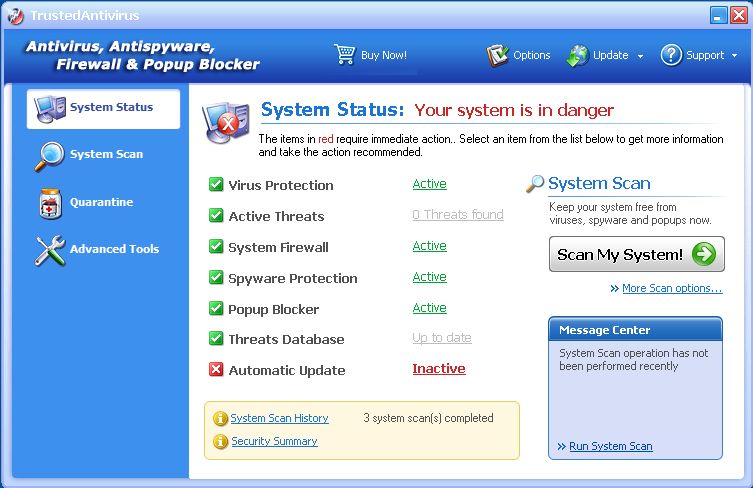
Businesses and other organizations need to take cybersecurity seriously, as dodgy individuals like the members of the Danti hacking group are always looking for ways to exploit them. It is important to invest in a legitimate anti-virus software suite that will protect your computer and your data from cybercriminals like the Danti hacking group.