Crimson Rat
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 51 |
| First Seen: | August 9, 2016 |
| Last Seen: | February 19, 2022 |
| OS(es) Affected: | Windows |
Trojan.CrimsonRat is a detection name used by cybersecurity vendors in regards to a Remote Access Trojan that is known to run as 'winservice.exe' on compromised systems. The Trojan.CrimsonRat malware is written in the Java programming language, and it is a cross-platform program that supports a Web access panel. Ironically, the payload of the Trojan is seen to arrive on systems as a file named 'securetyscan.exe,' which users may be lead to believe is a recommended security product. Hence, the UAC (User Account Control) prompt that appears during installation is not likely to raise suspicion. The Trojan.CrimsonRat is known to register a background service named 'winservice.exe' and allow a threat actor to modify and delete files on the compromised PC. Additionally, threat actors can use the CrimsonRat Trojan to download and run secondary threats on the infected machines.
The CrimsonRat Trojan is reported of attempting to suppress security alerts from several AV utilities and limit their capabilities. The first wave of attacks facilitated by the CrimsonRat Trojan was registered in Germany, but the 'Command and Control' server configuration revealed the threat actors are likely to be based in Sweden. Trojan.CrimsonRat is recorded to exchange data with the 5.189.167.65 IP address over port 12010, which is used to handle standard TCP/UDP connections. The Trojan.CrimsonRat malware is observed to report the compromised user's OS version, IP address, country of origin, keyboard layout, and a compiled list of installed software. The information may be used as a reference when the CrimsonRat operators decide to take advantage of the compromised device or sell the backdoor access to the PC via markets in the Dark Web. PC users who may have fallen a victim of the CrimsonRat malware may notice missing files, unfamiliar programs running in the background, and their AV scanner being unresponsive. It is best that you run a complete system scan with a reliable anti-spyware scanner that can detect and eliminate Trojan.CrimsonRat securely. AVs support rules designed to block the CrimsonRat from being installed. The alerts related to the CrimsonRat activation might offer the following detection names:
- RDN/Generic PWS.y
- Spyware ( 004f5c9a1 )
- TROJ_GEN.R047C0PHH16
- Trojan.Generic.17936439
- Trojan.Generic.D111B037
- TrojanAPT.MsoGen.J4
- Trojan[Spy]/Win32.Crimson
- W32/Crimson.AC!tr
- Win32.Trojan-spy.Crimson.Edxg
- a variant of MSIL/Spy.Keylogger.BNM
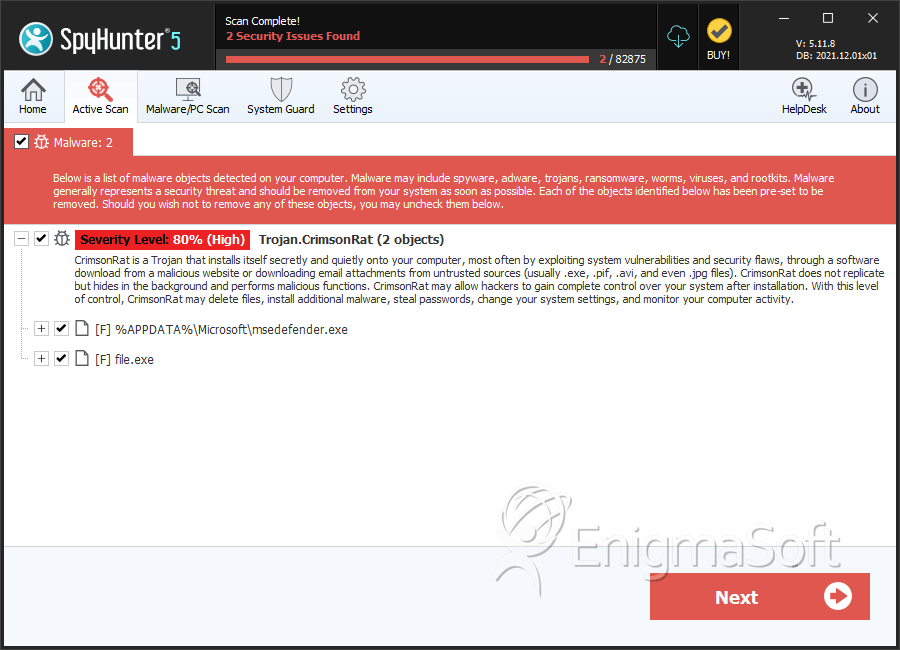
SpyHunter Detects & Remove Crimson Rat
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 363ceaf383cd5607e607fb89e1ae2131 | 18 |
| 2. | wintes.exe | 9363aa150eced079aa87ce3cc7de0c40 | 4 |
| 3. | file.exe | ead3940977d443b245d98b1fe3e9b7c2 | 1 |
| 4. | msedefender.exe | fcb6cb14e07575b91033cbc01915eb2a | 0 |
| 5. | file.exe | a1986e69d9581e112c6a51952a27279a | 0 |
| 6. | file.exe | 4ae93c1da934873f7829a6927d8e5b81 | 0 |
| 7. | file.exe | 9818c16c5e8da3419909260291925572 | 0 |

